漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-065718
漏洞标题:某商务大量在用系统存在绕过SQL防注入保护漏洞之三(影响数十万商务网站)
相关厂商:cncert国家互联网应急中心
漏洞作者: 泳少
提交时间:2014-06-23 17:44
修复时间:2014-09-21 17:46
公开时间:2014-09-21 17:46
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-06-23: 细节已通知厂商并且等待厂商处理中
2014-06-27: 厂商已经确认,细节仅向厂商公开
2014-06-30: 细节向第三方安全合作伙伴开放
2014-08-21: 细节向核心白帽子及相关领域专家公开
2014-08-31: 细节向普通白帽子公开
2014-09-10: 细节向实习白帽子公开
2014-09-21: 细节向公众公开
简要描述:
第三波的节奏啊?!!!!!!!!谢谢。。标题貌似有点夸张。。但是真的很腻害的样子。。@疯狗 @finger 大厂商吧!
详细说明:
看见了U神这个大牛能绕过防注入保护。然后我就找他询问下怎么绕过http://wooyun.org/bugs/wooyun-2010-065537!毕竟我这个本身是防注入的。。好了
废话不多说。直接主题。。。
关键字:
http://74.125.227.77/#newwindow=1&q=+%E6%8A%80%E6%9C%AF%E6%94%AF%E6%8C%81%EF%BC%9A%E9%91%AB%E5%8D%93%E7%BD%91%E7%BB%9C
收集了点网站:
总结得出理论,Product.asp这个文件是产品展示的!后面的都是参数。
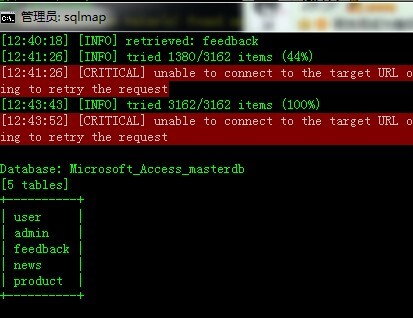
然后找了个网站利用sqlmap进行cookie注入
漏洞证明:
修复方案:
想办法去吧!
版权声明:转载请注明来源 泳少@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2014-06-27 22:53
厂商回复:
CNVD确认并复现所述通用案例情况,已经由CNVD直接联系软件生产厂商,电话至****,将通报发送至邮箱yjm** 中处置。
最新状态:
暂无