#1
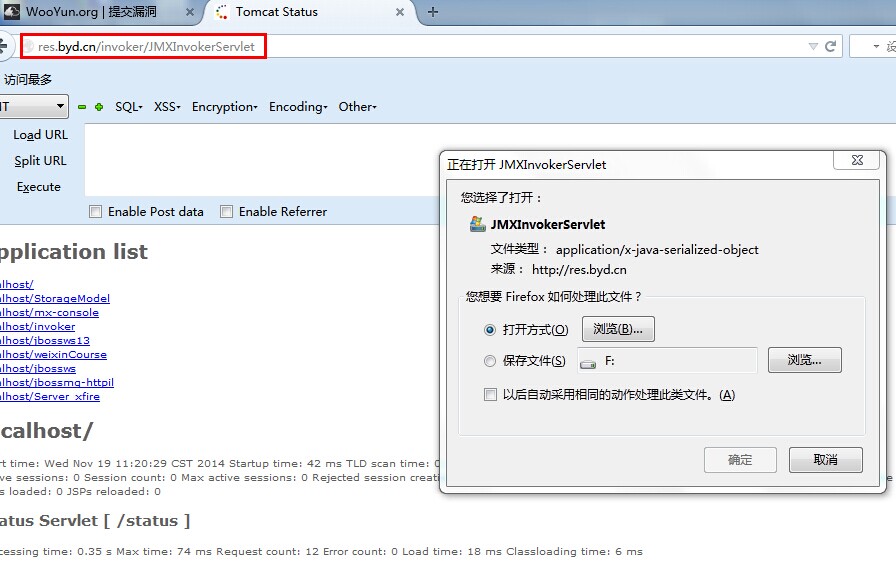
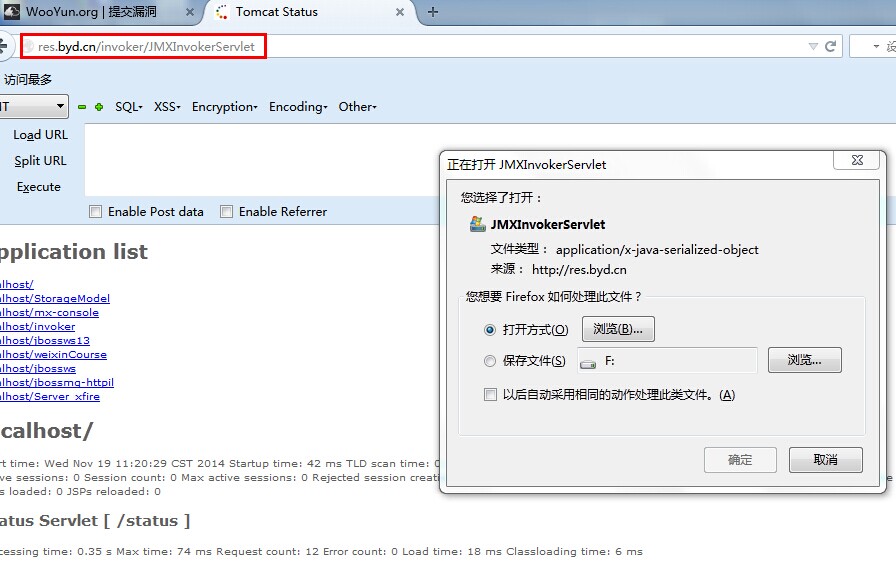
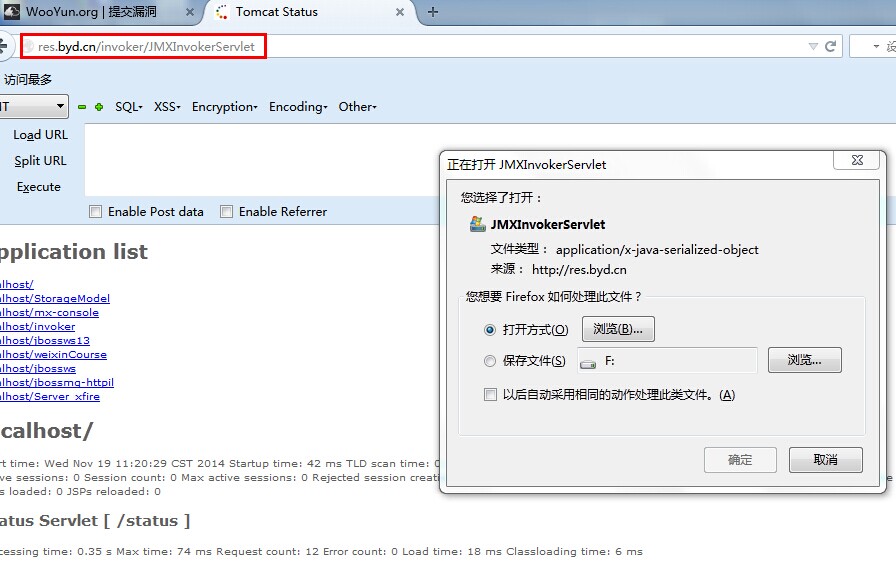
发现漏洞
站点:res.byd.cn/invoker/JMXInvokerServlet
直接getshell
#2
福利出现
但在getshell过程中发现:
站点:http://res.byd.cn/jbossws13/
返回:it works! Linux 2.6.18-194.el5 i386 ->||<-
很明显已有前辈进来过。
查看shell密码得心中暗喜,gainover~~~~~~~~~~~~~~
