http://www.pifii.com/
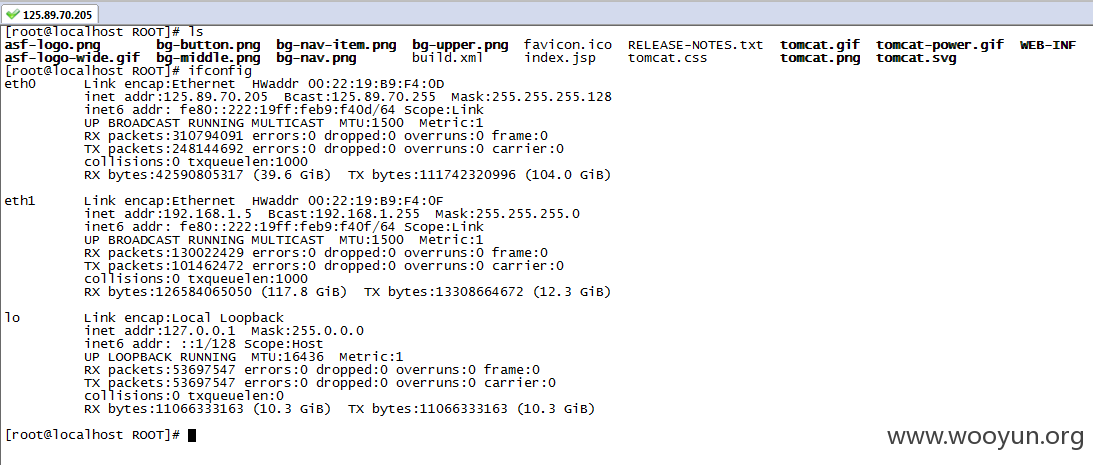
测试发现,派路由的机房大概IP
电信:
#125.89.70.204
125.89.70.205
125.89.70.206
125.89.70.207
125.89.70.208
125.89.70.209
联通:
#218.104.193.204
