漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-09066
漏洞标题:图虫网存储xss
相关厂商:图虫网
漏洞作者: _Evil
提交时间:2012-06-30 18:55
修复时间:2012-07-05 18:56
公开时间:2012-07-05 18:56
漏洞类型:xss跨站脚本攻击
危害等级:中
自评Rank:5
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-06-30: 细节已通知厂商并且等待厂商处理中
2012-07-05: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
危害大吧, cookies只要拿到了 账号+MD5密码就到手了,然后......
详细说明:
http://tuchong.com/settings/
注册了在这里配置:
在标签处插入:
保存.
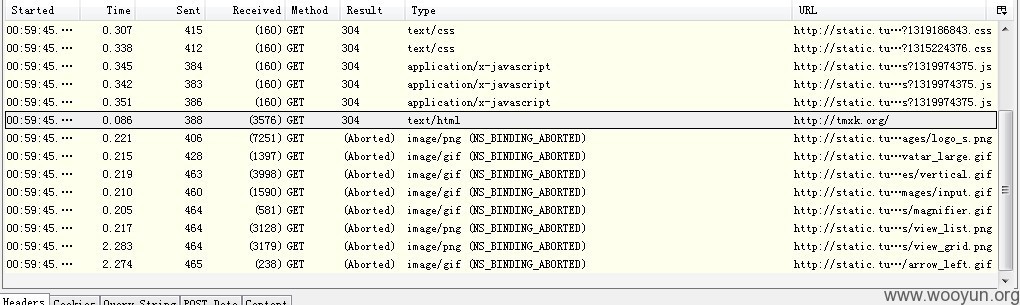
个人主页触发了 哦 \(^o^)/~
http://tuchong.com/272288/
这...... 自己测试了下盗取cookie危害大- -
还有个通杀的反射型xss:
tochong.com所以子站xxxxx.tuchong.com/?view=list 都有Xss漏洞
其他的反射型Xss就一堆了希望tuchong能修复,该转义 该编码 该过滤...
Zend配置也没配置好,爆路径的也很多..
谷歌下 site:tuchong.com php
或者随便举个列子
注册:
<input type="text" required="" id="regEmail" name="user_email">
user_email我改成[0x7c or '1'='1'#]
其他的- -||不说了.....
漏洞证明:
http://tuchong.com/settings/
注册了在这里配置:
在标签处插入:
保存.
个人主页触发了 哦 \(^o^)/~
http://tuchong.com/272288/
这...... 自己测试了下盗取cookie危害大- -
还有个通杀的反射型xss:
tochong.com所以子站xxxxx.tuchong.com/?view=list 都有Xss漏洞
其他的反射型Xss就一堆了希望tuchong能修复,该转义 该编码 该过滤...
Zend配置也没配置好,爆路径的也很多..
谷歌下 site:tuchong.com php
或者随便举个列子
注册:
<input type="text" required="" id="regEmail" name="user_email">
user_email我改成[0x7c or '1'='1'#]
其他的- -||不说了.....
修复方案:
该转义 该编码 该过滤... zend配置好.
版权声明:转载请注明来源 _Evil@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2012-07-05 18:56
厂商回复:
最新状态:
2012-07-10:谢谢,我们接受到了,会在近期改正!