漏洞概要
关注数(24)
关注此漏洞
漏洞标题:太平洋保险某系统存在任意文件上传漏洞可威胁内网
提交时间:2015-10-24 10:14
修复时间:2015-12-11 09:48
公开时间:2015-12-11 09:48
漏洞类型:文件上传导致任意代码执行
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2015-10-24: 细节已通知厂商并且等待厂商处理中
2015-10-27: 厂商已经确认,细节仅向厂商公开
2015-11-06: 细节向核心白帽子及相关领域专家公开
2015-11-16: 细节向普通白帽子公开
2015-11-26: 细节向实习白帽子公开
2015-12-11: 细节向公众公开
简要描述:
任意文件上传漏洞可威胁内网,求高rank
详细说明:
http://webchat.cpic.com.cn:9090

问题页面

上传附件处可直接上传shell文件
漏洞证明:
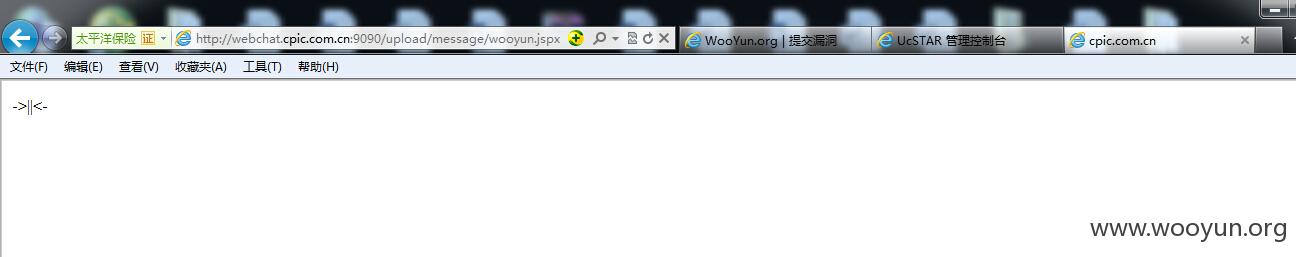
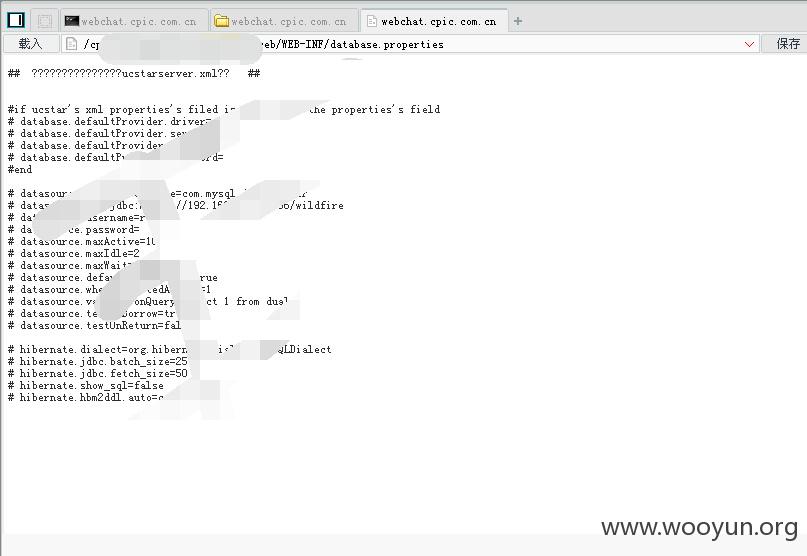
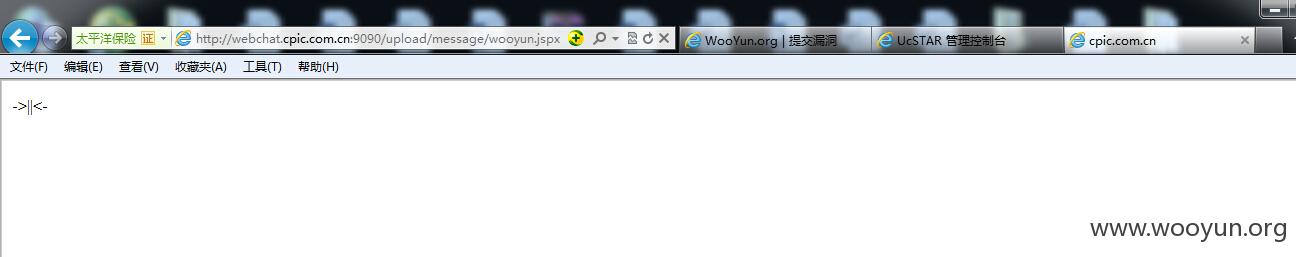
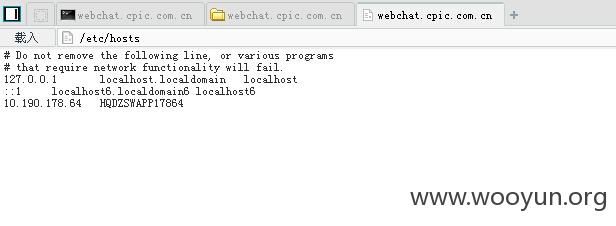
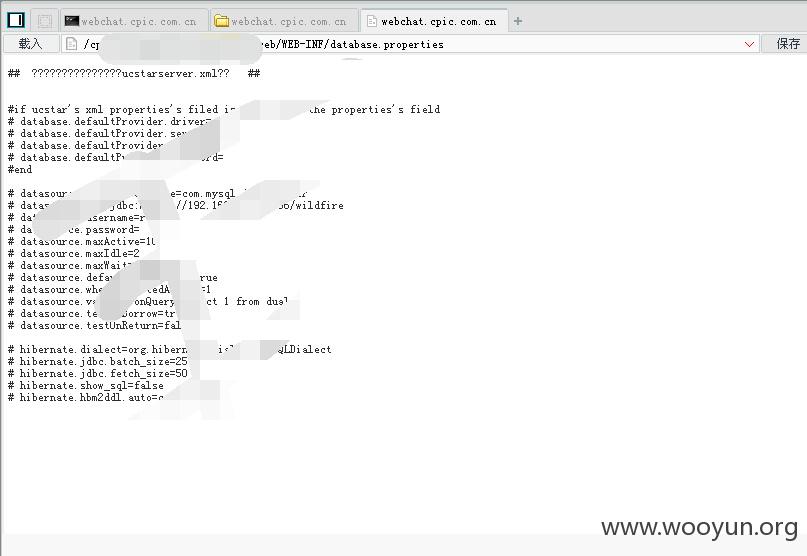
上传后的路径在http://webchat.cpic.com.cn:9090/upload/message/wooy.jspx
一句话地址:http://webchat.cpic.com.cn:9090/upload/message/wooyun.jspx
密码:wpp