218.104.193.205
218.104.193.206
218.104.193.207
218.104.193.208
218.104.193.209
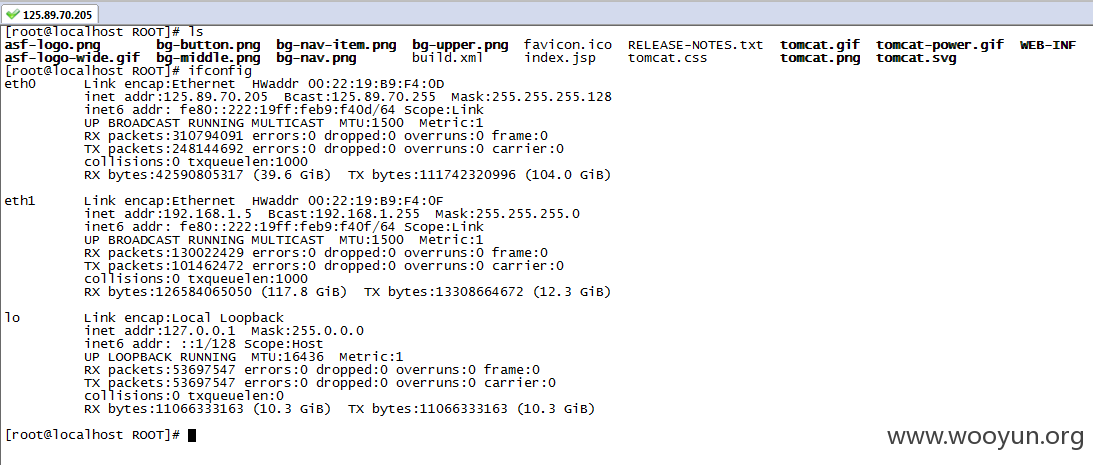
大部分都存在通用密码,root/ZH@id#0427。
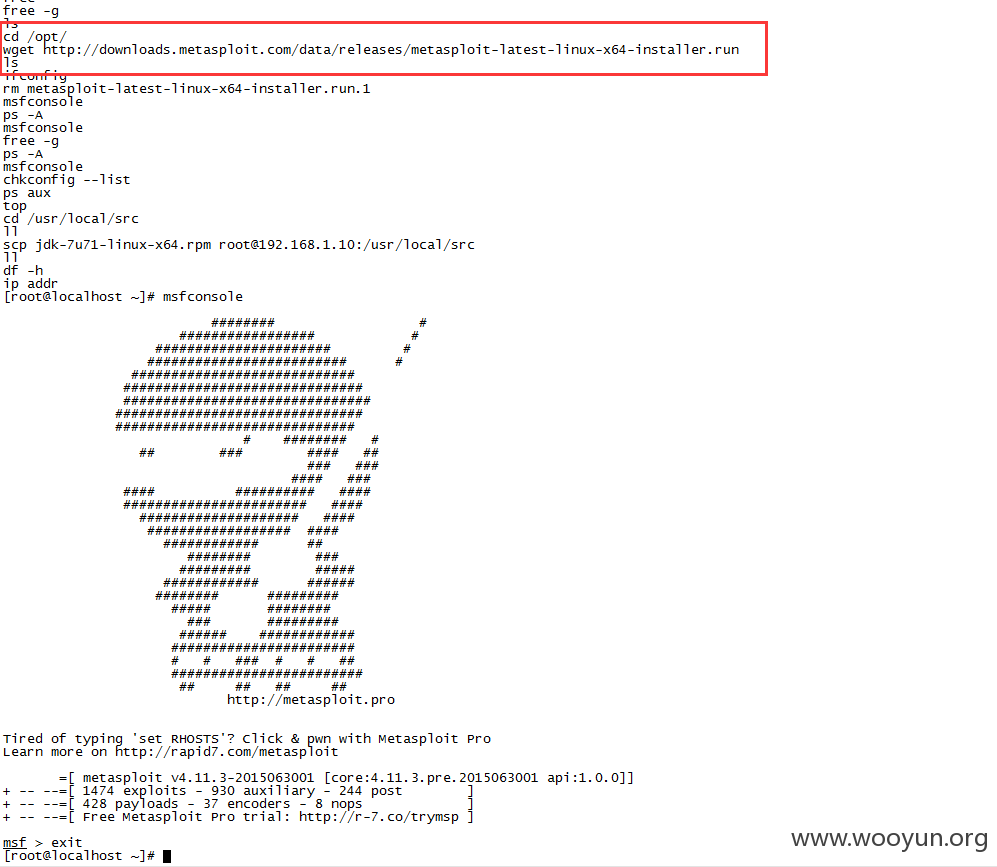
