早上上班 吃完饭逛逛乌云 看看昨天的漏洞还没有确认 距离周五还有2天了 48小时 2880分钟 172800秒 .......
有问题的站点:
http://css.wangjiu.com/ 打开后乱七八糟的 有种遗弃的赶脚!
三个问题:
0x01:信息泄露
http://css.wangjiu.com//WEB-INF/web.xml
0x02:不知道是任意文件下载还是怎么样
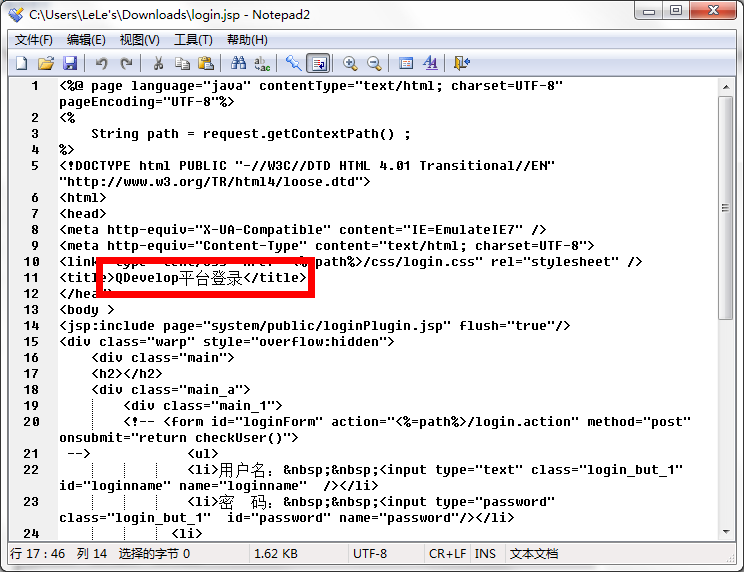
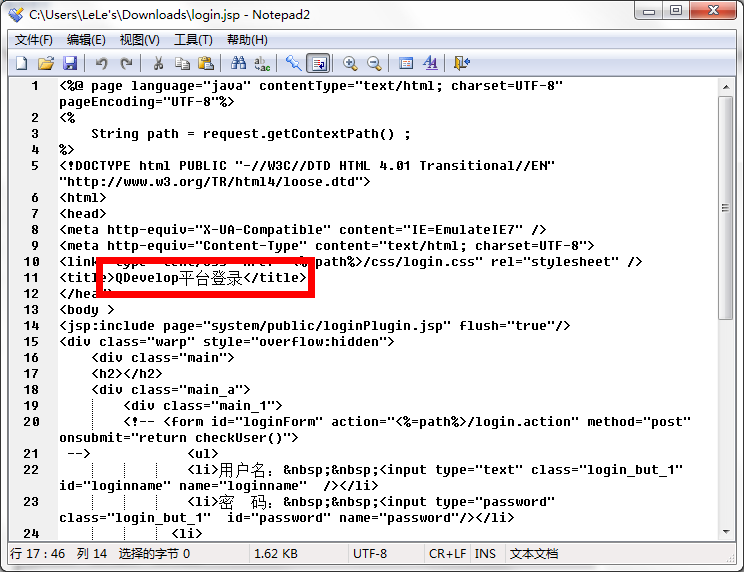
http://css.wangjiu.com/login.jsp

既然下下来了就看一看吧。
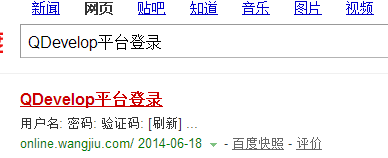
然后直接百度了
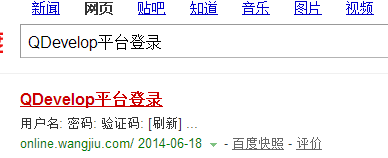
直接就出来登陆地址了
没登陆进去 只是提示到期了之类的
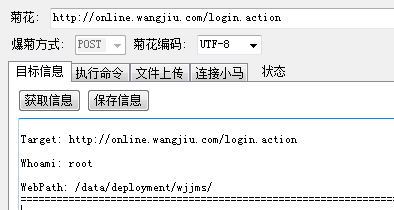
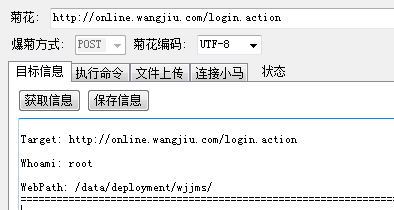
root权限 这就好玩了