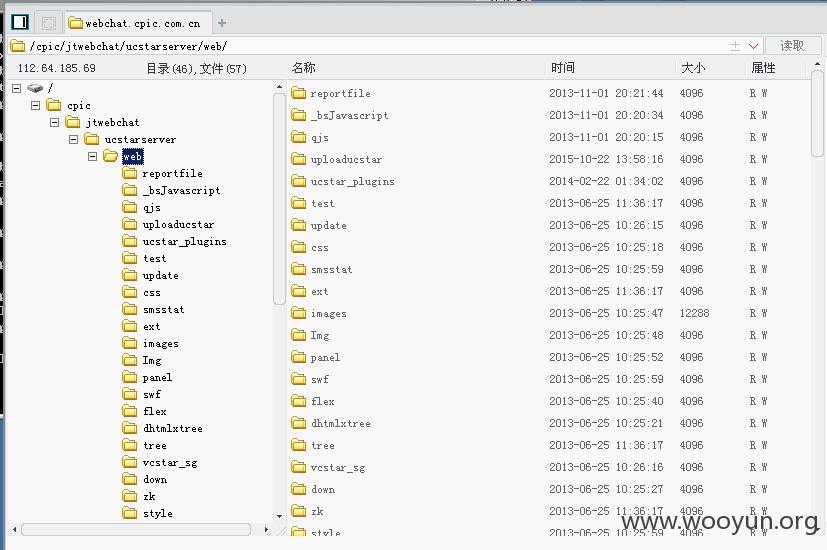
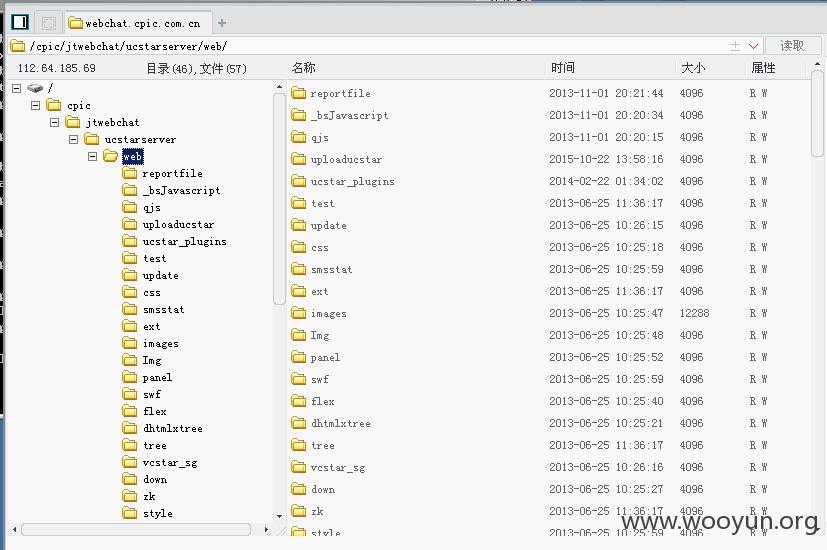
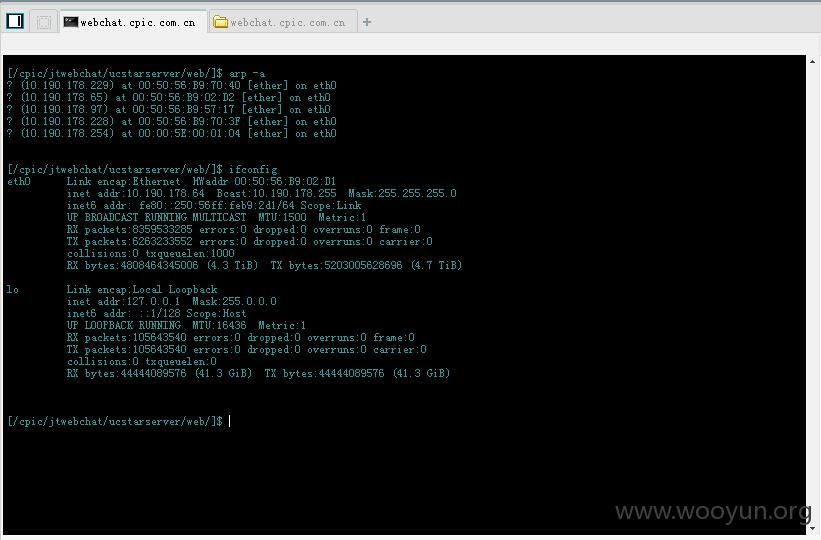
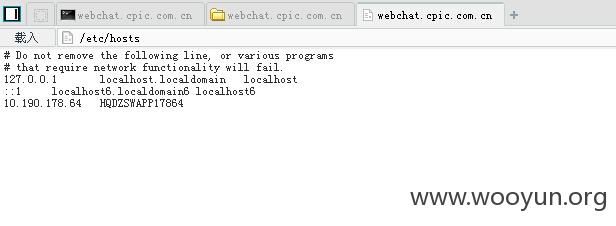
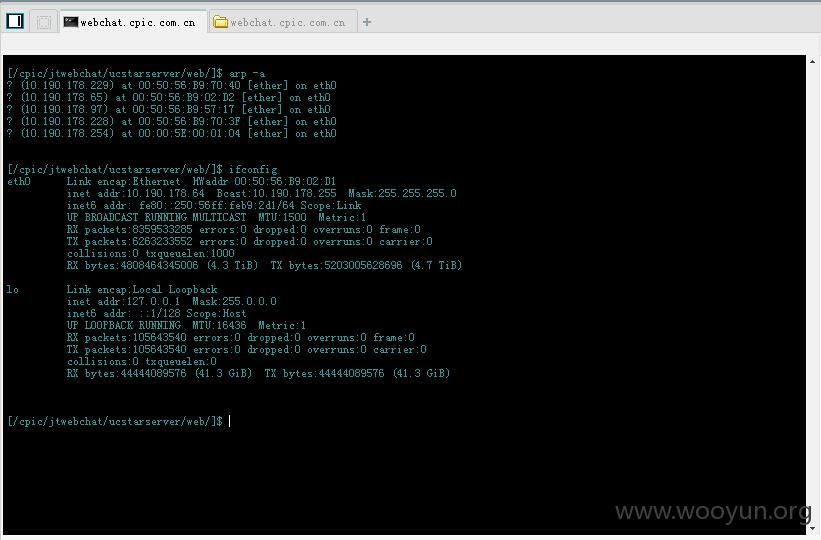
可威胁内网
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2015-10-27 09:47
厂商回复:
感谢白帽子对我公司安全支持。鉴于发生问题网页无法从登陆页面及其他页面找到,且白帽子也没有提供问题网页发现方法,且上传服务器会定期杀马,提供的一句话已失效,综合考虑给予10rank的评价。
最新状态:
暂无