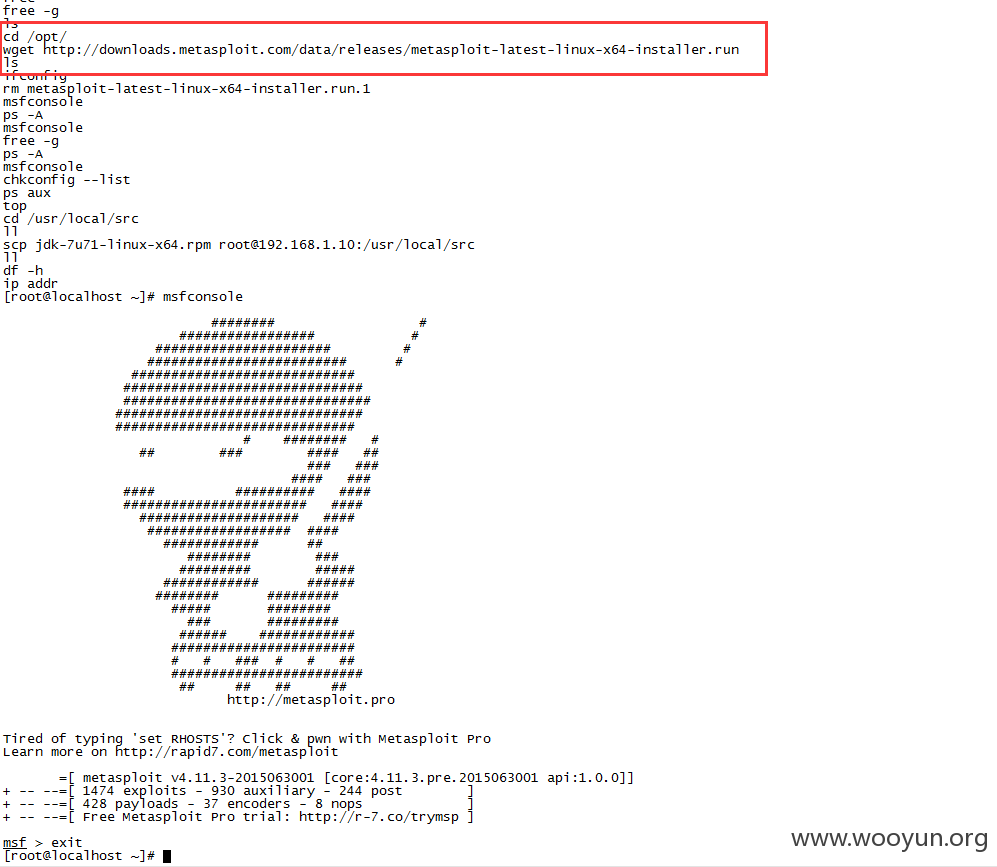
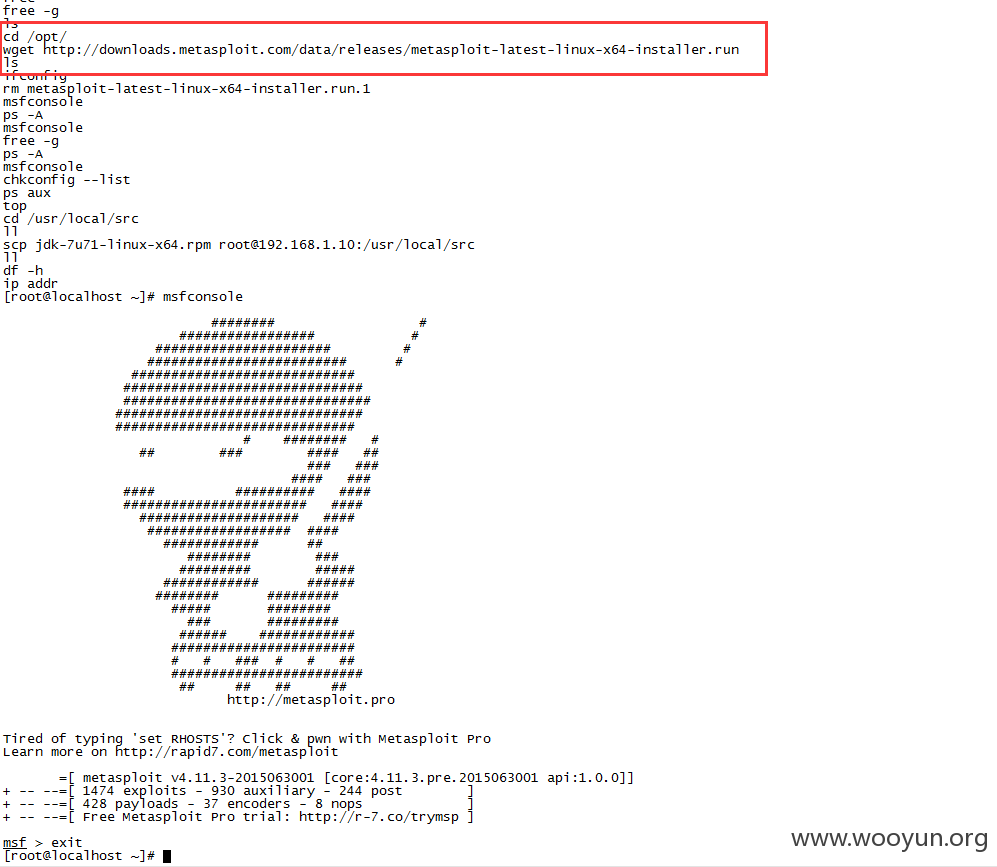
可以看出来,已经被入侵过了,上面有msf。
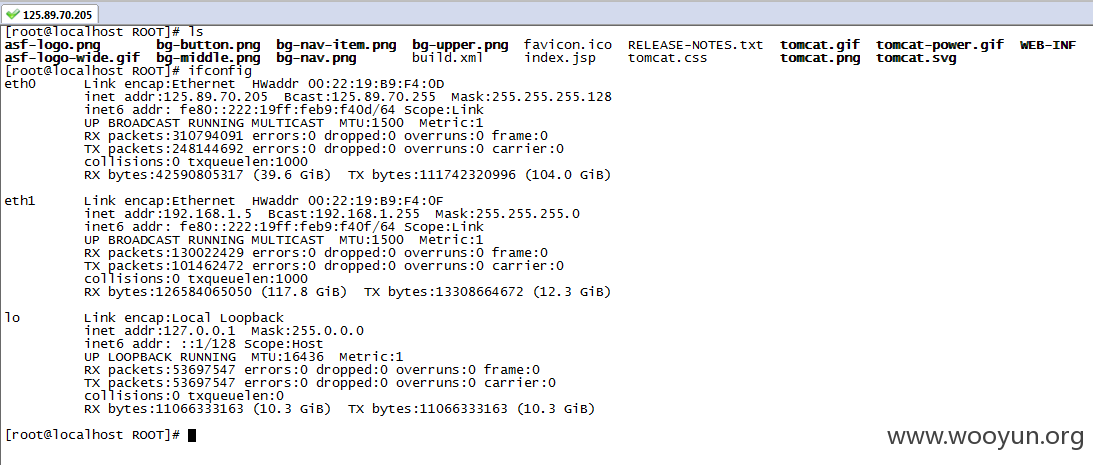
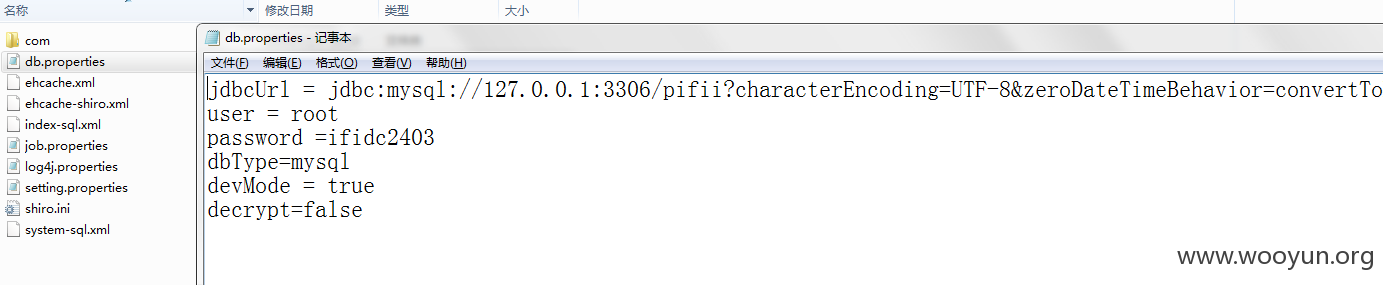
