漏洞概要
关注数(24)
关注此漏洞
漏洞标题:各大CMS厂商的CMS存在的同一安全问题
提交时间:2014-07-27 01:25
修复时间:2014-10-25 01:26
公开时间:2014-10-25 01:26
漏洞类型:xss跨站脚本攻击
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
Tags标签:
无
漏洞详情
披露状态:
2014-07-27: 细节已通知厂商并且等待厂商处理中
2014-07-31: 厂商已经确认,细节仅向厂商公开
2014-08-03: 细节向第三方安全合作伙伴开放
2014-09-24: 细节向核心白帽子及相关领域专家公开
2014-10-04: 细节向普通白帽子公开
2014-10-14: 细节向实习白帽子公开
2014-10-25: 细节向公众公开
简要描述:
实际上是很老一个问题,但经过我的测试,发现国内各大cms厂商,包括但不限于dedecms、phpcms、cmseasy、espcms、phpyun、thinksns、骑士人才系统、phpdisk、国微php168、phpok、kesioncms、pageadmin、xheditor、sdcms、emlog、dtcms等等都存着此安全漏洞(以上基本都有demo站或官网验证),不限于服务端语言(php、asp、aspx、jsp等)、不限操作系统及服务器中间件、不限浏览器种类及filter、能绕过大部分WAF,轻则越权操作,重则直接getshell,危害不可估量。其实你们已经发现了,漏洞类型是“XSS跨站脚本攻击”。
为了防止小伙伴们都来刷奖金、刷rank,我决定一起提交了,希望引起各大cms厂商的重视!
向前辈致敬:http://www.wooyun.org/bugs/wooyun-2010-064004 http://www.wooyun.org/bugs/wooyun-2010-064792
详细说明:
0x01 概述
相信很多站长对swfupload.swf、uploadify.swf这样的文件不陌生,做站的时候常常看到。实际上这是一个著名的利用swf异步上传的一个插件。
它可以很好解决异步上传、多文件异步上传的问题,很快这个插件就红遍了cms界,各大cms都使用这个swf来处理上传问题。
但是,这个swf却是一颗含有xss问题的定时炸弹!
