测试地址:
过程如下:
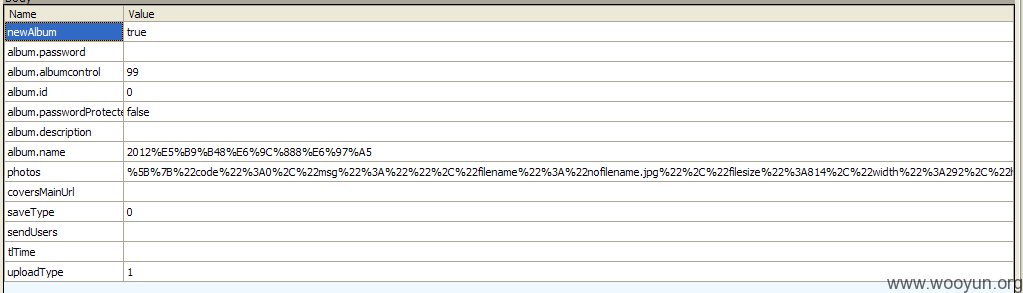
在相册中随意上传一张相片,到发布的时候截包。放过前面几个包,到http://upload.renren.com/upload/[YOUR ID]/finish_upload/v1.0的时候停下。
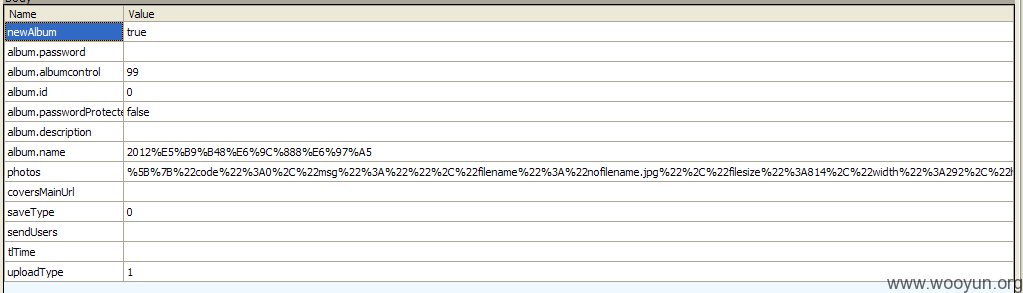
关键就是其中的photos参数~
信息如下,
URIComp解码,得到
目测,通常这种都没有过滤js unicode后的代码。
所以我们将JS代码unicode一下。
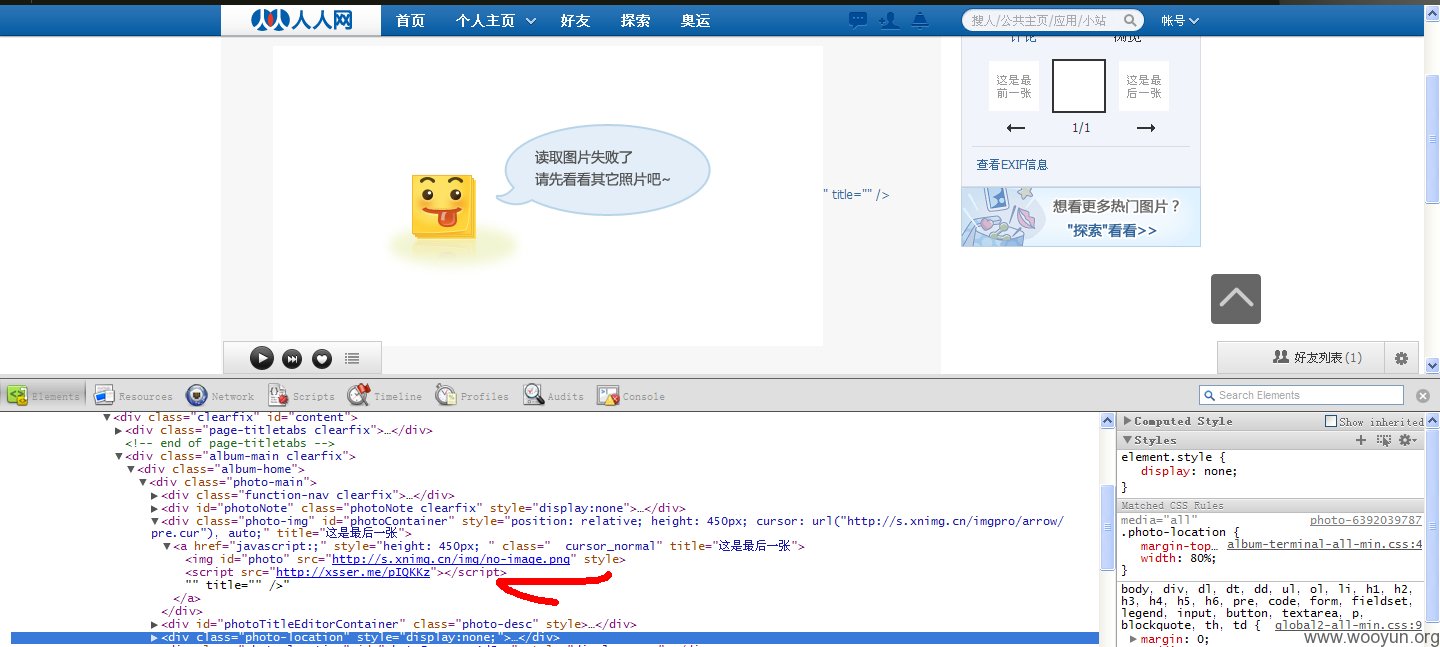