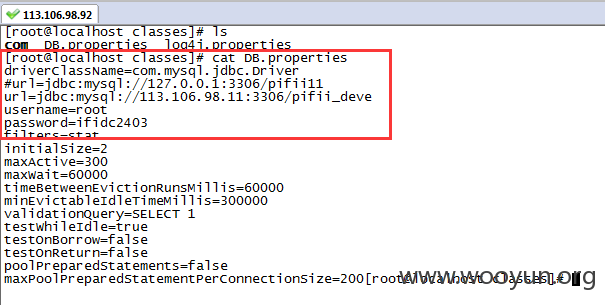
官网服务器也是这个密码,沦陷
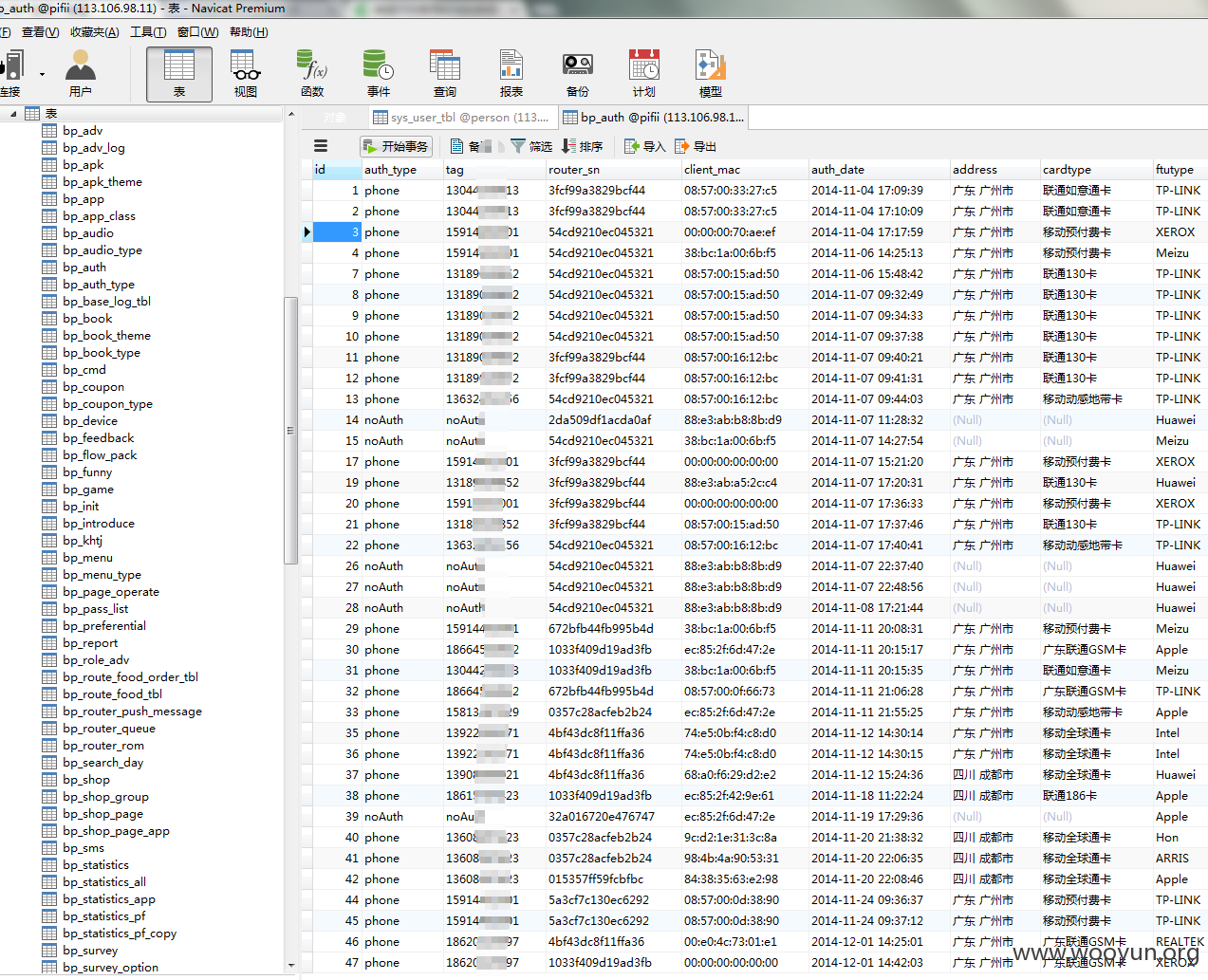
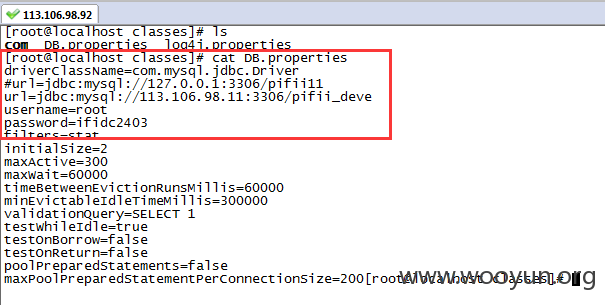
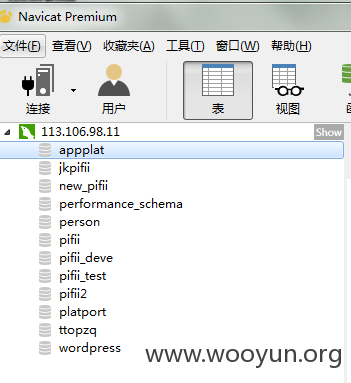
