漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2014-066550
漏洞标题:FengCMS本地文件包含一枚
相关厂商:fengcms.com
漏洞作者: magerx
提交时间:2014-07-01 13:45
修复时间:2014-09-29 18:26
公开时间:2014-09-29 18:26
漏洞类型:文件包含
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2014-07-01: 细节已通知厂商并且等待厂商处理中
2014-07-01: 厂商已经确认,细节仅向厂商公开
2014-07-04: 细节向第三方安全合作伙伴开放
2014-08-25: 细节向核心白帽子及相关领域专家公开
2014-09-04: 细节向普通白帽子公开
2014-09-14: 细节向实习白帽子公开
2014-09-29: 细节向公众公开
简要描述:
LFI
详细说明:
条件:PHP<5.3.4
/app/controller/searchController.php:
上面我们让post为空,$_GET['tags']不为空,$_GET['project']可控,接着看display()
/system/core/controller.php:27行
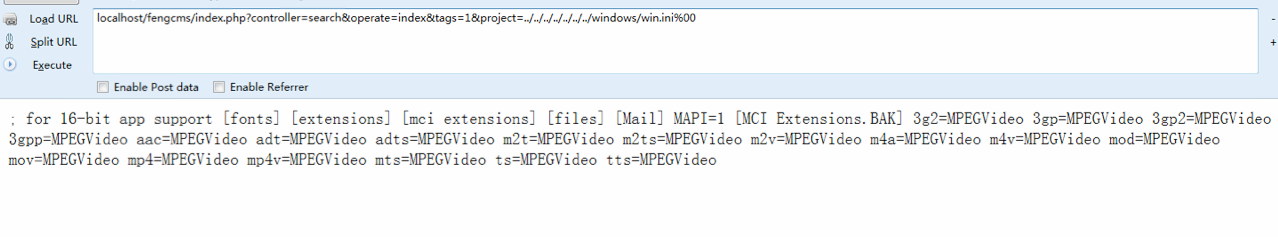
$path直接被include,(由于程序自带stripslashes前面提到过)%00截断,LFI有了
poc:
漏洞证明:
修复方案:
v
版权声明:转载请注明来源 magerx@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2014-07-01 13:47
厂商回复:
非常感谢乌云平台,为我们查找到了安全漏洞!我们一定再接再厉,做好我们的产品的安全工作!
最新状态:
暂无