将UNICODE后的插在图片地址的后面。
然后给他进行URIComp编码。
将这个替换fiddler中的photo中的参数。
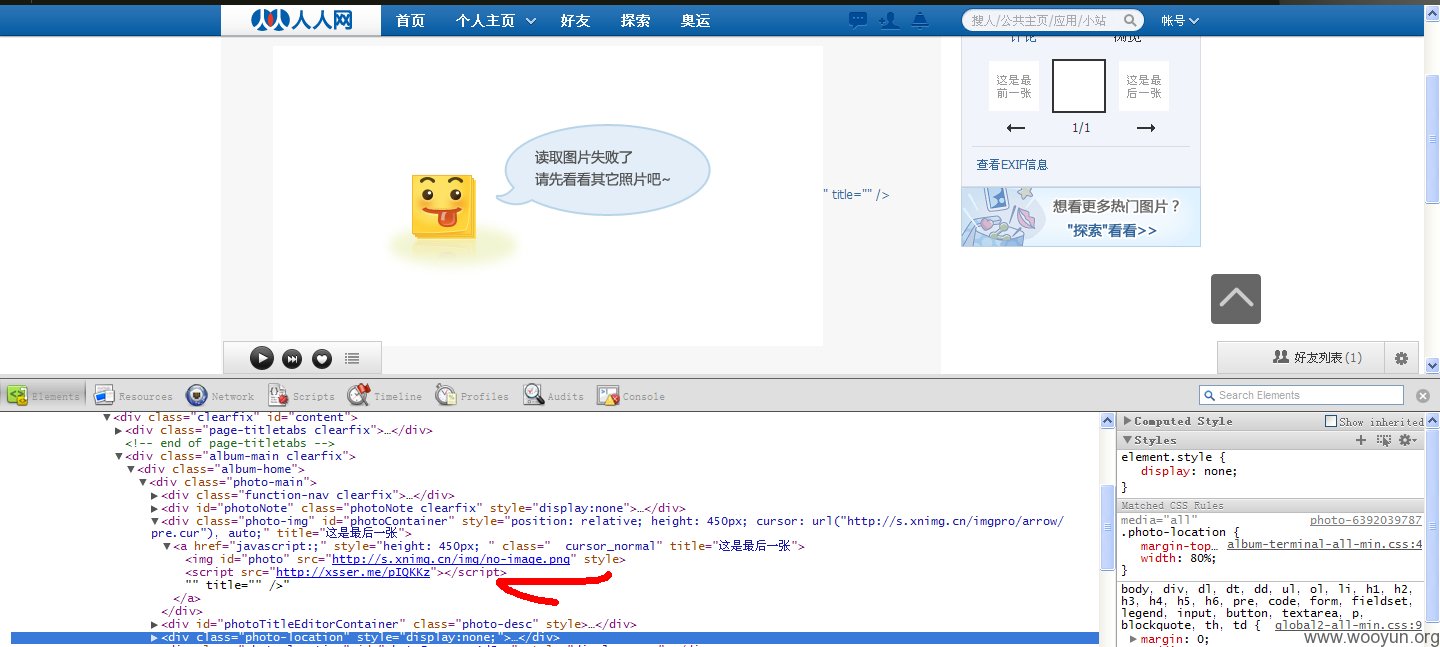
图在上面~~~
然后我们打开图片开源码,果断的X了。
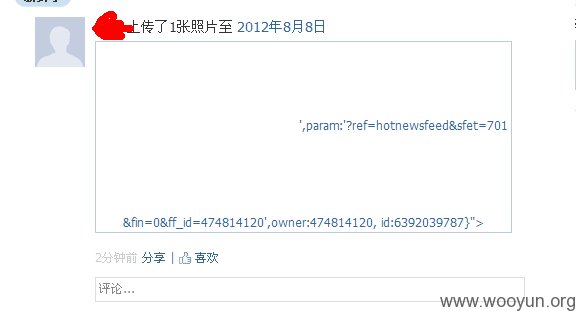
同时,目测在新鲜事中也会有同步。
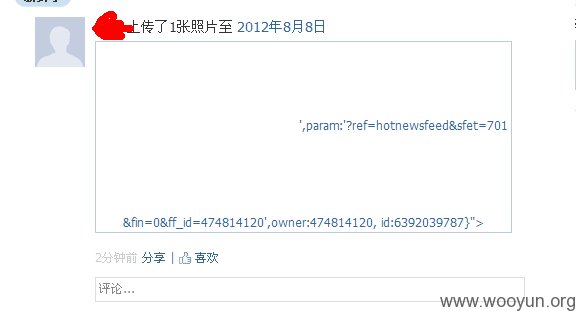
看了看新鲜事中的源码,也有JS链接,不过貌似不运行。。。-_-||
限制了新鲜事中的JS运行?
不过也无伤大雅,其他用户看到那么奇葩的代码应该都会去点一点的。。。
点就跨~~