漏洞概要
关注数(24)
关注此漏洞
漏洞标题:驴妈妈某分站敏感信息泄露可导致信息系统被渗透
提交时间:2013-11-07 20:44
修复时间:2013-11-12 20:45
公开时间:2013-11-12 20:45
漏洞类型:敏感信息泄露
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
Tags标签:
无
漏洞详情
披露状态:
2013-11-07: 细节已通知厂商并且等待厂商处理中
2013-11-12: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
由于没有一个通用标准的防御规则保护好中间件配置信息、DNS信息、业务数据信息、用户信息、源码备份文件、版本管理工具信息、系统错误信息和敏感地址信息(后台或测试地址)的泄露,攻击者可能会通过收集这些保护不足的数据,利用这些信息对系统实施进一步的攻击。
由于只是安全测试,本次未深入一步获取服务器和数据库权限!
详细说明:
#1 信息泄露原因
由于驴妈妈论坛管理员在更新服务器文件时,未注意到编辑器会默认创建各种.bak文件用来规避错误编辑时引发的数据丢失风险,从而造成了更严重的信息安全问题。
#2 泄露内容
网站: http://bbs.lvmama.com
网址:http://bbs.lvmama.com/config/config_global.php.bak
内容:
漏洞证明:
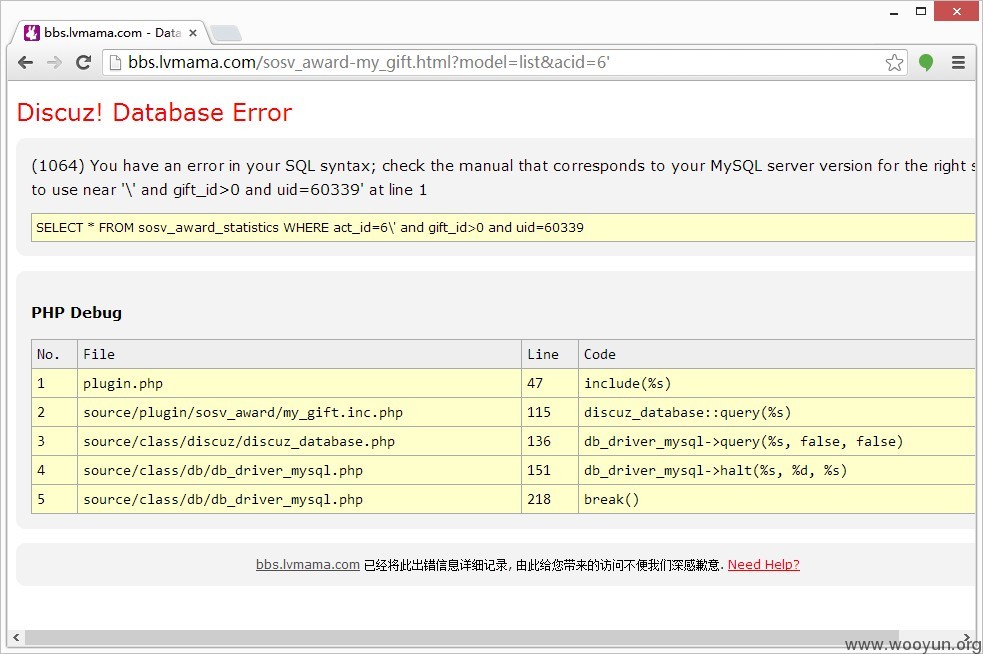