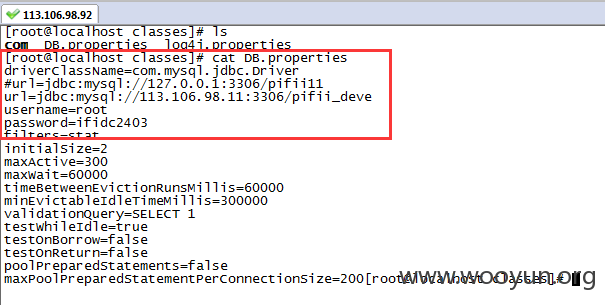
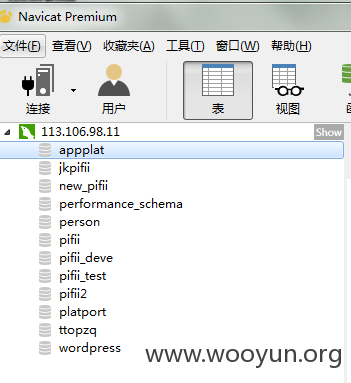
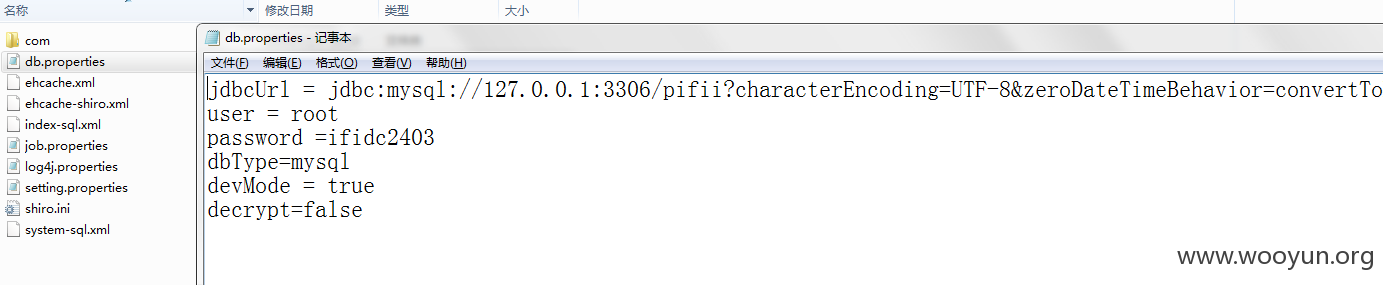
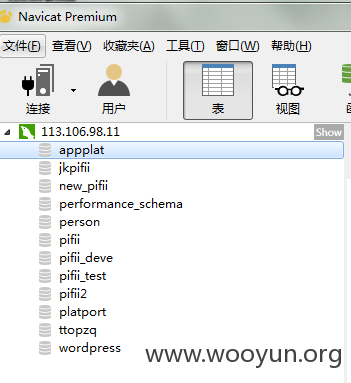
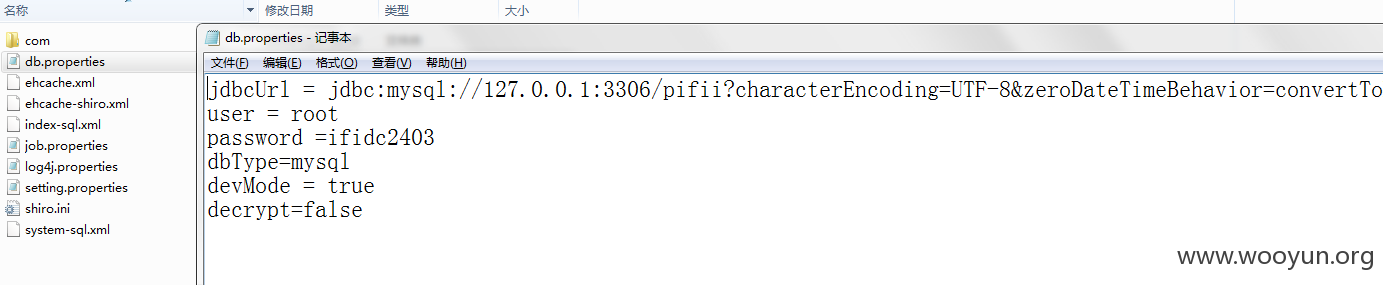