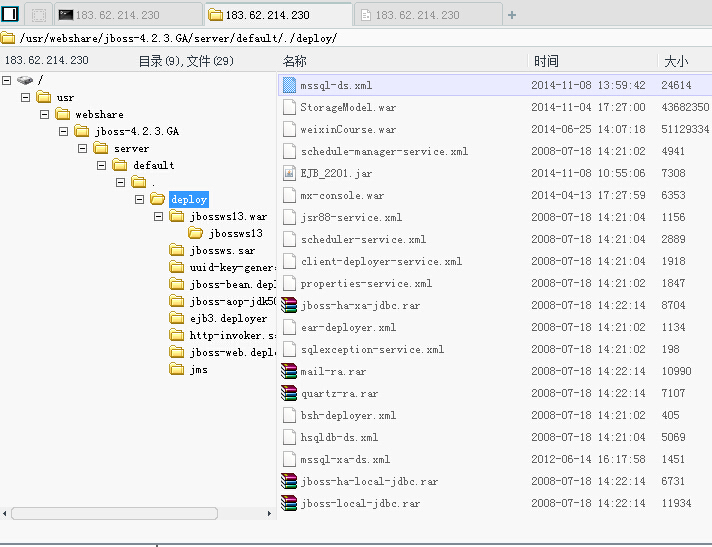
#4
来点图
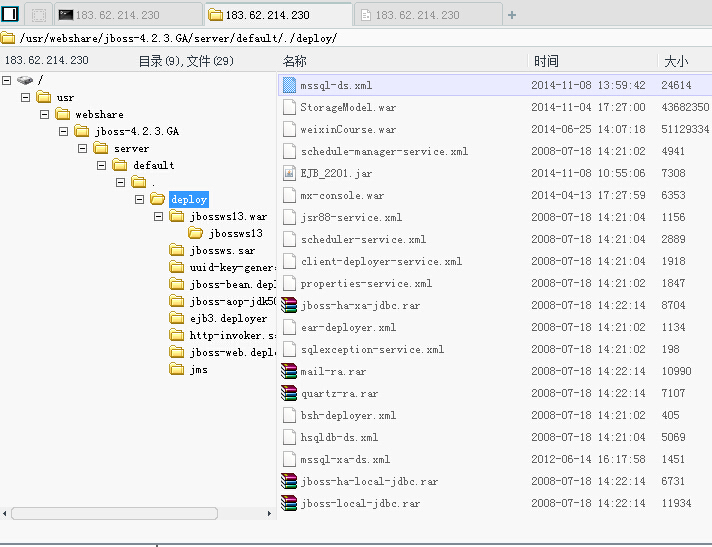
#5
数据库到手
#1
发现漏洞
站点:res.byd.cn/invoker/JMXInvokerServlet
直接getshell
#2
福利出现
但在getshell过程中发现:
站点:http://res.byd.cn/jbossws13/
返回:it works! Linux 2.6.18-194.el5 i386 ->||<-
很明显已有前辈进来过。
查看shell密码得心中暗喜,gainover~~~~~~~~~~~~~~
#4
来点图
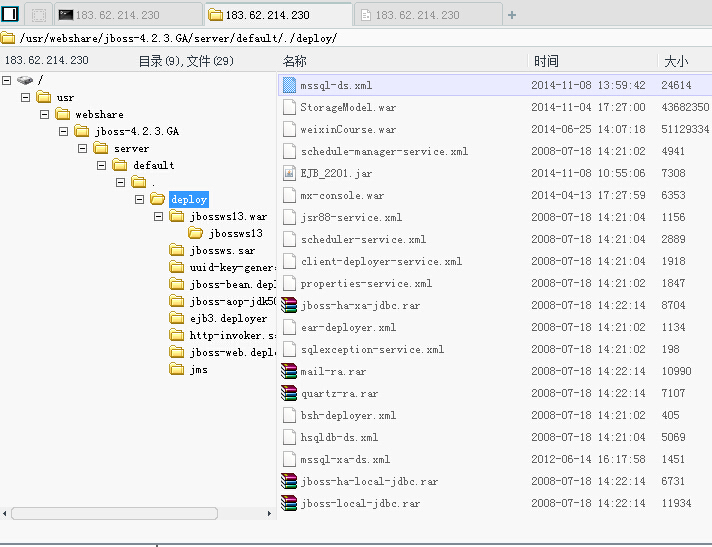
#5
数据库到手