# 再附送一个论坛的SQL注入漏洞
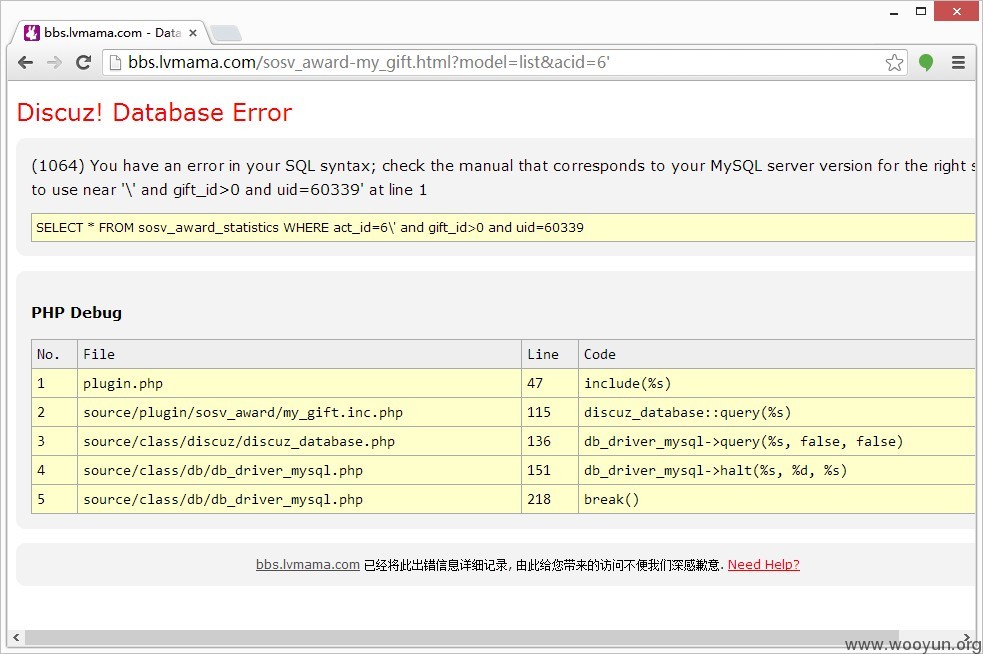
# 漏洞证明
有时候,论坛appkey泄露,骇客利用恶意调用论坛API将对论坛造成严重破坏。
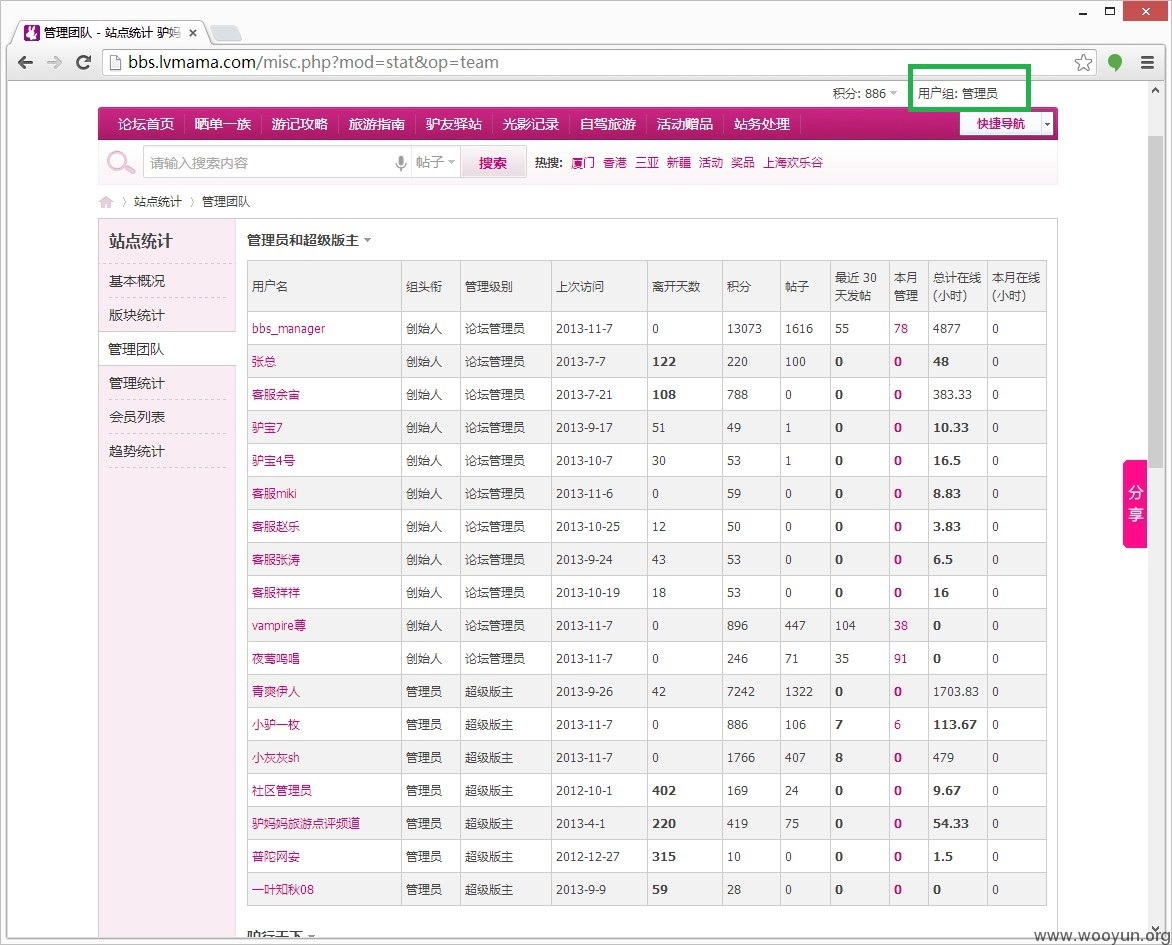
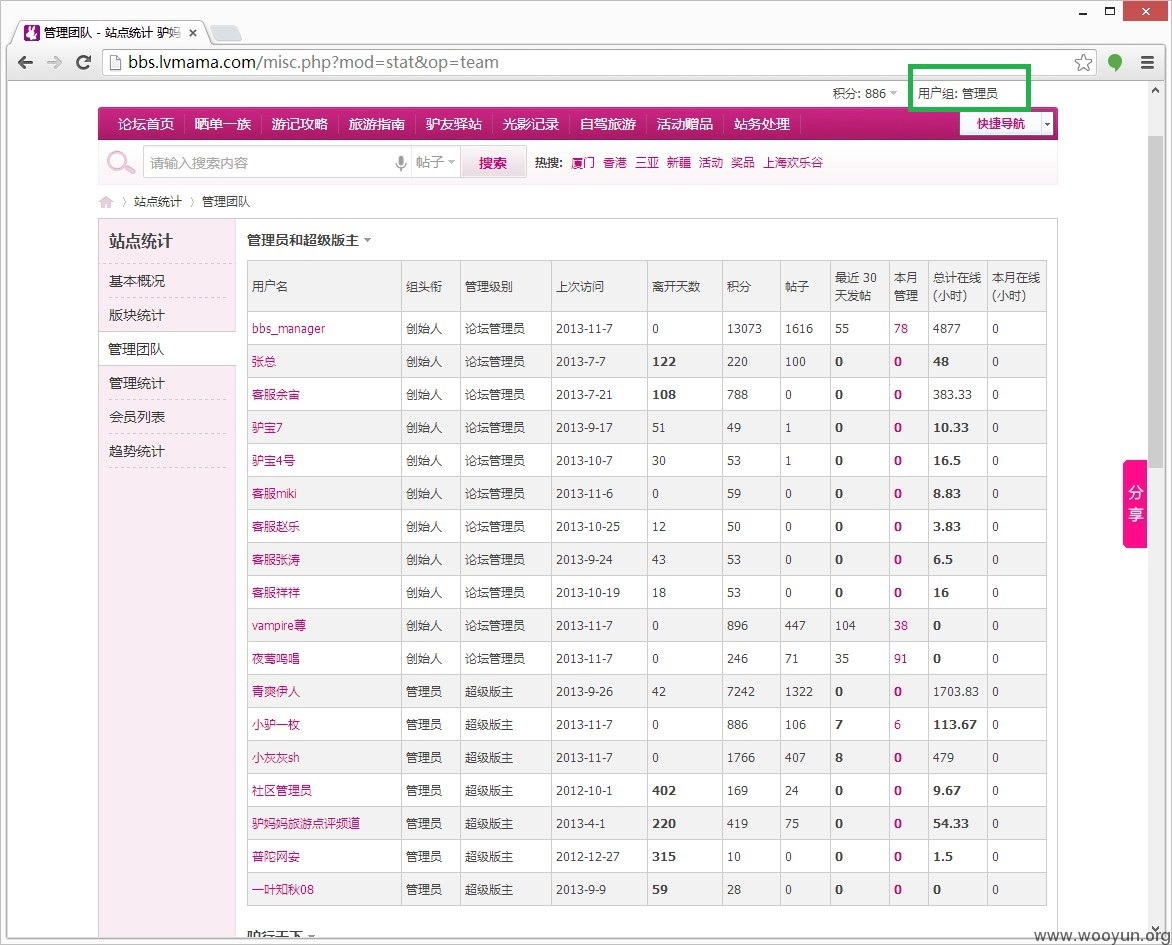
# 间接利用获取到论坛管理员权限(由于只是安全测试,未深一步获取服务器和数据库权限!)