代码可见,从参数(root.loaderInfo.parameters.movieName)中获得movieName后直接赋值到一些callback响应函数中,这些函数是js中执行的内容。我们只需闭合前面的"],再闭合try..catch中大括号},即可执行自己的javascript代码,造成反射型XSS。
因为是flash xss,而且没有过多关键字,所以无视浏览器filter和大部分WAF(因为在前端运行),所以影响较大,轻则越权操作、产生XSS、csrf蠕虫,重则直接getshell(结合某些cms的后台getshell技巧)。
0x02 各大cms纷纷躺枪
由于中招的cms过多,我就不一一截图了,直接给出官网demo或网上实例做演示吧:
漏洞证明:
0x03 证明:
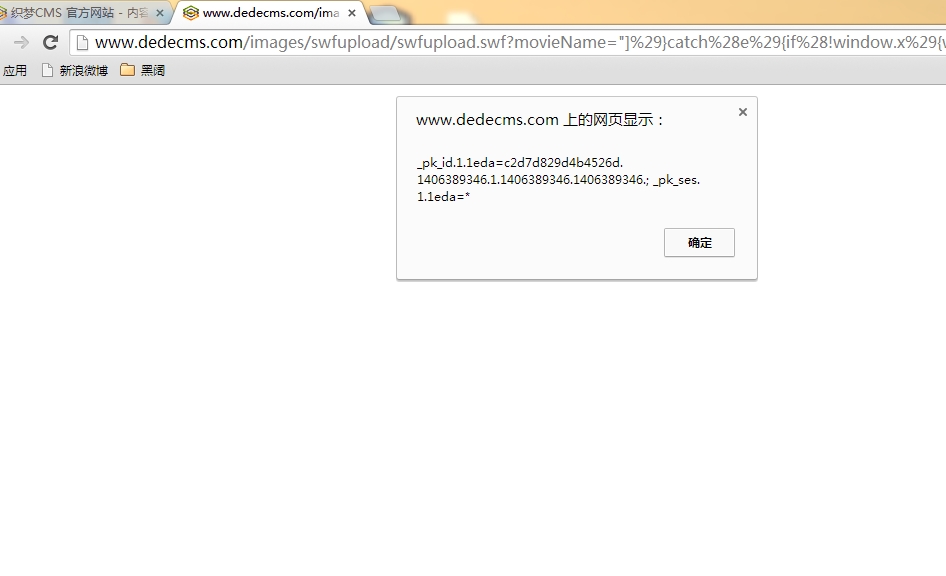
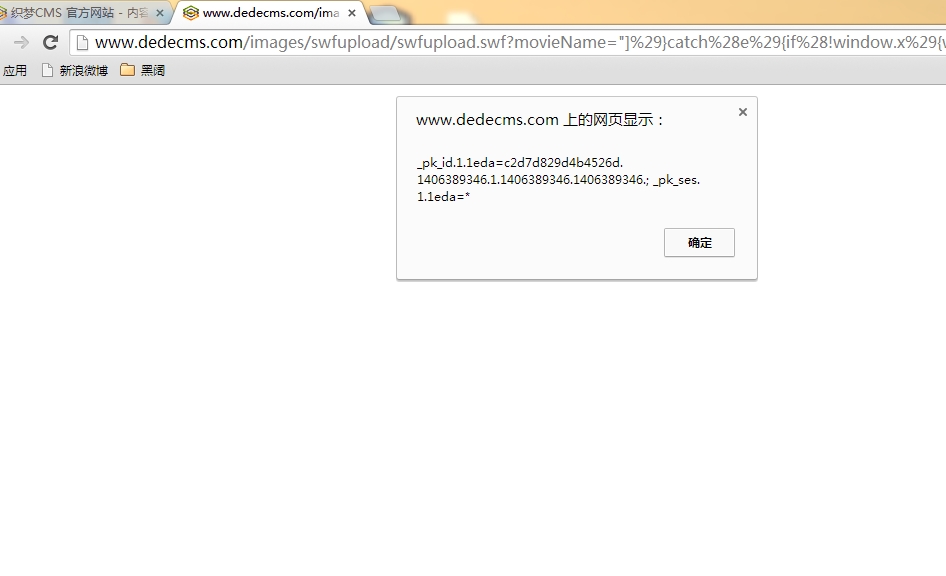
dedecms演示:
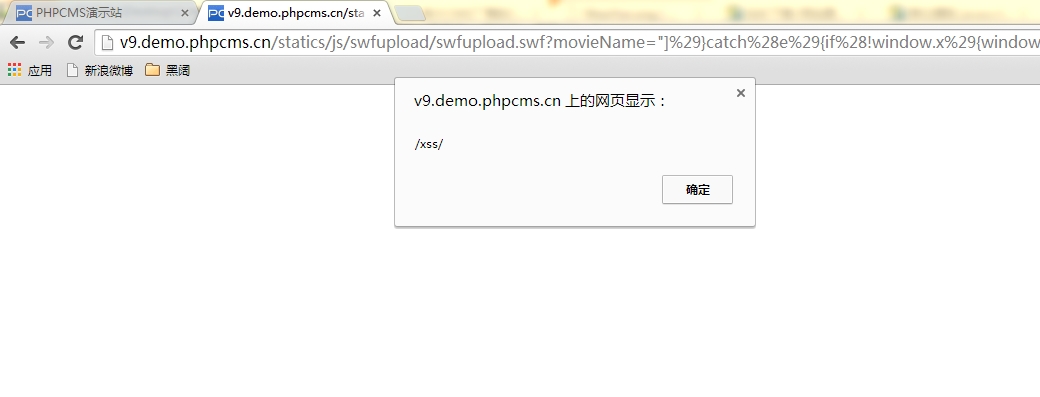
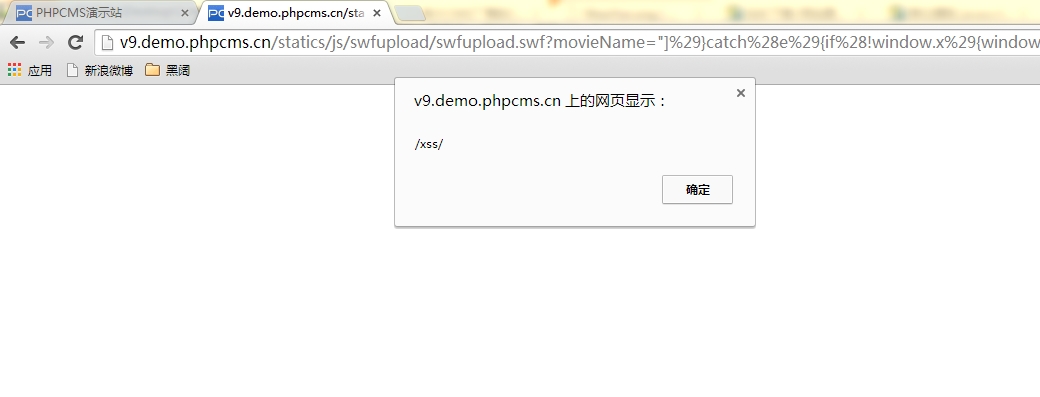
phpcms v9演示:
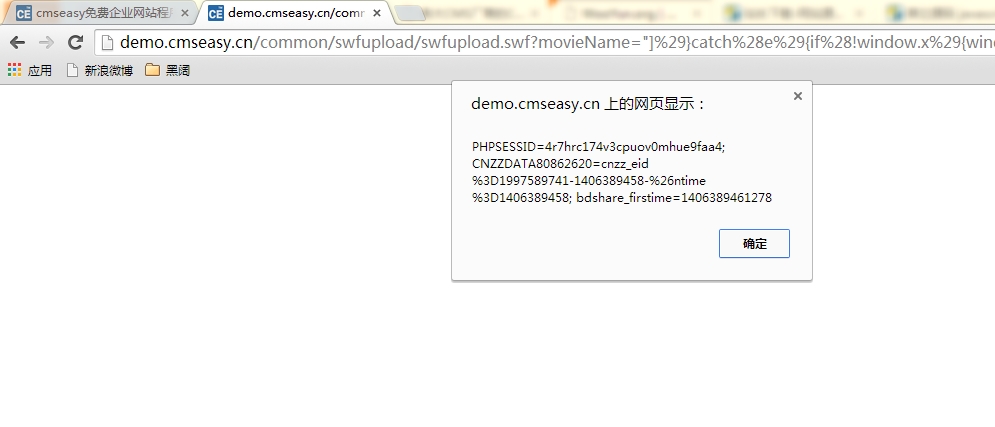
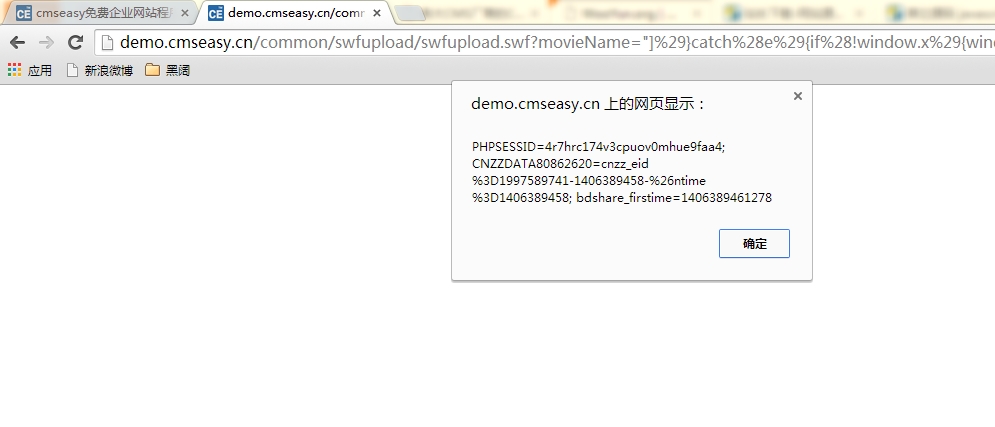
cmseasy 演示:
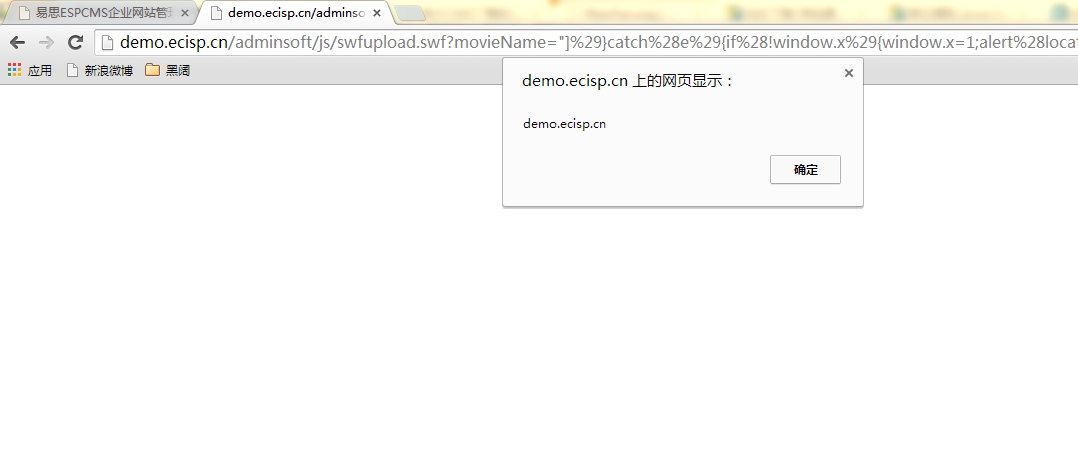
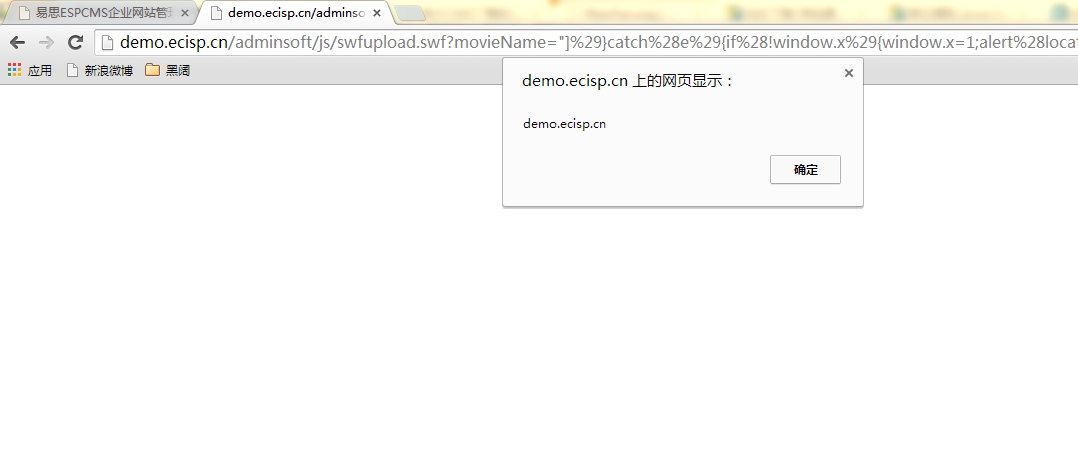
espcms 演示:
phpyun 演示:

多的我就不截图了。几乎都是在乌云注册的各大厂商,以及政府、企业、学校用的很多的CMS,包括不限于PHP、asp(kesioncms)、aspx(pageadmin、dtcms等)。
其中xheditor是编辑器,又被很多cms所引用,所以能够影响所有使用xheditor的用户,包括但不仅限于以下列表:

修复方案:
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:11
确认时间:2014-07-31 21:51
厂商回复:
CNVD确认所述情况,类似flash域跨站原理已经在相关讨论中遇到过,对于所述多款CMS面临的风险,暂无法一一处置。先行确认,由第三方厂商进行防护。
最新状态:
暂无