74CMS最新版:74cms_v3.4.20140820 官方8.20号更新
文件:/user/personal/personal_resume.php
这里插入了求职意向,主要这里的职位信息:recentjobs
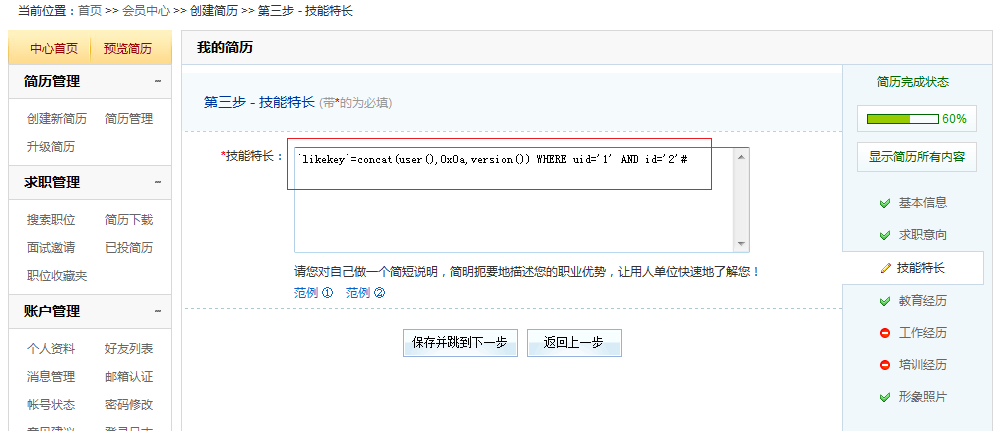
这里更新了技能特长:specialty
最后在文件:/include/fun_personal.php
这里从简历信息里取出来了信息
注意这里:
这里的recentjobs,specialty,就是上面插入简历信息里面的recentjobs,specialty,这里取出来后,有进入了updatetable:
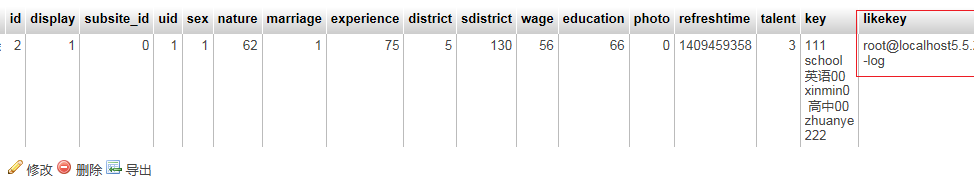
这里是更新搜索关键字的
最后来看看updatetable函数:
将参数直接进入SQL语句,没有经过过滤。
总结:
1、求职职位和技能特长进入数据库,可带入恶意sql语句
2、从简历信息里取出来职位及特长
3、再次进入数据库,没有过滤,恶意SQL语句进入数据库
4、导致二次sql注入
这里的求职职位,技能特长,姓名三处都存在二次注入
这里通过截断即可更新任意用户的信息了