泄漏用户数据库信息
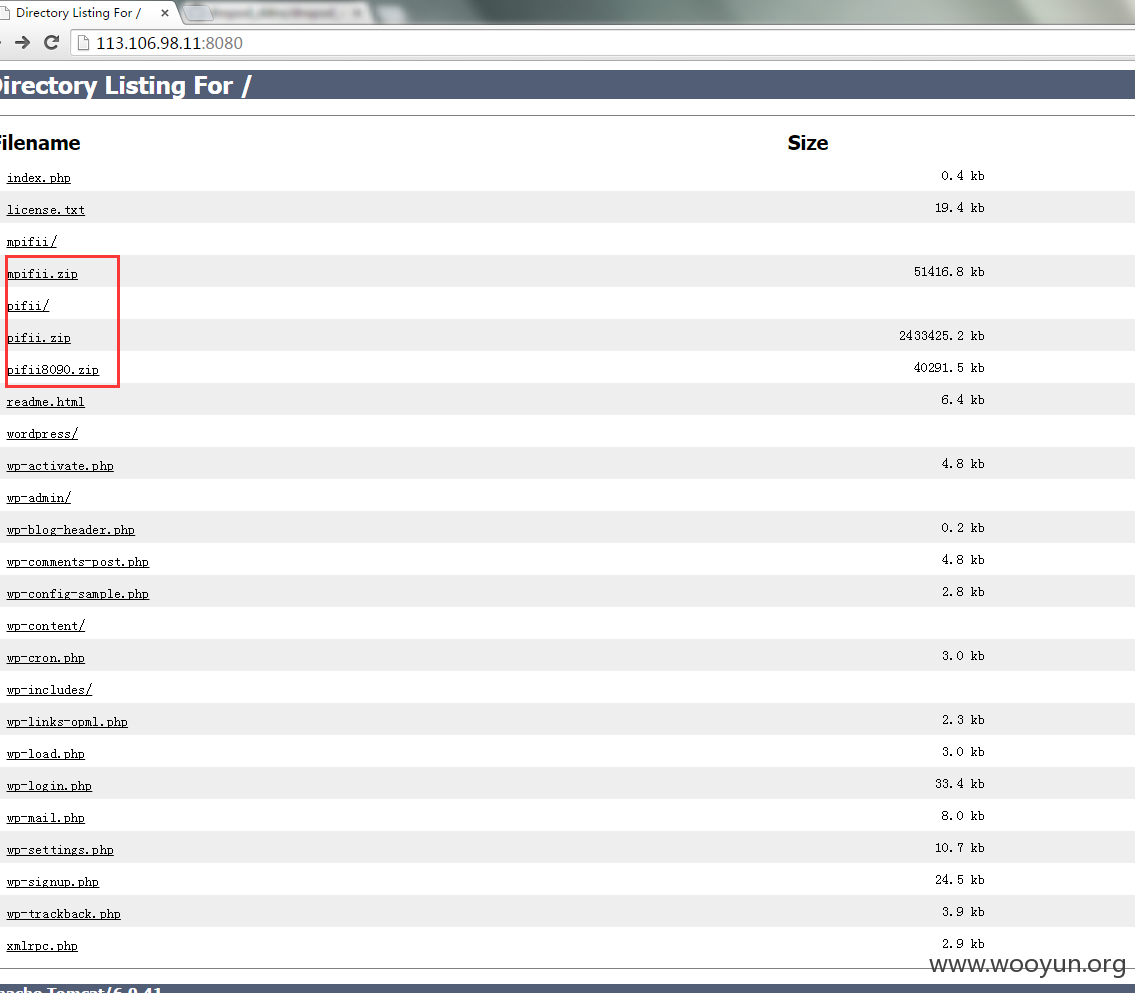
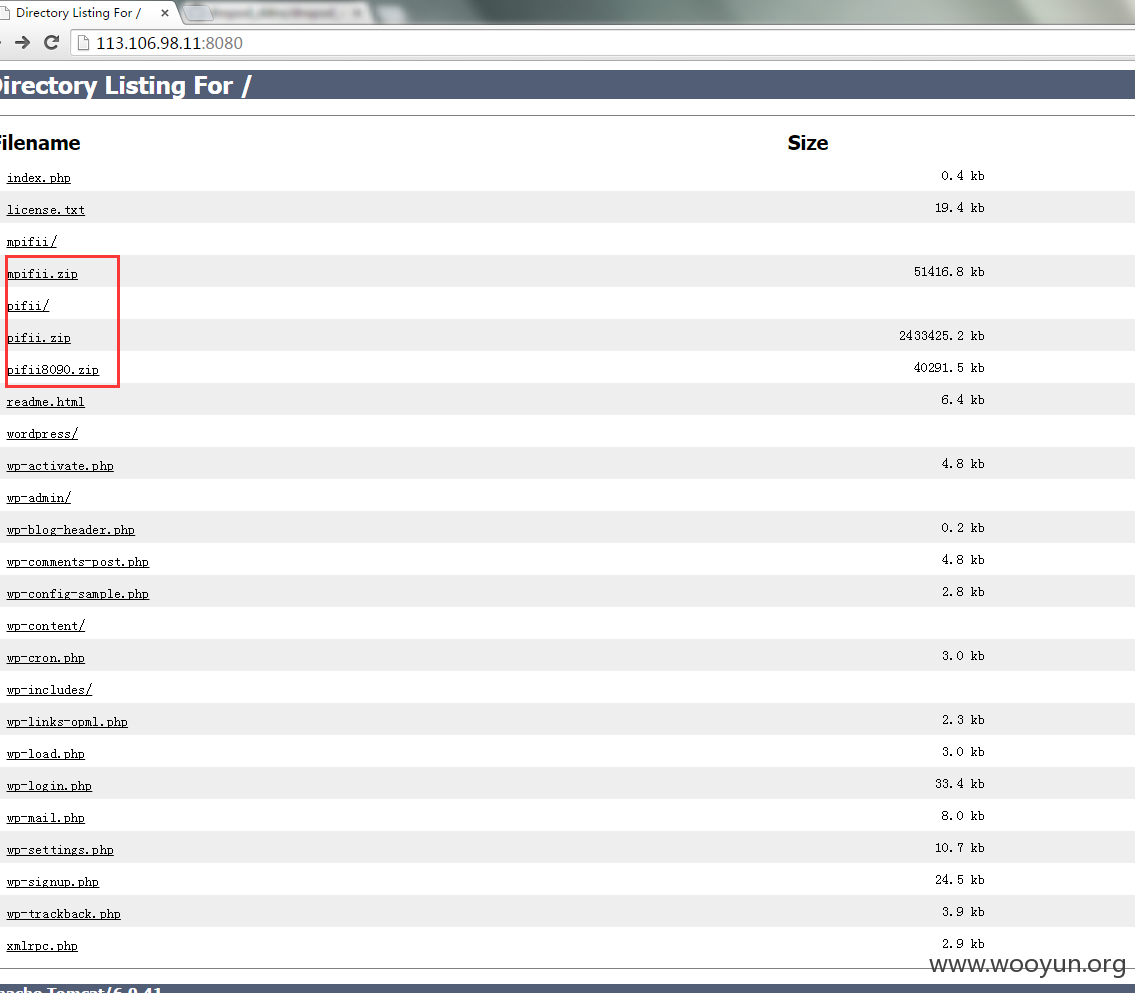
同时还存在备份文件下载。
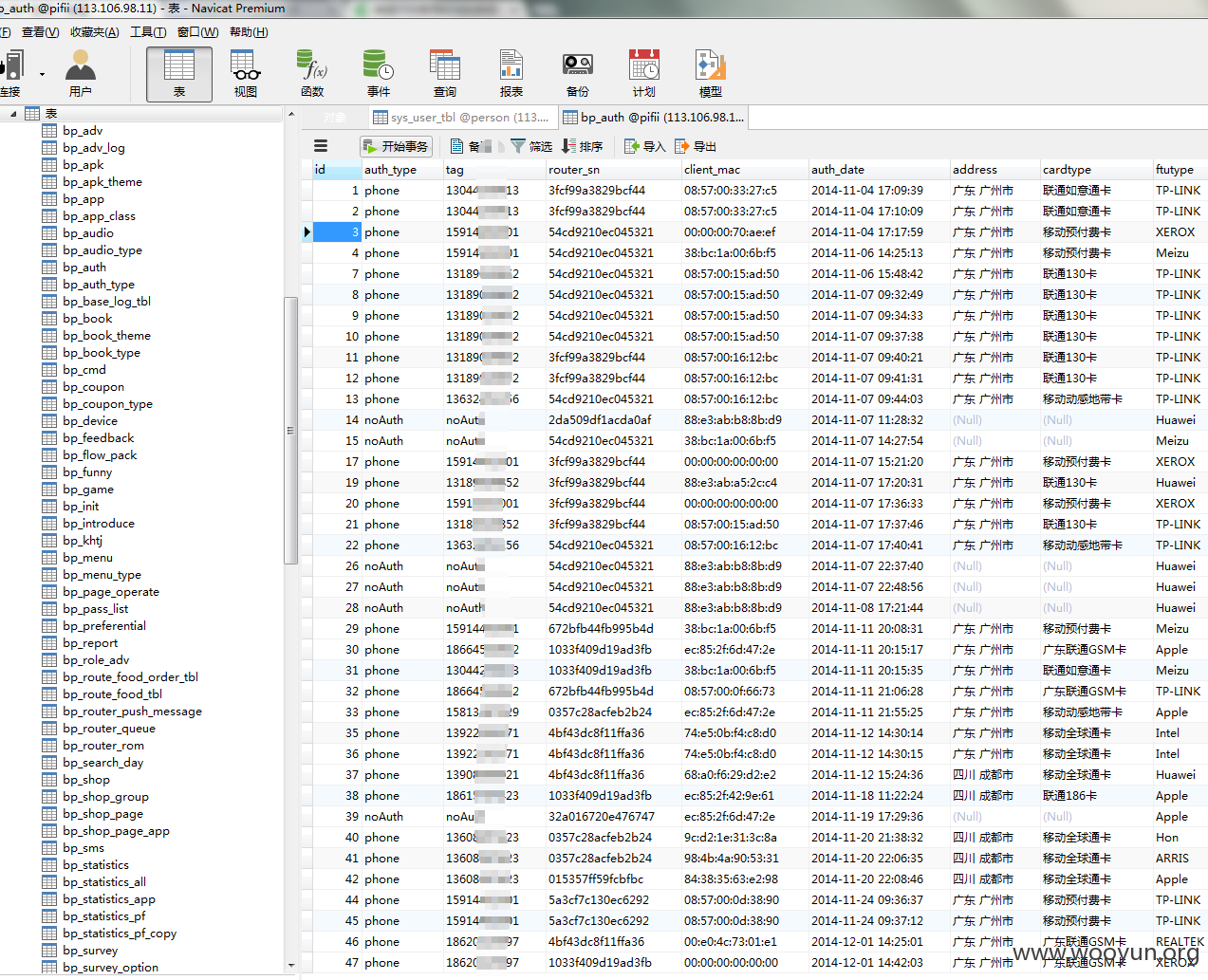
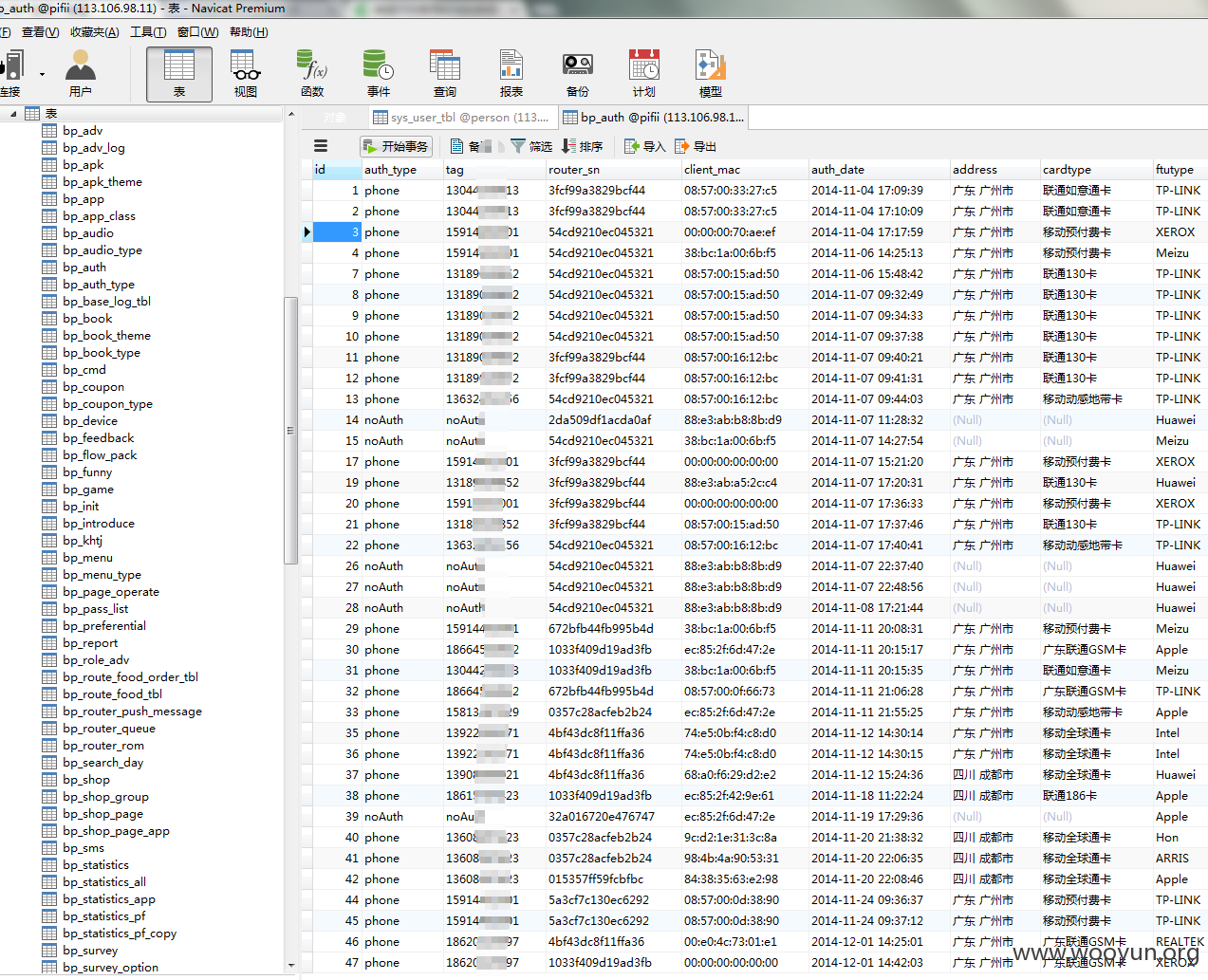
