十二五国家科技成果万物网络命令执行可getshell
http://www.tgc100.com/portal/news_photoView.action
站点存在Struts2命令执行导致黑客获取webshell权限


中航大学培训管理系统命令执行可getshell
keto.com命令执行可getshell

IBM-GTS智库可命令执行可getshell



http://wenhuayn.com/logon.action


http://cas.sju.js.cn/tyyh/password/findPassword.action

网站:佛山党建
站点存在Struts2命令可getshell
测试入口:http://119.145.135.183:8100/DZJXKH/findPassword.action

http://m.meishangmen.com/user/findPassword.action
站点存在Struts2命令执行,可getshell
http://hb-eport.gov.cn/app/pub/user/getPassword.action
命令执行,你懂得

http://cp.haohua.chemchina.com/GetPassword.action
站点存在Struts2命令执行可getshell

http://www.junzilanhr.com/forgetpassword.action
站点存在Struts2命令执行,可getshell

http://www.risechina.com/com/rise/bms/user/userlogin.action
站点存在Struts2命令执行,可getshell

http://www.chinaostrain.com/LMS/portal/ajaxCheckUserPortalLogin.action
站点存在命令执行,可直接getshell

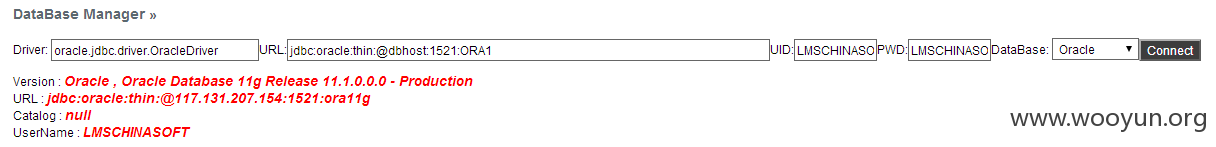
数据库以及默认配置:
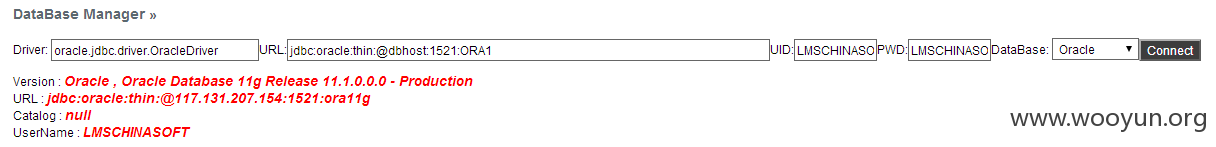
默认配置:
http://dms.leedarson.com:9000/regUserCityAjax.action
站点存在命令执行可getshell

http://dms.leedarson.com:9000/regUserCityAjax.action
站点存在命令执行可getshell