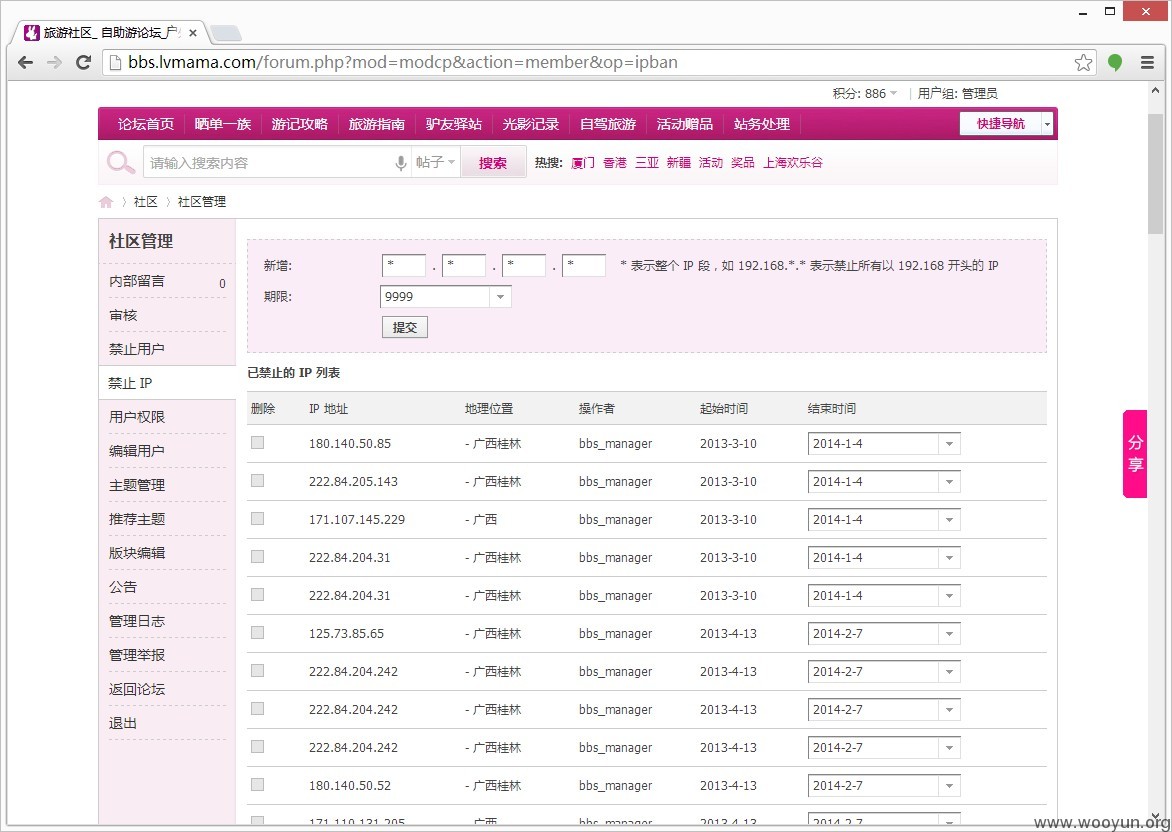
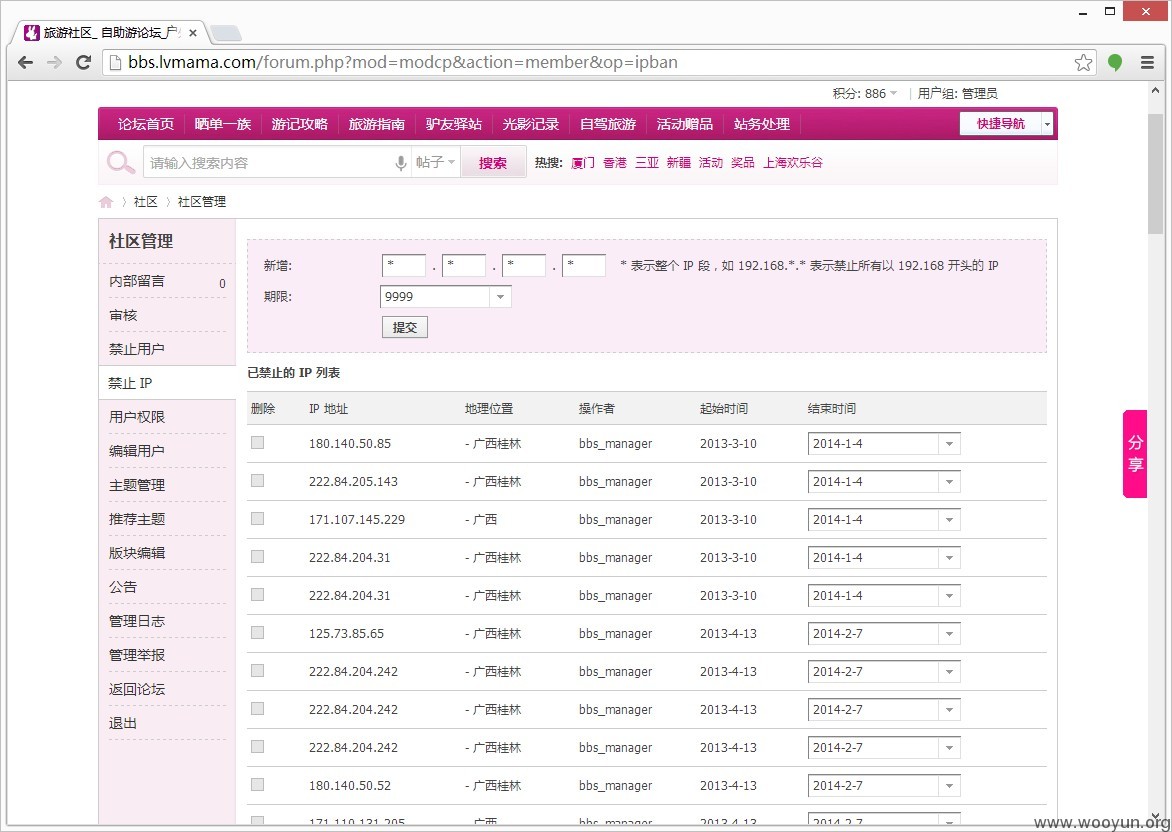
# 可禁止所有IP访问论坛,并删除所有论坛交流贴
修复方案:
版权声明:转载请注明来源 猪猪侠@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2013-11-12 20:45
厂商回复:
漏洞Rank:10 (WooYun评价)
最新状态:
暂无