泄漏大量用户信息
http://www.pifii.com/
测试发现,派路由的机房大概IP
电信:
#125.89.70.204
125.89.70.205
125.89.70.206
125.89.70.207
125.89.70.208
125.89.70.209
联通:
#218.104.193.204
218.104.193.205
218.104.193.206
218.104.193.207
218.104.193.208
218.104.193.209
大部分都存在通用密码,root/ZH@id#0427。
可以看出来,已经被入侵过了,上面有msf。
官网服务器也是这个密码,沦陷
泄漏用户数据库信息
同时还存在备份文件下载。
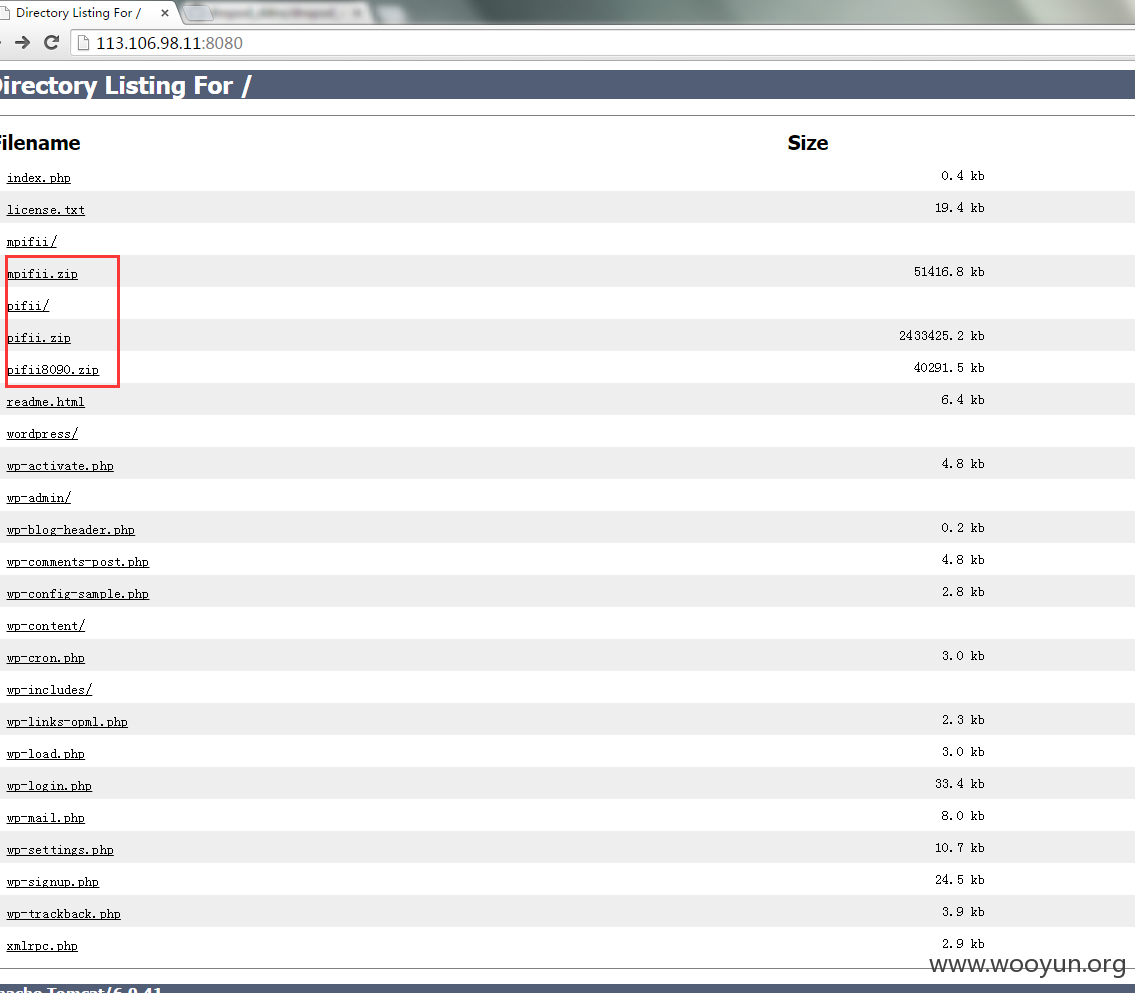
泄漏大量用户信息